LeChiffre Ransomware
The LeChiffre Ransomware is a ransomware Trojan that is used to take money from computer users. The LeChiffre Ransomware is particularly threatening because it targets businesses using spam emails. The LeChiffre Ransomware was recently responsible for attacks on three Indian banks, causing millions in monetary losses. Among the victims of the recent the LeChiffre Ransomware attacks was also an important pharmaceutical company and numerous individuals.
Table of Contents
Recent LeChiffre Ransomware Attacks in India
PC security researchers observed recent LeChiffre Ransomware attacks in early January of 2016 in India. These attacks targeted Indian companies. Several variants of the LeChiffre Ransomware were involved in these attacks, which are customized depending on the target of the attack. There are several characteristics of the LeChiffre Ransomware that are specific to this attack, despite that most ransomware Trojans are nearly identical in their approach. The LeChiffre Ransomware requires computer users to execute it manually. The LeChiffre Ransomware attack is delivered by infiltrating the companies' networks and then escalating this attack to the other computers on the affected network by using unprotected Remote Desktop ports. Using this access, con artists deliver the ransomware by downloading it from the remote server and then clicking on it after it has been downloaded to start the encryption of the victim's files. Rather than convincing computer users to click on the ransomware file through social engineering or using other threat to deliver it, the fraudsters will go into the affected computers and execute the threat directly.
How the LeChiffre Ransomware Carries out Its Attack
The LeChiffre Ransomware uses AES encryption. The LeChiffre Ransomware encrypts the first and final 8192 bytes of each targeted file. The LeChiffre Ransomware appends the encryption key to the file. Taking a look at the LeChiffre Ransomware, it seems that this threat is written in Delphi and s almost certainly Russian in origin. Curiously, it seems that the LeChiffre Ransomware is not implemented very professionally. Unlike most ransomware Trojans, the LeChiffre Ransomware does not contain countermeasures to prevent PC security researchers from studying it in a sandbox or virtual environment. This has allowed PC security researchers to observe this threat in detail. This, combined with the method in which the LeChiffre Ransomware is executed on its victims' computers, has made malware analysts suspect that the people responsible for the LeChiffre Ransomware attacks are not particularly experienced. Apart from the poor encryption (not encrypting the entire file, and appending the encryption key to the files), the LeChiffre Ransomware communicates with its victims using email rather than more advanced, and anonymous methods.
Despite Its Poor Implementation, the LeChiffre Ransomware Has Caused Millions in Losses
The LeChiffre Ransomware asks computer users to contact its authors using an email address contained in its message. The LeChiffre Ransomware demands the payment of a 1 Bitcoin ransom. Currently, the average price for 1 Bitcoin is between $300 and $400 USD. According to news reports from India, there are so many computers that have been infected with the LeChiffre Ransomware that currently the amounts demanded by the LeChiffre Ransomware add up to millions of US dollars. However, ransoms have mostly not been paid, except for some top executives at the targeted banks and pharmaceutical companies.
Protecting Your Computer and Network from the LeChiffre Ransomware
The best way to protect yourself and your company from the LeChiffre Ransomware is to secure your network. A strong security software, firewall, and anti-spam software are crucial tools when combating ransomware infections. Ensure that there is a company culture that includes secure browsing practices to prevent these kinds of threats from entering a computer. Maintain security back-ups of all files on an external memory device or the cloud on a different network.
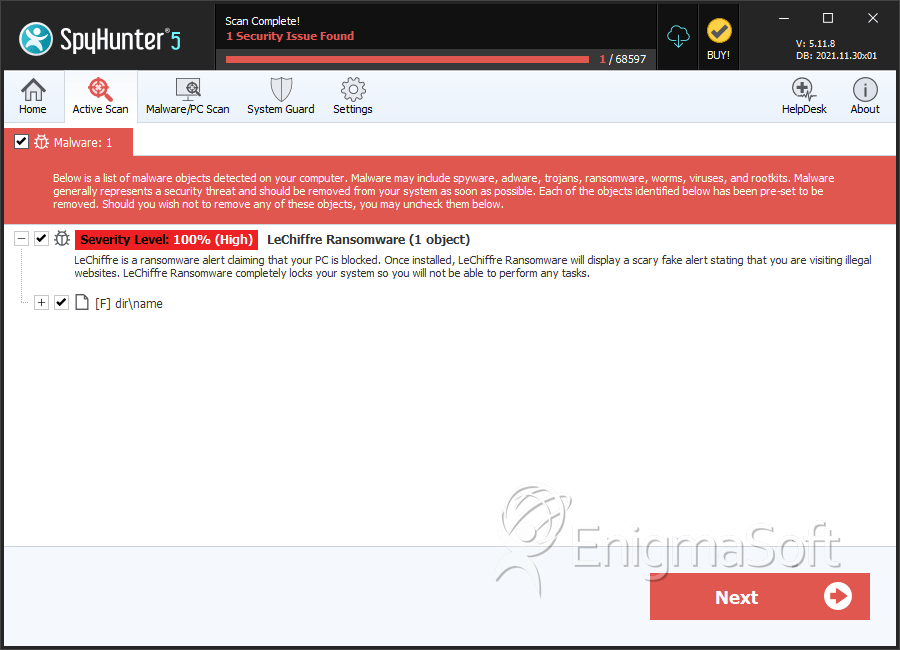
SpyHunter Detects & Remove LeChiffre Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | name | 4523ccfd191dcceeae8e884f82f5c7ad | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.