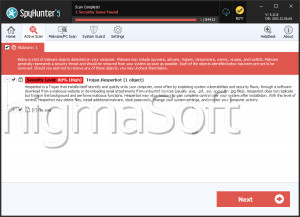
Hesperbot Trojan
Hesperbot Trojan is a prejudicial program and variant of the infamous Zeus Trojan. Systems infected by Hesperbot (Trojan) may have their banking credentials at risk, meaning their online banking could be hacked and financial future threatened.
Hesperpot Trojan appears to root from the Czech Republic as evidenced by its true domain (ceskaposta.cz) cleverly used and masked in an email spam communication purporting to come from the Czech Postal Service. Email spam continues to be problematic and a popular threat strategy that dupes unwary PC users who click on infectious links or attachments that unleash threats onto their vulnerable systems. The theme of the email spam is also familiar, a fake parcel tracking communication and attachment. If clicked or opened, both a computer and mobile component of Hesperbot is dropped. Today, a lot of people have connectivity to multiple devices, i.e. desktop, laptop, mobile, ipad, etc., a trend cybercriminals and malware makers of Hesperbot are counting on.
Similar to the infamous and game changing Zeus, Hesperbot Trojan has the technical ability to:
- Inject HTML code into running processes.
- Capture screenshots, particularly those of banking or financial login screens in an effort to steal login credentials.
- Perform keylogging, i.e. capturing keystrokes into online forms, particular those of a financial nature.
- Take video, again, for the purpose of capturing login screens and input.
- Setup a hidden Virtual Network Server (VNC) to communicate secretly with hackers and stay off the radar of anti-virus or anti-malware detection tools.
Despite having Czech roots, Hesperbot Trojan has mainly been tracked as attacking online users and systems in Turkey. However, do not take comfort in the locale as threats, especially APTs having success, are often duplicated, i.e. cloned, or tweaked to spread across the global spectrum. While a lot of banking institutions end up reimbursing customers who have their banking accounts hacked, in the end we all end up paying. Banks and other businesses affected will have to recoup their losses somehow and that usually means higher fees for services. Therefore, fighting cybercime requires a collective effort by the security community and those being targeted, i.e. computer, mobile, etc. and users. Anyone who connects to the Internet must adhere to safety concerns and practices as follows:
- Invest in a stealth anti-malware solution that guards your system 24 hours, 365 days a year and uses real time protection, i.e. updates definitions around the clock.
- Keep software updated and patched in a timely fashion.
- Use strong passwords.
- For your own safety, do not store credentials in the browser cache. Although it is convenient to have frequently used forms auto populated, i.e. auto filled, this is the first area many malware programs are programmed to look, especially when the browser is vulnerable to attacks.
- Only download and install programs from vendors you trust, so do your due diligence to check out the stability and security before accepting or clicking to download.
- Be leery of freeware. A lot of freeware comes with a high price, i.e. unwanted programs, some even harmful.
- React quickly to weird system behaviors, since it is possible an APT (Advanced Persistent Threat) tiptoed past your security. Unfortunately, zero exploits are just that 'zero or no warning.' Zero simply means an 'unknown' behavior or a threat has found an unknown loophole. If security isn't aware, sometimes it simply cannot foresee or block the attack. However, early reaction can mitigate loss or damage.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.