Immigration Ransomware
Protecting personal and organizational devices from malware has become a critical requirement in the modern digital environment. Cyber threats continue to evolve in sophistication, often targeting both individuals and enterprises with techniques designed to encrypt data, disrupt operations, and extort victims. Among these threats, ransomware remains one of the most damaging categories of malicious software. The Immigration Ransomware family represents a recent example of how attackers exploit system weaknesses, encrypt valuable files, and pressure victims into paying for recovery.
Table of Contents
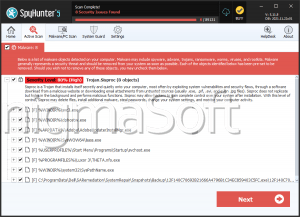
A Closer Look at Immigration Ransomware
Immigration Ransomware is classified as a file-encrypting malware threat. After execution on a compromised system, it initiates a process that searches for accessible files and encrypts them. During this process, the malware modifies the affected filenames by appending the '.eimmigration' extension.
For instance, files such as '1.png' become '1.png.eimmigration,' while '2.pdf' is renamed '2.pdf.eimmigration.' These modifications indicate that the file contents have been encrypted and are no longer accessible in their normal state. Victims attempting to open the files will find that standard applications can no longer read the data.
In addition to encrypting files, the ransomware creates a text document titled 'WHATS_HAPPEND.txt.' This file serves as the ransom note, providing instructions and warnings from the attackers.
Ransom Note Claims and Extortion Strategy
The ransom message attempts to pressure victims through a mixture of technical explanations and threats. According to the note, the attackers claim they identified vulnerabilities in the victim's security infrastructure and exploited them to gain unauthorized network access. After infiltrating the environment, the attackers state that all important files were encrypted but can supposedly be restored using a decryption tool in their possession.
The message also introduces an additional form of extortion. It claims that sensitive files were stolen during the intrusion and warns that the data will be published within 72 hours if the victim does not establish contact. This tactic, commonly known as double extortion, is designed to increase pressure on organizations that may otherwise rely on backups for recovery.
Victims are instructed to contact the attackers through the email address 'nhuvgh@outlook.com.' The note also discourages the use of third-party recovery services, claiming they are either fraudulent or intermediaries that will increase the ransom cost.
File Encryption and the Challenges of Data Recovery
Once Immigration Ransomware encrypts files, access to the data is typically impossible without the specific decryption tool controlled by the attackers. Modern ransomware families commonly employ strong cryptographic algorithms, which makes brute-force decryption unrealistic.
Recovery options are therefore extremely limited. The only reliable way to restore files without cooperating with attackers is by using unaffected backups. If secure backups exist on external storage or remote servers that were not connected to the infected system, data restoration may be possible after the malware is fully removed.
Another important factor is speed of response. Leaving ransomware active on a system increases the risk that it will continue encrypting additional files or spread to other devices connected to the same network. Prompt containment and removal are therefore essential to limit damage.
Common Infection and Distribution Methods
Like many ransomware threats, Immigration Ransomware is not usually delivered through a single channel. Instead, attackers rely on multiple distribution techniques designed to trick users or exploit weak security practices.
Common infection vectors include:
- Misleading emails containing malicious attachments or links
- Technical support scams that persuade users to download malware
- Cracked software, key generators, and illegal activation tools
- Malicious documents disguised as legitimate Office or PDF files
- Files downloaded from peer-to-peer networks or third-party download sites
- Compromised websites, malicious advertisements, and infected USB devices
In many cases, the malicious payload is embedded inside files that appear legitimate. Executables, archives, scripts, and documents may all be used as carriers for ransomware installers.
Strengthening Device Security Against Ransomware
Effective ransomware defense depends on a layered security approach that combines technical safeguards with responsible user behavior. Systems that lack updates, rely on weak security policies, or download unverified software are significantly more vulnerable to attacks such as Immigration Ransomware.
The following practices significantly improve protection against file-encrypting malware:
- Maintain regular backups of important data on remote servers or storage devices that remain disconnected from the main system when not in use
- Keep operating systems and applications fully updated to eliminate vulnerabilities that malware may exploit
- Use reputable security software capable of detecting and blocking ransomware activity
- Avoid opening unexpected email attachments or links from unknown senders
- Download programs only from official or trusted sources, avoiding pirated software and activation tools
- Restrict the use of removable media and scan USB devices before accessing their contents
- Implement strong network segmentation and access controls in organizational environments
Consistent implementation of these practices dramatically reduces the likelihood of successful infection and limits the damage if an attack occurs.
Final Assessment
Immigration Ransomware demonstrates many characteristics typical of modern ransomware operations: strong file encryption, a ransom note with contact instructions, and threats of data exposure designed to force payment. Once the malware encrypts files, recovery without backups becomes extremely difficult.
Preventive security measures remain the most effective defense. Regular backups, cautious handling of emails and downloads, and up-to-date security software form the foundation of strong protection against ransomware threats. In the evolving landscape of cybercrime, proactive defense and user awareness remain essential for safeguarding digital assets.