Legorum.exe
With digital threats constantly evolving, users must remain vigilant against sophisticated attacks that compromise personal data and system integrity. One such threat tracked as Legorum.exe, operates as a loader malware, serving as a gateway for even more threatening infections. Its presence on a system signals a significant security breach, exposing victims to trojans, ransomware, and other harmful programs. Understanding its methods and potential impact is crucial for maintaining cybersecurity.
Table of Contents
Legorum.exe: A Silent but Evil Infiltrator
Legorum.exe is not just a single harmful program but a delivery mechanism for more advanced cyber threats. As a loader, its primary purpose is to install additional unsafe files, opening the door for further system compromise. Users often unknowingly introduce this malware to their devices through phishing emails, software bundles, and unverified downloads, making it a severe risk for anyone engaging with questionable online content.
Once installed, this loader operates silently in the background, connecting to remote servers controlled by cybercriminals. These servers issue commands that direct Legorum.exe to download, install, and execute harmful files without the victim’s knowledge. Because of its stealthy nature, users may not realize their device is compromised until severe issues—such as system slowdowns, data theft or even ransomware attacks—begin to manifest.
The Hidden Dangers of Legorum.exe
One of the most concerning aspects of Legorum.exe is its ability to facilitate multiple forms of cybercrime. By deploying Trojans and spyware, it enables hackers to steal sensitive data, including financial details and login credentials. Such information is often sold on underground marketplaces or used for unauthorized transactions and identity fraud.
This malware also possesses remote execution capabilities, meaning attackers can issue commands to the infected system from afar. Through this method, cybercriminals may trigger additional infections, manipulate system settings, or exfiltrate stolen information to external servers. This level of control places affected users at risk of constant surveillance and unauthorized access to their personal files.
The Persistence Mechanisms of Legorum.exe
Unlike some threats that simply infect a system and leave a noticeable impact, Legorum.exe is designed to remain hidden and difficult to remove. To achieve this, it modifies system configurations, ensuring that it automatically launches upon startup. This persistence mechanism means that even if users attempt to restart their devices, the malware continues to operate undetected.
Furthermore, Legorum.exe employs evasion techniques to bypass security software, making detection and removal particularly challenging. It may disguise its processes under legitimate system names, inject its code into trusted applications, or even disable certain antivirus functions to extend its lifespan on the system.
False Positive Detections: When Do They Occur?
While security programs are crucial in identifying and neutralizing threats like Legorum.exe, they may occasionally flag legitimate files as threats—a scenario known as a false positive detection. This occurs when an anti-malware mistakenly classifies a benign program as harmful due to similarities in behavior or code structure. Some software tools rely on heuristic analysis, which examines how a program behaves rather than its exact signature. If a legitimate application shares traits with known threats, it may be incorrectly labeled as unsafe.
False positives are more common when security programs detect new or modified applications that have not yet been cataloged in their databases. Additionally, compressed or encrypted files can sometimes be misidentified as potential threats, especially if their internal structure resembles that of threatening software. While false positives can be inconvenient, they highlight the importance of regularly updating security software to improve detection accuracy.
Why Detecting Legorum.exe Means Immediate Action is Necessary
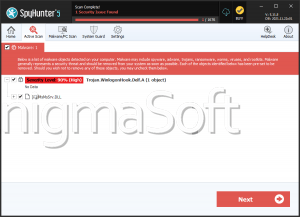
Unlike harmless false positive detections, a legitimate Legorum.exe infection is a serious issue. If security software identifies this loader on a system, it means the device is already compromised. At this stage, the malware has likely downloaded and executed additional threats, making it crucial for users to respond promptly. Allowing the infection to persist increases the risk of data breaches, financial loss, and further system instability.
Given its stealthy nature and ability to escalate cyberattacks, Legorum.exe represents a significant security concern. Recognizing its presence and understanding the risks it poses are essential steps in safeguarding personal and professional digital environments.