Kiss Ransomware
Ransomware threats have been plaguing the Internet for years now, and we will likely not see the end it any time soon. File-locking Trojans are easy to distribute and are one of the most vicious threats, which almost always guarantee destruction to the victim. Users who do not have an anti-malware tool installed and fail to update all their software regularly are the ones that are most vulnerable to ransomware threats. One of the most recently uncovered data-encrypting Trojans has been dubbed Kiss Ransomware. This threat does not appear to belong to any of the popular ransomware families.
Propagation and Encryption
It is likely that bogus pirated copies of legitimate applications, mass spam email campaigns, malvertising operations, and fraudulent application updates may be some of the infection vectors employed in the spreading of the Kiss Ransomware. If this nasty threat infiltrates a PC successfully, it will begin looking for the file types, which is programmed to target. This means that it is likely that most of the data on the victim's computer will be locked – audio files, images, documents, databases, archives, videos, presentations, spreadsheets, etc. After applying its encryption algorithm and locking all the targeted files, it will become evident that the Kiss Ransomware also alters the names of the affected files. This ransomware threat adds a new extension to the locked files using a certain pattern - '[id-
The Ransom Note
In the next step of the attack, the Kiss Ransomware will drop a ransom note on the user's desktop. The note’s name is ' %$ BACK FILES !#.html.’ In the note, the authors of the Kiss Ransomware demand that the victim gets in touch with them via email – ‘decodor@airmail.cc.' Usually, authors of ransomware threats ask their victims to contact them and then they would explain to the user what has happened with their files and how to buy a decryption key. Since payment is often required in the shape of Bitcoin, attackers are usually prepared with instructions for the victim on how to obtain Bitcoin and how to complete the transaction with them so that they would supposedly send the victim the decryption key they need.
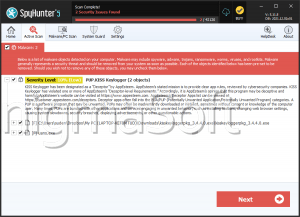
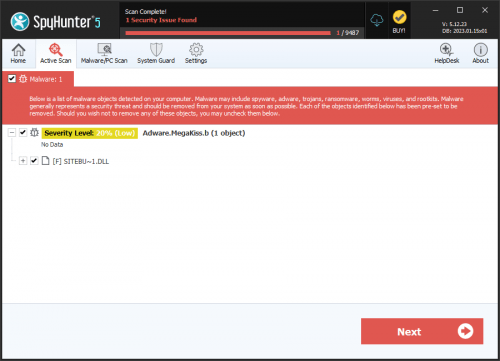
However, this is not a safe approach, as cybercriminals tend to lie about their intentions. Often, as soon as they get their hands on the victim's cash, they lose all motivation to cooperate, and many users are left empty-handed despite paying up the ransom fee. This is why it is far safer to remove the Kiss Ransomware from your computer with the help of a legitimate anti-malware application.