ISHTAR Ransomware
The ISHTAR Ransomware is a ransomware Trojan that con artists use to force computer users to pay large amounts of money. Most encryption ransomware Trojans like the ISHTAR Ransomware, take their victims' files hostage by encrypting them with strong encryption algorithms. They then demand that the victim pays a ransom by using some anonymous payment method. The ISHTAR Ransomware targets Russian-speaking computer users, and it is clear that this threat originates from Russia. The ISHTAR Ransomware is being distributed in spam email messages containing a message in Russian and a file named 'Anketa sotrudnikov pretend na povushenie.' Many email messages being used to distribute the ISHTAR Ransomware will pretend to be associated with social media platforms such as Facebook or Twitter. As always, you should avoid opening unsolicited email attachments to avoid threats like the ISHTAR Ransomware.
Table of Contents
The ISHTAR Ransomware Uses Deceiving Methods to Deliver Its Payload
In most cases, the ISHTAR Ransomware is delivered in a file that has its real extension disguised. In many cases, threat creators will use files with two extensions to hide the real nature of the file being distributed. Once the ISHTAR Ransomware is installed on the victim's computer, it will encrypt the victim's files, and identify these files with the prefix 'SHTAR-.' This is a slight difference with many other ransomware Trojans, which tend to add a text string to the end of the file name, as an extension, rather than to the beginning, as is the case with the ISHTAR Ransomware. Regardless of the new name the file receives, files that have been encrypted by the ISHTAR Ransomware will no longer be accessible. This is because the ISHTAR Ransomware uses two strong encryption methods to encrypt both the victim's data and the generated decryption key, making it almost impossible to recover the data without access to a key, which the con artists will hold in their possession. The ISHTAR Ransomware will target a wide variety of file types in its attacks, often preferring media files and documents that would have some value to the computer users. The ISHTAR Ransomware creates a file with the encrypted files, which is named 'ISHTAR.DATA' and a ransom note dropped on the Desktop, named 'README-ISHTAR.txt.' The content of the ISHTAR Ransomware's ransom note is printed below:
'ДЛЯ РАСШИФРОВКИ ФАЙЛОВ ОБРАТИТЕСЬ НА ПОЧТУ youneedmail@protonmail.com
ЛИБО
НА BM-[32 random characters] ИСПОЛЬЗУЯ BITMESSAGE DESKTOP ИЛИ https://bitmsg.me/
-----
БАЗОВЫЕ ТЕХНИЧЕСКИЕ ДЕТАЛИ:
> Стандартный порядок шифрования: AES 256 + RSA 2048.
> Для каждого файла создается уникальный AES ключ.
> Расшифровка невозможна без файла the ISHTAR.DATA (см. директорию %APPDATA%).
-----
TO DECRYPT YOUR FILES PLEASE WRITE TO youneedmail@protonmail.com
OR TO
BM-[32 random characters] USING BITMESSAGE DESKTOP OR https://bitmsg.me/
BASIC TECHNICAL DETAILS:
> Standart encryption routine: AES 256 + RSA 2048.
> Every AES key is unique per file.
> Decryption is impossible without the ISHTAR.DATA file (see %APPDATA% path).'
Recovering from an ISHTAR Ransomware Attack
Victims of the ISHTAR Ransomware attack are urged to pay a ransom of 1 BitCoin, which is approximate $720 USD at the exchange rate at the time of writing this report. PC security analysts strongly advise computer users to refrain from paying the ISHTAR Ransomware's ransom. There is no guarantee that the people responsible for the ISHTAR Ransomware attack will keep their word and restore the victim's files after the victim has paid. However, since may not be possible to decrypt the files affected by the ISHTAR Ransomware, security analysts advise computer users to take preventive measures to become well protected against most ransomware Trojans.
The best method to prevent ransomware Trojan attacks like the ISHTAR Ransomware is to ensure that all files are backed up properly. If backups of the computer user's files exist, then computer users can recover from a threat attack by simply restoring their files from the backup location quickly. A reliable security program and common-sense email handling measures can prevent the ISHTAR Ransomware from entering a computer in the first place.
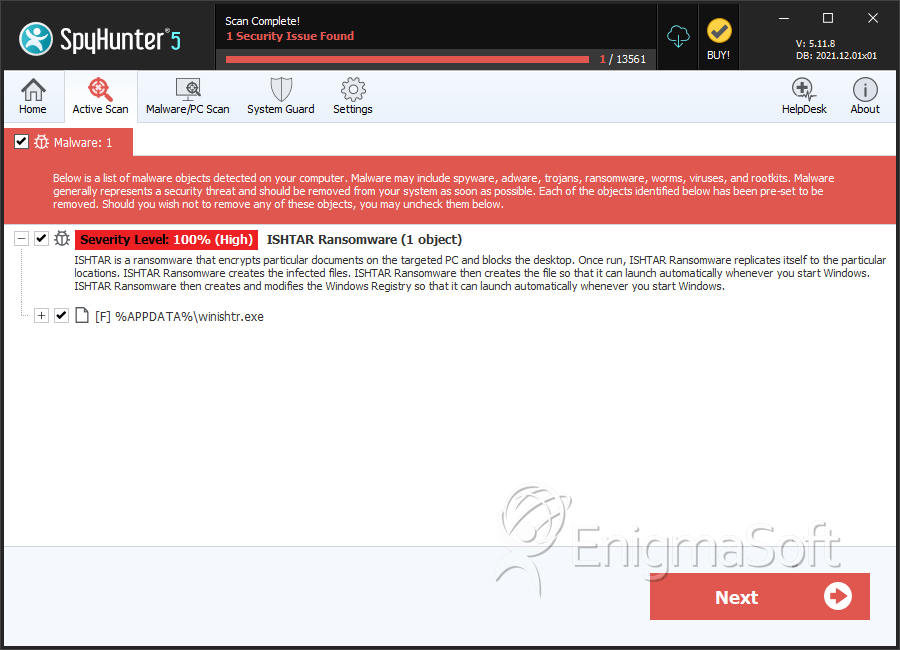
SpyHunter Detects & Remove ISHTAR Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | winishtr.exe | d6955c1047a02fca56b848ddefb35c07 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.