Heropoint Ransomware
The Heropoint Ransomware is an encryption ransomware Trojan. These threats are quite common and can be devastating. Ransomware Trojans like the Heropoint Ransomware will encrypt the victim's files using a strong encryption algorithm and then request the payment of a ransom in exchange for the decryption key, necessary to restore the affected files. In most cases, the encryption method is strong and cannot be cracked without the decryption key, essentially allowing the extortionists to hold the victim's files hostage.
Table of Contents
How the Heropoint Ransomware may be Delivered to Victims
The Heropoint Ransomware was first reported on January 2, 2018. The Heropoint Ransomware seems to not be in a finished condition and is still early in development. Like most ransomware Trojans active currently, it is likely that the Heropoint Ransomware may reach its victims by using spam email attachments. One of the most favored methods for delivering ransomware like the Heropoint Ransomware is to attach a DOCX file to a spam email message. These spam emails will use social engineering techniques to convince the victim to download and execute the file attachments that may disguise themselves as messages from Amazon, Facebook, various banks, or other legitimate sources.
The Well-Known Attack of the Heropoint Ransomware
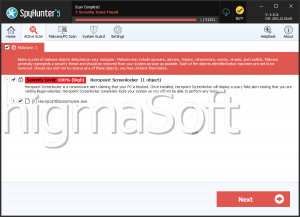
Once the Heropoint Ransomware is downloaded and installed on the victim's computer, the Heropoint Ransomware will run on the infected computer as 'HeropointRansomware.exe.' The Heropoint Ransomware is a small program that will use the XOR encryption to make the victim's files inaccessible. Unlike other encryption ransomware Trojans, which target a wide variety of file types, the Heropoint Ransomware targets only ten different file types in its attack. The Heropoint Ransomware will encrypt the files with the following file extensions:
.TXT, .PNG, .ICO, .MP3, .EXE, .JPG, .PPTX, .XLSX, .HTLM, .MP4
The files encrypted by the Heropoint Ransomware attack will no longer be recognized by the Windows Explorer and appear as blank icons on the infected computer.
How the cybercrooks may Profit from Attacks Like the Heropoint Ransomware
The Heropoint Ransomware will generate a lock screen with a message that reads as follows:
'WHAT HAPPENED ?
Your precious files have been encrypted from my virus
How do i adjust this?
Pay 20$ in bitcoin to get password
WHAT DO NOT HAVE TO DO?
Open the task manager
Open the cmd (command prompt)
Open Regedit and sethc.....
Run pc in Safe Mode
Delete rigestries from msconfig
WHAT DOES IT HAPPEN IF I DO NOT PAY?
Well .... to files, photos, texts, word / powerpoint projects you can say goodbye ...
My email is: Heropointyt@gmail.com'
The Heropoint Ransomware ransom note does not function merely as a text message, but also as a lock screen. It prevents the victim from accessing the Task Manager, Command Line or the Registry Editor or closing the Heropoint Ransomware note. Because of this, it will be necessary to restart the affected computer using Safe Mode or another alternate start-up method to bypass the Heropoint Ransomware lock screen. Unfortunately, the currently files encrypted by the Heropoint Ransomware attack are not recoverable without the decryption key. Because of this, it will be necessary to restore the affected files from file backups.
Protecting Your Data from Threats Like the Heropoint Ransomware
The best protection against threats like the Heropoint Ransomware is to have file backups on the cloud or external memory devices. This allows victims of the Heropoint Ransomware attack to restore the affected files from a backup copy without having to engage with the cybercrooks or pay the Heropoint Ransomware ransom. Apart from this, they should use a security program to protect their computers and prevent the Heropoint Ransomware from running on their computers. The combination of a reliable security program and file backups should be effective against threats like the Heropoint Ransomware. Since the likely distribution vector for this threat involves spam email messages, measures against these misleading content also can be effective.
URLs
Heropoint Ransomware may call the following URLs:
| dosesoftbun.live |