Kriptor Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | July 27, 2022 |
| OS(es) Affected: | Windows |
The Kriptor Ransomware threat can be used by cybercriminals in attacks targeting the data of their chosen victims. The malware is capable of initiating an encryption routine utilizing a sufficiently strong cryptographic algorithm. As a result of the threat's actions, affected users will be unable to access most of their data, including databases, archives, documents, PDFs, pictures, photos and more.
The '.Kriptor' extension will be appended to the names of the process files. Victims also will notice that their normal desktop background has now been changed to a new image provided by the threat. In addition, a text file named 'read_it.txt' will appear on the desktop of the breached device. The file contains a ransom note with the demands of the attackers.
Table of Contents
Ransom Note’s Overview
The ransom-demanding message states that the cybercriminals spreading the Kriptor Ransomware are accepting payments in Bitcoin only. However, to receive any additional details, victims are instructed to establish contact with the hackers via their two email addresses - 'leljicok@gmail.com' and 'kkizuko@yandex.com.' As part of their message, users can attach 3 encrypted files. The threat actors are supposed to unlock the received files for free.
The full text of the ransom note dropped by Kriptor Ransomware is:
'Don't worry, you can return all your files!
All your files like documents, photos, databases and other important are encrypted
What guarantees do we give to you?
You can send 3 of your encrypted files and we decrypt it for free.
You must follow these steps To decrypt your files :
1) Write on our e-mail :leljicok@gmail.com ( In case of no answer in 24 hours check your spam folder
or write us to this e-mail: kkizuko@yandex.com)
2) Obtain Bitcoin (You have to pay for decryption in Bitcoins.
After payment we will send you the tool that will decrypt all your files.)'
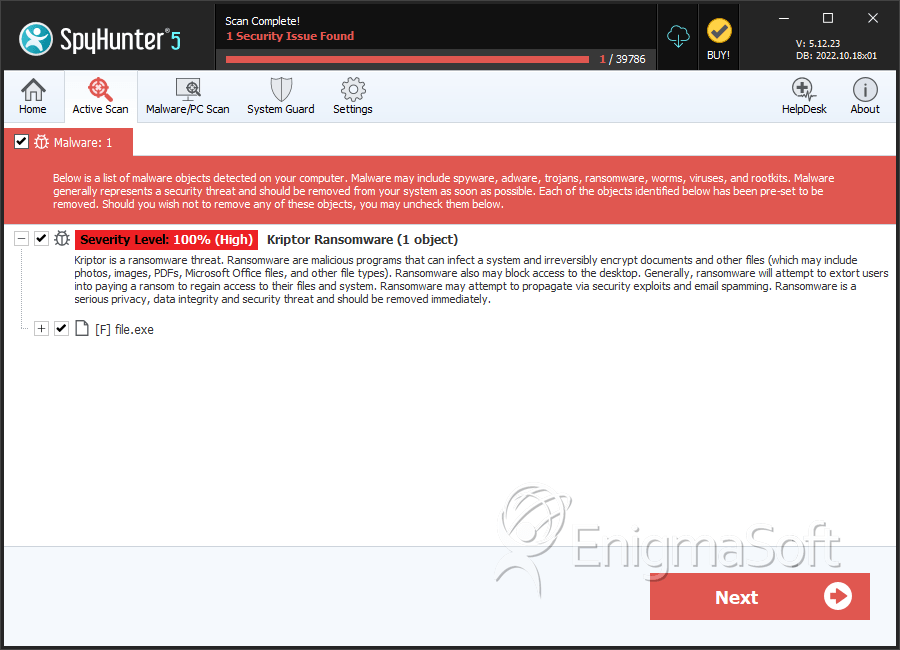
SpyHunter Detects & Remove Kriptor Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 104b8a1e6f7cf47de17db83210ab76a4 | 2 |

