Horros Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | April 11, 2018 |
| Last Seen: | December 5, 2020 |
| OS(es) Affected: | Windows |
The Horros Ransomware is an encryption ransomware Trojan that was first observed in early April of 2018. The Horros Ransomware carries out a typical ransomware attack, encrypting victims' files and then demanding ransom payments in exchange for the decryption key that will be crucial to restore the affected files. Ransomware Trojans like the Horros Ransomware are becoming more common increasingly, and computer users need to take preventive steps to protect their data from this and other threat attacks.
Table of Contents
The Horros Ransomware will Hibernate Your Files
The Horros Ransomware is delivered using spam email messages, but it can be distributed using other methods, such as taking advantage of unsecured RDP connections on the targeted computer. When the victims receive the Horros Ransomware via email, it will arrive in the form of a DOCX file with embedded macros that download and install the Horros Ransomware onto the victim's computer. The Horros Ransomware will use a strong encryption algorithm to make the victim's files completely inaccessible once installed on the targeted computer. The Horros Ransomware will target the user-generated files, which may include photos, music, and databases, while avoiding Windows system files or executable files. These threats do this because they depend on the victim being able to use the affected computer to make a ransom payment and contact the cybercrooks. The following are some of the file types that are commonly targeted in attacks like this one:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
The Horros Ransomware runs as an executable file named 'FileEncrypter.exe,' and the files that are encrypted by the Horros Ransomware attack are easy to recognize because the Horros Ransomware will add the file extension 'horros' to the end of each affected file's name.
The Horros Ransomware Does not Deliver a Ransom Note
The goal of creating ransomware Trojans like the Horros Ransomware is to force computer users to pay large ransoms after taking their files hostage. To do that, these threats deliver a ransom note to the victim's computer. This ransom note will include instructions on how to pay and contact the cybercrooks. Since the Horros Ransomware does not deliver any ransom note or inform a way to contact the cybercrooks, then it is clear that the Horros Ransomware is either still in development or unfinished. However, the Horros Ransomware still carries out an effective ransomware attack that will make the victim's files unusable.
Protecting Your Data from the Horros Ransomware
While it may not be possible to restore the files affected by ransomware attacks like the Horros Ransomware, some sources have noted that there is a decryptor available for the Horros Ransomware infections. However, in most cases, recovering the files encrypted by these types of attacks is not possible. Because of this, preventive actions are the best measure to ensure that your data is always safe from these threats. The best preventive measure is to have reliable file backups stored on external memory devices, which can enable you to restore affected files after they have been compromised. Apart from file backups, malware researchers advise having a security program that is fully up-to-date to protect your data.
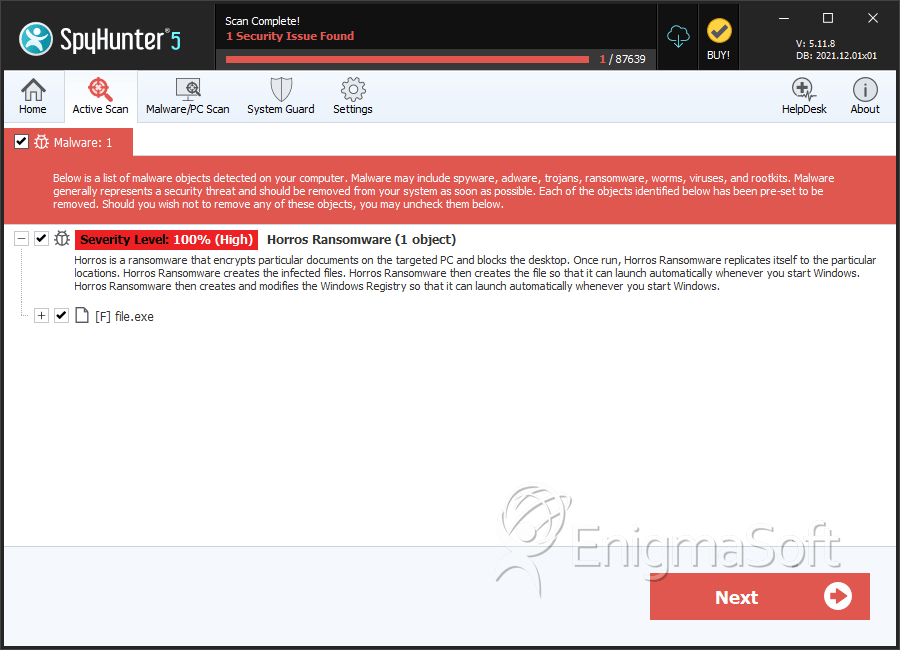
SpyHunter Detects & Remove Horros Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 095ae02d1a70dbabccd47bd0d0a706eb | 1 |

