KillerLocker Ransomware
The KillerLocker Ransomware is a ransomware Trojan that is used to encrypt the victims' files, to obtain the payment of a ransom from the affected computer users. The KillerLocker Ransomware is similar to a known ransomware Trojan, the BitStak Ransomware, and uses the AES-256 encryption to take over the victim's data and make it inaccessible. The KillerLocker Ransomware may be delivered to the victims' computers by using corrupted email attachments, often included in fake email messages from banking institutions, shipping companies or social media platforms. Victims may believe that the email message is legitimate, and open the attached file or click on an embedded link. The KillerLocker Ransomware may be delivered in a variety of file types, including files that are considered legitimate such as PDF, DOCX or XLSX files.
Table of Contents
Beware of the KillerLocker Ransomware Threat, Despite It’s Unsophisticated Appearance
The KillerLocker Ransomware has many superficial features that make it seem like the work of amateurs. However, the KillerLocker Ransomware is a threat that should be taken seriously. The KillerLocker Ransomware begins its attack immediately, as soon as the victim opens the corrupted file that is used to deliver the KillerLocker Ransomware threat. The KillerLocker Ransomware may be delivered in a corrupted executable file named 'the KillerLocker.exe,' which carries out its attack. The KillerLocker Ransomware uses a memory file process that has a random name and scans the victim's computer in search for files with a certain file extension. The KillerLocker Ransomware will search the following directories and encrypt the victim's files:
%USERPROFILE%\Music\
%USERPROFILE%\Videos\
%USERPROFILE%\Pictures\
%USERPROFILE%\Desktop\
%USERPROFILE%\Contacts\
%USERPROFILE%\Searches\
%USERPROFILE%\Favorites\
%USERPROFILE%\Downloads\
%USERPROFILE%\Documents\
%USERPROFILE%\AppData\Roaming\
The KillerLocker Ransomware Seems Designed to Target Portuguese Speakers
The KillerLocker Ransomware encrypts all files in the directories listed above, adding the extension '.RIP' to the end of the encrypted file. The files that have been encrypted by the KillerLocker Ransomware become unreadable and inaccessible without the decryption utility needed to undo the KillerLocker Ransomware's encryption. The KillerLocker Ransomware uses a ransom note that is only available in Portuguese and does not include an English alternative. This makes it clear that the KillerLocker Ransomware is designed to target computer users in this specific geographic area. The KillerLocker Ransomware uses an approach that has been observed in other ransomware Trojans: the KillerLocker Ransomware leaves a decryptor on the victim's computer which receives a message from its Command and Control server when the victim's payment is received. The KillerLocker Ransomware possesses a panel that includes a list of the encrypted files along with a countdown timer to increase pressure on the victim. The KillerLocker Ransomware ransom note includes the picture of a scary clown, to further unnerve victims of this attack.
The following is the text of the KillerLocker Ransomware ransom note:
'Todos os seus arquivos foram criptografados com uma criptografia AES 256 BIT Muito forte.
Realize o pagamento em: 000-00 /00 ate 48 horas
Key [text field] Decrypt files'
Which translated into English, means:
'All your files are encrypted with an AES 256-Bit Very strong cipher.
Perform payment: 000-00 / 00 up to 48 hours
Key [text field] Decrypt files'
The KillerLocker Ransomware may be an Incomplete Ransomware Trojan
It's possible that the KillerLocker Ransomware is still a work in progress. One of the reasons why PC security analysts suspect this is that the KillerLocker Ransomware does not include instructions on how to pay the KillerLocker Ransomware ransom. In fact, it is possible that these con artists don't even have a decryptor in place, making it a bad idea to contact them for payment instructions. Rather, computer users are strongly advised to take preventive steps, mainly through the use of a reliable backup method to ensure that all files are properly backed up. This way, computer users can quickly recover from a KillerLocker Ransomware attack by simply restoring the affected files from a backup after removing the KillerLocker Ransomware threat.
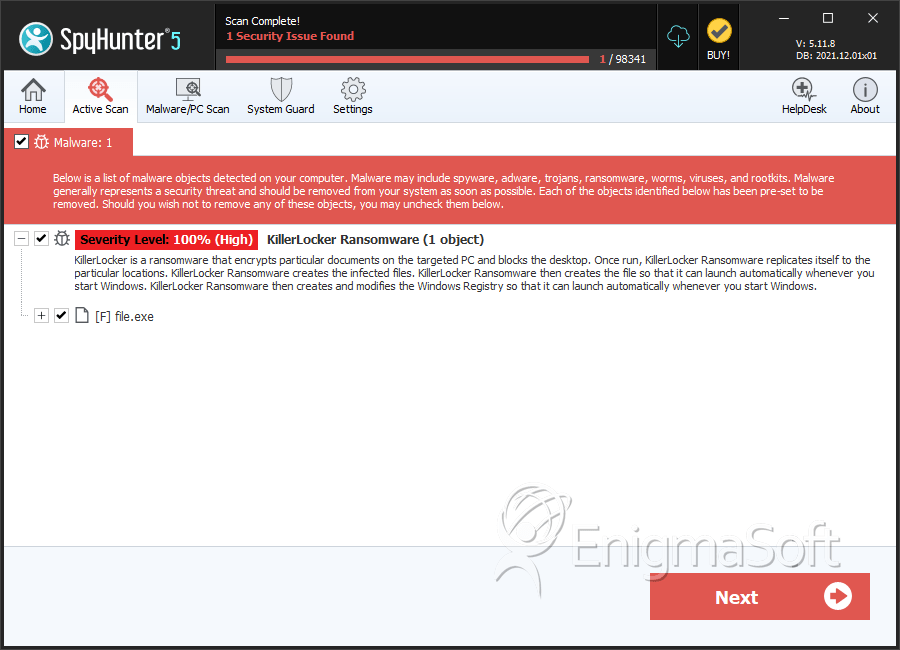
SpyHunter Detects & Remove KillerLocker Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | a802aae121fb19bd185e736ffffcbe46 | 0 |
| 2. | file.exe | d704f3cf861fdf54bcf2beba24dea0f4 | 0 |
| 3. | file.exe | 7afa1f01d6379816b3804eaf5e6c947e | 0 |

