KCVY OSLOCK Ransomware
Cybercriminals are constantly refining their tools, making it essential for users to protect their devices against evolving threats. Among the many forms of ransomware, screenlockers represent a particularly disruptive category. They may not always damage files directly, but they can still cause significant distress by preventing access to the entire system. One such threat making the rounds is the KCVY OSLOCK Ransomware, a sophisticated screenlocker that attempts to trick victims into paying large sums of money.
Table of Contents
What is KCVY OSLOCK Ransomware?
KCVY OSLOCK is a screenlocker-type ransomware designed to deny users access to their computers. Unlike data-encrypting ransomware, it does not actually lock or damage files, even though its ransom note claims otherwise. The malware displays a full-screen message that blocks normal use of the device, falsely informing victims that their files have been encrypted.
The ransom note states that victims have 72 hours to pay $5000 in Ethereum (ETH) to avoid alleged file deletion. It also warns against shutting down the system, threatening permanent data loss if the user attempts it. These claims are deceptive, as the ransomware does not modify or encrypt data in any way.
Screenlockers vs. File-Encrypting Ransomware
Ransomware typically falls into two categories:
Screenlockers: Designed to block access to the operating system, forcing the user to pay for system restoration.
File-encrypting ransomware: Capable of encrypting user files in a way that usually cannot be reversed without the attackers' key or tool.
While some screenlockers incorporate encryption, KCVY OSLOCK does not. Instead, it relies on psychological pressure and misinformation to manipulate victims into paying.
Why Paying the Ransom is Risky
Meeting ransom demands is strongly discouraged. There is no guarantee that cybercriminals will restore access or provide an unlocking key after receiving payment. In many cases, victims are left with both financial loss and an unusable system. Additionally, paying ransom supports and finances further criminal operations, fueling the cycle of cybercrime.
For screenlocker infections like KCVY OSLOCK, removal of the malware usually restores system functionality without any need to recover files, since no encryption is involved.
How KCVY OSLOCK and Similar Threats Spread
Like most ransomware, KCVY OSLOCK is distributed using phishing and social engineering tactics. Malicious payloads are often disguised as legitimate files or bundled with cracked software and freeware. Commonly exploited file formats include archives (ZIP, RAR), executables (.exe, .run), documents (Word, PDF, OneNote), and even scripts such as JavaScript.
Infection often occurs through:
- Spam emails with malicious attachments or links
- Trojanized software installers and fake updates
- Peer-to-peer file sharing networks and untrustworthy download sites
- Malvertising campaigns and drive-by downloads
- Illegal software activation tools ('cracks')
Some malware variants may even spread laterally across local networks or through removable storage devices.
Building a Strong Defense Against Malware
Staying safe from ransomware requires a combination of vigilance, good digital habits, and layered security measures. While no strategy is foolproof, the following practices significantly reduce risk:
Maintain Reliable Backups
Store backups in multiple locations, such as external drives kept unplugged when not in use, or on secure remote/cloud servers. This ensures that even if one copy is compromised, others remain safe.
Practice Safe Browsing and Email Habits
Avoid downloading from suspicious websites, resist clicking unknown links, and never open attachments from unverified senders. Treat unexpected emails with caution, even if they appear legitimate.
Use Security Software and Keep Systems Updated
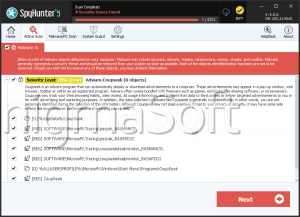
A reputable anti-malware solution provides an additional layer of defense against known threats. Regularly updating operating systems and applications helps close vulnerabilities exploited by attackers.
Disable Macros and Restrict Script Execution
Many malicious files rely on hidden scripts or macros to launch attacks. Disabling these features where possible helps prevent infections.
Stay Informed and Train Users
Awareness is one of the strongest tools against cyberattacks. Individuals and organizations alike benefit from ongoing cybersecurity education, which helps identify and avoid common traps.
Final Thoughts
The KCVY OSLOCK Ransomware highlights how cybercriminals exploit fear and urgency rather than sophisticated encryption. Even though it does not damage files, its ability to lock access and deliver a convincing ransom note makes it a serious threat. Users must remember never to pay ransoms and instead focus on prevention, safe recovery practices, and proactive security measures to protect their systems against both screenlocker and data-encrypting ransomware.