Labour Ransomware
Ransomware continues to be one of the most pervasive threats in the cybersecurity landscape, with new variants emerging regularly. One such variant that has recently gained attention is the Labour Ransomware. This threatening software encrypts a victim's files, appending the file extension '.labour' to each affected file, and demands a ransom for their decryption. Here's an in-depth look at how the Labour Ransomware operates, its impact, and steps to take if your system is infected.
Table of Contents
How the Labour Ransomware Works
- Infection Vector: The Labour Ransomware typically spreads through phishing emails, fraudulent attachments, compromised websites or exploit kits that abuse system vulnerabilities. Users may inadvertently download the malware by clicking on a fraudulent link or opening an infected attachment.
- Encryption Process: Once executed on the victim's system, the Labour Ransomware begins encrypting a wide array of file types. Common targets include documents, images, videos, databases and other important files. Each encrypted file is appended with the '.labour' extension, making it easily identifiable.
- Ransom Note: As soon as the encryption process is complete, the ransomware generates a ransom note named '.README.txt'. This note is typically placed in every directory containing encrypted files. The displayed note includes instructions on how to contact the attackers to recover the encrypted files. The provided contact address is bfe1234@yahoo.com.
- List of Encrypted Files: The ransom note often contains a list of files that have been successfully encrypted. This is intended to demonstrate to the victim the extent of the damage and to pressure them into complying with the ransom demands.
What to Do If Infected by the Labour Ransomware
Being infected by ransomware can be a stressful and challenging experience. Here are the steps you should follow to mitigate damage and potentially recover your files:
- Disconnect from the Network: Immediately unplug your computer from the Internet and any local networks to avert the ransomware from spreading to other devices.
- Do Not Pay the Ransom: Cybersecurity experts generally advise against paying the ransom. Paying is not a guarantee that you will receive the decryption tool and may encourage the attackers to target others.
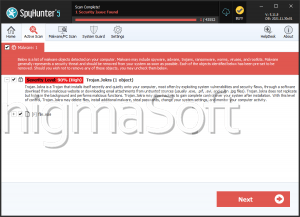
- Identify the Ransomware: Determine the type of ransomware that has infected your system. This information can be helpful in finding potential decryption tools.
- Report the Attack: Report the ransomware attack to local law enforcement and cybersecurity organizations. This can help authorities track ransomware trends and potentially apprehend the perpetrators.
- Restore from Backups: If you have recent backups of your files, you can restore your system to a state before the infection. Ensure that the backups are clean and not infected by the ransomware.
- Seek Professional Help: Consult with cybersecurity professionals who can assist with ransomware removal and data recovery. They can also help secure your system against future attacks.
- Use Decryption Tools: Check reputable sources for decryption tools. Some cybersecurity firms and organizations release free decryption tools for certain types of ransomware. Ensure the tools are from trusted sources to avoid further infections.
- Strengthen Security: After dealing with the ransomware, take steps to strengthen your system's security. This includes updating all software, using strong and unique passwords, enabling multi-factor authentication and educating users about phishing attacks and safe browsing practices.
Preventive Measures
To protect against ransomware like Labour Ransomware, consider the following precautionary measures:
- Routine Backups: Regularly back up your important data to an external drive or cloud storage. Ensure that backups are not connected to your main network to avoid infection.
- Security Software: Use reputable anti-malware software to protect your system from threats. Keep the anti-malware software updated to the latest versions.
- Update Systems: Regularly update your operating system, software, and applications to patch vulnerabilities that ransomware might exploit.
- Email Caution: Be cautious with email attachments and links. Verify the sender's authenticity before opening attachments or clicking links.
- User Education: Educate users about cybersecurity best practices and the dangers of ransomware. Awareness is key to preventing infections.
The Labour Ransomware is a threatening and disruptive program that can cause significant data loss and operational downtime. By understanding how it operates and knowing the steps to take if infected, you can better protect your machine and mitigate the impact of an attack. Always prioritize prevention through regular backups, robust security measures, and ongoing user education to defend against ransomware and other cyber threats.
The ransom note displayed by the Labour Ransomware reads:
'Hello, all of your files have been encrypted.
don't worry you can recover everything, just contact me from the following maill
bfe1234@yahoo.com
you will have to send me your id (-) and your private ip (10.0.1.6).a copy of your important files has been sent to me and if you take a long time to pay
feel free that I will leak data and intimate files on deep web forums.the following list of files have been successfully encrypted:'