Kelihos
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
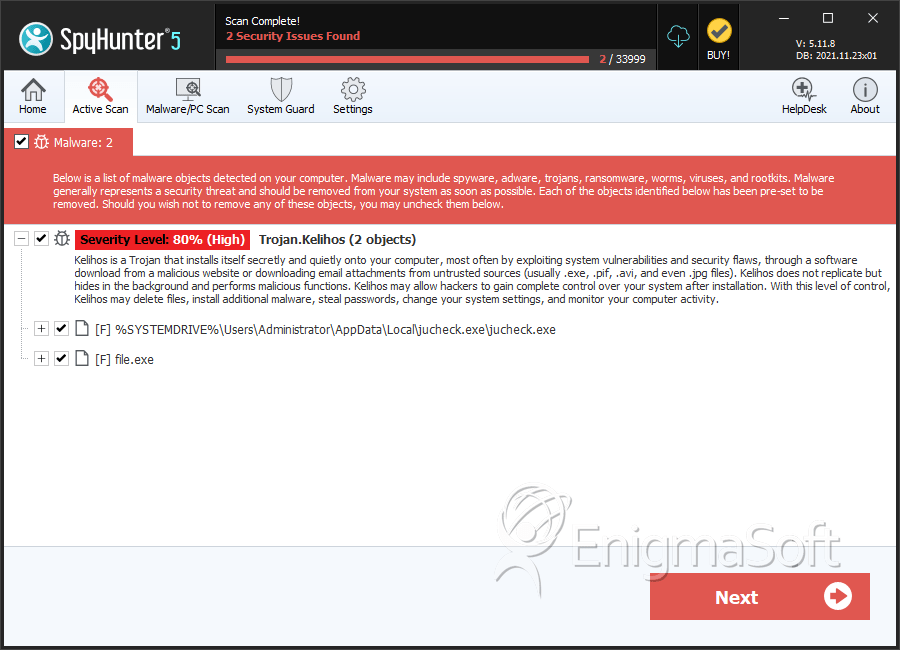
| Threat Level: | 80 % (High) |
| Infected Computers: | 33 |
| First Seen: | February 15, 2011 |
| Last Seen: | October 30, 2022 |
| OS(es) Affected: | Windows |
The Kelihos botnet was shut down effectively by Microsoft in September of 2011. Like most botnets, the Kelihos botnet was integrated by "zombie" computer systems linked through an automated remote access tool, installed with the aid of Trojans. The Kelihos botnet, which included more than 41 thousand machines, is also known as Waledac 2.0. This zombie network was capable of sending out about 3800 million spam email messages every single day. While Kelihos botnet is not the biggest botnet to have ever been shut down, the Kelihos botnet case is notable, because it is the first time that a guilty party has been identified. Legal action can now be taken against an individual.
According to Microsoft, Dominique Alexander Piatti from the Czech Republic used the free service dotFREE Group to operate and control the Kelihos botnet, mainly through "cz.cc" domains. These domains have long been under the scrutiny of PC security researchers, because they have been associated with the recent wave of Mac-specific rogue security programs. In fact, Google temporarily blocked all "cz.cc" addresses because of their propensity for hosting malware.
The lawsuit also includes 22 other individuals, which have yet to be identified. In July of 2011, Microsoft offered a reward of 250 thousand dollars in exchange for any information leading them to the individuals responsible for the Rustock botnet, a huge botnet that Microsoft was able to take down in March of 2011. Almost half of the entire world's spam email was sent by Rustock , which was able to send up to 44100 million spam email messages every single day. Repeating their successful formula from the Rustock case, Microsoft was able to take out the Kelihos botnet by disabling the domains that were responsible for sending out instructions to all of the infected computers in the Kelihos botnet.
On September 22, 2011, Microsoft asked for a temporary restraining order against Piatti, dotFREE Group and the non-identified individuals, allowing Microsoft to disable the connections between the Kelihos botnet and the zombie machines. Some of the cz.cc domains are being used for legitimate businesses, which will be restored through a joint effort between Microsoft and Piatti himself. Much of the code used in the Kelihos botnet was passed on from the Waledac botnet, which infected about 90,000 computers and was shut down in 2010. The actions taken against the Kelihos botnet represent an important warning to other computer criminals operating similar networks, especially now that a guilty party has been identified and prosecuted.
SpyHunter Detects & Remove Kelihos
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | jucheck.exe | 0531c8c963c5dada1f2645c33172400f | 5 |
| 2. | file.exe | 0749701c27cde38bdd527830ce465579 | 1 |
| 3. | file.exe | 1a9789a171eb7cd6db376a9d14140945 | 0 |
| 4. | file.exe | 31e7d612a7462228c0180745868ce76b | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.