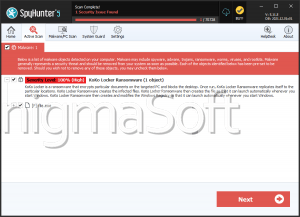
Koko Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 62 |
| First Seen: | May 1, 2017 |
| Last Seen: | September 11, 2021 |
| OS(es) Affected: | Windows |
Dealing with the consequences of a Koko Ransomware attack can be a very challenging task due to this threat’s ability to encrypt files and make their contents inaccessible. Reverting the encryption is impossible without acquiring the unique decryption key that the Koko Ransomware uses for each victim. Unfortunately, this key piece of information is stored on the server of the threat’s operators, and they will not give it away unless they receive fair Bitcoin compensation.
The Koko Ransomware may be Spread via Fake Emails and Downloads
The Koko Ransomware’s authors may use several propagation channels to ensure that their threatening application will reach as many users as possible – phishing emails with bogus attachments, pirated software, fake downloads or fake software updates and patches. The Internet is full of potentially harmful applications so that we advise you to be very careful about the content you browse and download. In addition to this, you should always make sure to have backup protection in the form of a reputable anti-virus engine.
If the Koko Ransomware is not stopped on time, it may cause potentially irreversible damage to your file system. The ransomware encrypts text files, documents, Adobe projects, archives, pictures, and many other files to make the life of the victim as difficult as possible. After this, it drops a ransom note, which contains a short message from the attackers. The message is found in the file ‘
Cooperating with Koko’s Authors Is Out of the Question
Naturally, the cybercriminals behind the Koko Ransomware assure their victim that there is no way to recover the files via free means. They offer a solution that can be acquired by paying some Bitcoin to a wallet address they will specify. However, we would not advise you to try to cooperate with the Koko Ransomware’s operators because there is no guarantee that they are trustworthy. Many ransomware victims were tricked out of their money when they opted to pay, and it would not be a surprise if the Koko Ransomware’s operators have the same plan.
If you suspect that your computer’s files have been damaged by the Koko Ransomware, then we recommend using a reputable anti-virus product to eliminate the infection, and then look into data recovery software and techniques.