Java.Exploit.CVE
Table of Contents
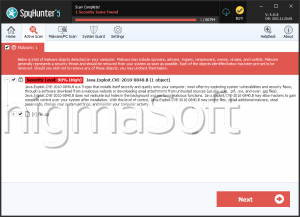
Java.Exploit.CVE – A Java-specific Malware Infection
Java.Exploit.CVE is a malware infection that uses a vulnerability in the Java Runtime Environment to enter and infect a computer system. The CVE-2010-0840 error is a Java vulnerability that has been used to infect computer systems with malware such as Java.Exploit.CVE. There is no need to worry about this online threat. ESG PC security researchers report that a patch has already been released, which fixes this Java security vulnerability. ESG malware analysts recommend updating Java to make sure that you are completely protected from Java.Exploit.CVE and similar threats. Many websites still contain this flaw in their security and may cause unintended Java.Exploit.CVE infections. The Java.Exploit.CVE Trojan horse has been observed in the wild mainly in the fall months of 2011. It is thought that the Java.Exploit.CVE Trojan originated in the Russian Federation, a nation that is well-known for being home to some of the most dangerous bands of computer criminals on the planet. ESG PC security researchers recommend updating Java and making sure that you use strong, reliable and fully-updated anti-malware software.
Java.Exploit.CVE Takes Advantage of a Two-way Street
Many computer users do not realize that whenever you browse the Internet, the flow of information is a two way street. Not only are you reading information on a web page, but your computer browser is interacting constantly, exchanging information with the server hosting the website in question. This is why it is important to realize that, when you are reading a website infected with a security hole associated with the Java.Exploit.CVE Trojan, an exchange of information is actually taking place. The Java error that enables the Java.Exploit.CVE Trojan allows malicious data to stay on your computer system, even after the website in question has been closed. Failing to patch up these security holes will usually lead it to becoming reinfected constantly with the Java.Exploit.CVE Trojan. Hackers use this exploit in order to make the victim's computer system attempt to run a remote executable. This executable causes the victim's computer system to become infected with the Java.Exploit.CVE Trojan, a malicious application that can harm your computer system and steal your private information.
Java.Exploit.CVE is a Silent Infection
One of the most dangerous aspects of the Java.Exploit.CVE Trojan is that Java.Exploit.CVE exhibits almost no symptoms. Unlike other kinds of malware infections, criminals have designed the Java.Exploit.CVE Trojan to remain on your computer system without making its presence known. This malware infection lurks silently on your hard drive, with the capacity to monitor your activities, steal your data or hand over access to a remote party.