Keep Calm Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 102 |
| First Seen: | July 18, 2017 |
| Last Seen: | August 4, 2021 |
| OS(es) Affected: | Windows |
The Keep Calm Ransomware uses a Custom AES encryption algorithm to encrypt its victims' files, and take them hostage. Once the victim's files are encrypted, the Keep Calm Ransomware demands a ransom of 0.1 BTC (approximately $250 USD) in exchange for the decryption key needed to recover the affected files. The Keep Calm Ransomware is based on EDA2, an open source ransomware platform that has been available to the public since May 2016. EDA2 has been the basis for countless ransomware Trojans since its release, including the Keep Calm Ransomware itself. The Keep Calm Ransomware was first observed on July 18, 2017, and was seen delivered as an attachment in spam email messages, as well as disguised as a serial number generator for illegally copied software.
Table of Contents
How to Keep Calm Having Your Crucial Files Unaccessible?
The Keep Calm Ransomware will change the victim's Desktop image during its attack so that it will display an image of a pirate flag, as well as a ransom note that may be contained in a text file also delivered to the victim. The Keep Calm Ransomware's desktop image includes the phrase 'Keep Calm and Recover Your Files.' Regretfully, due to the strength of the encryption method used by the Keep Calm Ransomware in its attack, it is not possible to restore the files encrypted by the Keep Calm Ransomware attack through brute force decryption.
The Keep Calm Ransomware Ransom Note and Encryption Process
In its attack, the Keep Calm Ransomware will use a strong encryption algorithm to make the victim's files inaccessible. The files encrypted by the Keep Calm Ransomware attack will be marked with the file extension '.locked' that it will add to the end of each file's name. The Keep Calm Ransomware will target the following file types for encryption during its attack:
.3df8, .3gp2, .accdb, .adpb, .amxx, .ascx, .ashx, .asmx, .bmp, .cctor, .ctor, .ddcx, .disk, .divx, .djvu, .docm, .docx, .dotm, .dotx, .exe, .exif, .gthr, .gzig, .html, .indd, .itdb, .java, .jfif, .jiff, .jpeg, .mbox, .mpeg, ,pdf, .potm, .potx, .ppsm, .ppsx, .pptm, .pptx, .rsrc, .shar, .tax2013, .tax2014, .tbz2, .text, .thmx, .upoi, .wave, .wdgt, .wma, .wmdb, .wmmp, .xlam, .xlsb, .xlsm, .xlsx, .xltx, .xlwx, .xvid, .zipx.
After encrypting the victim's files, the Keep Calm Ransomware will download and display a ransom notification, warning the victim of the attack and demanding the payment of a ransom. The full text of the Keep Calm Ransomware ransom notification reads as follows:
'YOUR PC HAS BEEN INFECTED
Hello,
+We are the only ones in the world that can provide your files for you!
+When your PC was hacked, the files were encrypted and sent to a server we control!
+You must send 0.1 BTC about 250 USD to
15VUKaBP5YbNiKDhntf5FPAzzqJ9HYieEq
+Within 1 week from now to retrieve your files and prevent them from being leaked!
+When you have sent payment, please send email to luisa91@you-spam.com with:
1) Date Transaction
2) PC's Name
3) Email to send you the KEY
+Once we confirm the transaction, we'll send email with the key and the process to decrypt all your files
+Check your spam looking for Email Subject: AES Key lucky guy!
+You can purchase BITCOINS from many exchanges such as:
https://www.bitstamp.net/
https://www.bitfinex.com/
https://www.coinbase.com/
https://localbitcoins.com/
or google for your country
*We are business people and treat customers well if you follow what we ask
*Remember your email is one-way, so don't do anything stupid
*And please don't waste time trying to decrypt with some local service, without the key is impossible, we use AES encryption
Thank you for your cooperation
Goodbye!'
Dealing with the Keep Calm Ransomware
The best protection against ransomware like the Keep Calm Ransomware is to have file backups. If computer users have backup copies of the encrypted files, then the con artists lose any power over the victim that allows them to demand a ransom payment. Apart from file backups, PC security analysts advise computer users also have a reliable, fully updated security application.
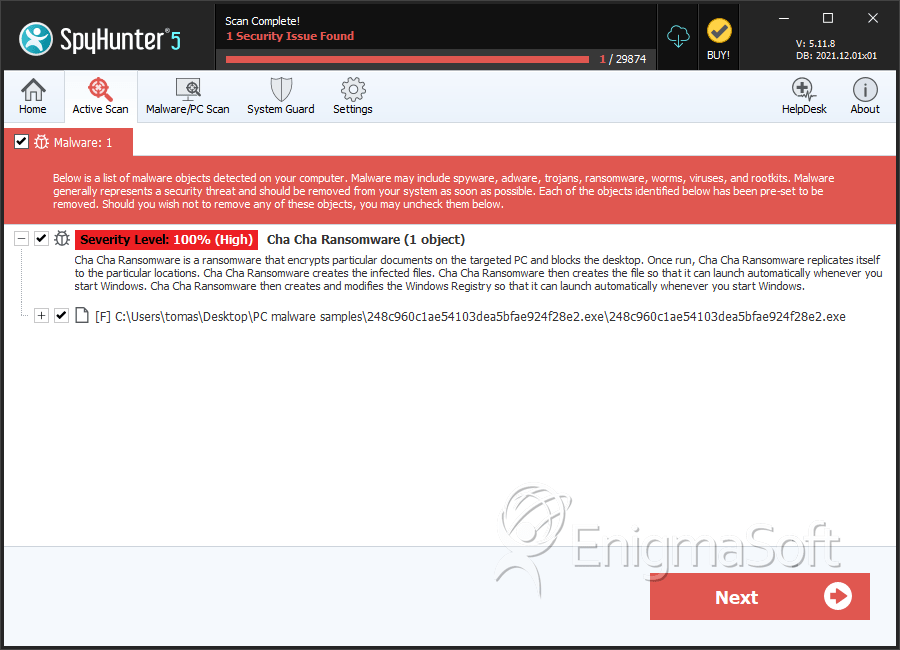
SpyHunter Detects & Remove Keep Calm Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 248c960c1ae54103dea5bfae924f28e2.exe | 248c960c1ae54103dea5bfae924f28e2 | 12 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.