Karo Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 20,969 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 32 |
| First Seen: | June 29, 2017 |
| Last Seen: | May 9, 2025 |
| OS(es) Affected: | Windows |
The Karo Ransomware is a ransomware Trojan that is used to attack computer users by taking their data hostage and then demanding the payment of a ransom from the victim. The Karo Ransomware is mostly delivered using corrupted email attachments, contained in spam email campaigns. These email messages will contain Microsoft Word documents, which use corrupted macros to download and install the Karo Ransomware onto the victim's computer. The Karo Ransomware is a variant of EDA2, an open source ransomware engine that was made available to the public in 2016, allowing con artists to create ransomware Trojans easily and carry out attacks.
Table of Contents
The Bitter Taste of a Karo Ransomware Infection
The Karo Ransomware will scan all of the victim's drives, as well as shared network directories and external memory devices connected to the affected computer. The Karo Ransomware will search for certain file types, belonging to commonly used file types generated by the user (such as media files and documents used by commonly used software). The following are some of the file types that are targeted by a Karo Ransomware attack:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, ,doc, .epub, .docx .fb2, .flv, .gif, .gz, .iso .ibooks,.jpeg, .jpg, .key, .mdb .md2, .mdf, .mht, .mobi .mhtm, .mkv, .mov, .mp3, .mp4, .mpg .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr.
The files encrypted by the Karo Ransomware attack will be marked with the file extension '.ipygh,' making it clear that the affected files were compromised by the Karo Ransomware attack. The Karo Ransomware will deliver its ransom note in a file named 'ReadMe.html,' which contains instructions on how to pay and alerts the victim about the attack. The full text of the Karo Ransomware's ransom note reads:
'YOU HAVE BEEN INFECTED WITH RANSOMWARE
What has happened?
You have been infected with ransomware. All of your files have been encrypted. Which means, you wont be able to open them or view them properly. It does NOT mean they are damaged.
Solution
You will need to decrypt the files, and only we can decrypt your files. So you need to pay us money if you want your files back. Once payment is made, you will be given a special file to run, and once you run that file, everything will get back to normal. All of your files will be unlocked and this ransomware will get removed from your PC.
Payment procedure
Download a special browser called "TOR browser" and then open the given below link. Steps for the same are -
1. Go to https://wwv.torproject.org/download/download-easy.html.en to download the "TOR Browser".
2. Click the purple button which says "Download TOR Browser"
3. Run the downloaded file, and install it.
4. Once installation is completed, run the TOR browser by clicking the icon on Desktop.
5. Now click "Connect button", wait a few seconds, and the TOR browser will open.
6. Copy and paste the below link in the address bar of the TOR browser.
DATAYYYY
Now HIT "Enter"'
7. Wait a few seconds, and site will open
If you have problems dining installation or use of Tor Browser, please, visit Youtube and search for "Install Tor Browser Windows" and you will find a lot of videos.
Pay before its loo late'
Dealing with the Karo Ransomware
Unfortunately, it is not possible to decrypt the files affected by the Karo Ransomware. Because of this, it is crucial to have file backups. Having file backups, computer users can recover their files after a Karo Ransomware attack without having to deal with the people responsible for these attacks or financing further infections and threat development.
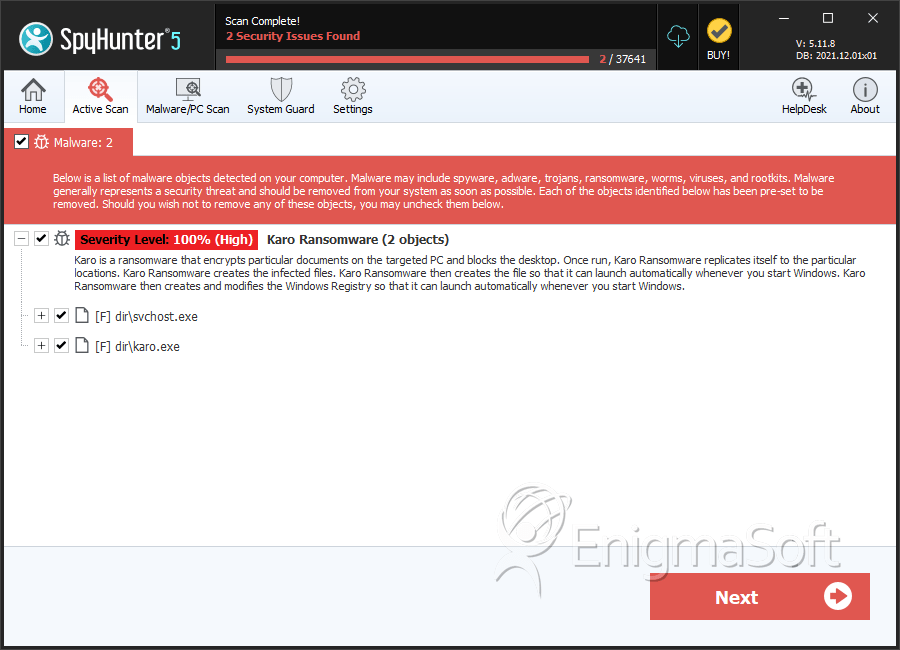
SpyHunter Detects & Remove Karo Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | a9053a3a52113698143a2b9801509c68d0d8b4b8208da453f0974547df0931bc.exe | 43478841baa4b8754f75516220e33ac3 | 9 |
| 2. | 72716d15ea7d118b8c99dbcb15114188abe468718c876ac52b0779161ef7e821.exe | d7c62a22cc1a832ba2ce0bfd1c4f9e9c | 9 |
| 3. | svchost.exe | 4e2273bca8389e2b57077e5e8cbd6f5f | 0 |
| 4. | karo.exe | c2300aac0f22062b057df333b063d253 | 0 |
