HTTP Error 401 Invalid Security Token Email Scam
Unexpected emails that demand immediate action are a common tactic used by cybercriminals to manipulate unsuspecting recipients. Messages that claim urgent technical issues or account problems often attempt to create panic so users react without verifying the information. For this reason, it is essential to remain vigilant when dealing with unfamiliar or alarming emails. One such threat is the 'HTTP Error 401 Invalid Security Token' email scam. These messages are part of a phishing campaign and are not associated with any legitimate companies, organizations, or entities.
Table of Contents
A Fake Technical Alert Designed to Create Urgency
The 'HTTP Error 401 Invalid Security Token' emails are crafted to appear like legitimate alerts from an email service provider. They claim that the recipient must complete a sign-in authentication process due to an issue involving an 'HTTP Error 401' and an invalid security token.
According to the message, the problem supposedly occurred because the recipient's email service, such as Outlook, OWA, or a webmail server, has expired or become outdated. The email suggests that access to the mailbox may be disrupted unless the issue is resolved immediately.
To make the message appear convincing, recipients are instructed to follow a link labeled 'Continue' and re-enter their account password. The email claims that completing this step will generate a new security token, automatically update the expired service, and restore uninterrupted access to the mailbox.
In reality, the notification is entirely fabricated and serves only one purpose: to trick recipients into revealing their login credentials.
The Phishing Page Behind the Link
Clicking the link in the message redirects the user to a fraudulent website designed to imitate a legitimate email login portal. The page usually looks professional and may resemble the interface of common email services in order to reduce suspicion.
Victims who enter their email password on this page unknowingly send their credentials directly to cybercriminals. The attackers can then use these stolen details to gain unauthorized access to the victim's email account.
The consequences of such access can be severe. Once an account is compromised, attackers may:
- Search through emails to collect sensitive personal or financial information.
- Send additional phishing messages from the victim's address to contacts.
- Distribute malicious links or attachments using the compromised account.
- Attempt to reset passwords for other services linked to the email account.
Because email accounts often serve as the central hub for password recovery and account notifications, gaining control of one mailbox can open the door to multiple other compromises.
Why This Scam Appears Convincing
Cybercriminals frequently design phishing campaigns to appear technical or system-related because such messages can seem legitimate to many users. By referencing an 'HTTP Error 401' and a supposed invalid security token, the scammers attempt to mimic authentic system alerts.
The message's tone is intentionally urgent and technical. It implies that the recipient must act quickly to prevent losing access to their email service. These tactics encourage users to follow the provided instructions without independently verifying whether the alert is genuine.
In reality, legitimate email providers do not request passwords through external links in unsolicited messages. Any request to re-enter credentials through an email link should be treated as highly suspicious.
Additional Threats Linked to Spam Campaigns
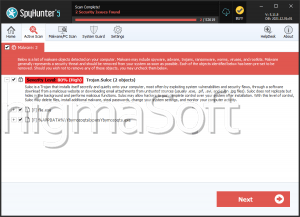
Although the primary goal of this phishing campaign is credential theft, emails of this type can also be used to distribute malicious software. Spam messages often serve as entry points for malware infections.
Common infection methods include:
- Links that redirect users to compromised or fake websites capable of automatically downloading malware or prompting users to install it manually
- Attachments disguised as documents, spreadsheets, PDFs, compressed archives, scripts, or executable files that contain hidden malicious code
- Documents that require additional actions, such as enabling macros, which then trigger the malware installation
Once malware is installed, attackers may gain further control over the device, steal information, or monitor user activity.
Recognizing and Avoiding the Threat
The 'HTTP Error 401 Invalid Security Token' emails are a phishing attempt designed to look urgent and technical in order to trick recipients into revealing their email passwords. Their ultimate objective is to gain unauthorized access to personal accounts.
Messages of this kind should not be trusted. Users are strongly advised to ignore and delete suspicious emails that request login credentials or instruct them to resolve technical issues through unfamiliar links. When there is genuine concern about account access or service status, the safest approach is to visit the official website of the service provider directly rather than following links in unsolicited messages.
Maintaining caution with unexpected emails remains one of the most effective ways to protect personal information, prevent account compromise, and avoid malware infections.