HC6 Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 1 |
| First Seen: | November 30, 2017 |
| Last Seen: | July 23, 2019 |
| OS(es) Affected: | Windows |
The HC6 Ransomware is an encryption ransomware Trojan that is part of a wave of encryption ransomware Trojans released in November 2017. The HC6 Ransomware is designed to encrypt the victim's files to make them inaccessible. This allows the HC6 Ransomware to demand a ransom payment from the victim in exchange for the application that will make it possible to restore the affected files. The HC6 Ransomware was first observed carrying out attacks on November 28, 2017. The HC6 Ransomware will infect computers running the Windows operating system and will enter the victim's PC through a corrupted Microsoft Word document downloaded from a spam email message. The HC6 Ransomware runs as the executable file 'hc6.exe' on the victim's computer. The HC6 Ransomware seems to be an independent encryption ransomware project and does not seem to be part of a larger family or an open source encryption ransomware engine such as EDA2 or HiddenTear.
Table of Contents
The HC6 Ransomware will Make Your Files Unusable
The HC6 Ransomware will target the victim's files, encrypting them with a strong encryption algorithm to make them inaccessible by its attack. Fortunately, it seems that PC security researchers, who can allow computer users to restore their files, have developed a decryption program. The HC6 Ransomware will encrypt the user-generated files, which may include media such as images, music and video, and a wide variety of commonly used file types. The HC6 Ransomware will mark the files encrypted by its attack with the '.fucku' extension, which is included to each infected file's name. The examples of the files that threats like the HC6 Ransomware will encrypt in their attack include:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
The HC6 Ransomware’s Ransom Demand
The HC6 Ransomware demands a ransom of $2,500 to be paid through Bitcoins. However, refraining from paying the HC6 Ransomware ransom may save your money and a lot of annoyance. The HC6 Ransomware's ransom note is delivered in a text file named 'recover_your_fies.txt' dropped on the infected computer's desktop. This file's name is misspelled, and there also are several misspelled words in the HC6 Ransomware's ransom note, which reads as follows:
'ALL YOUR FILES WERE incript.
ORDER, TO RESTORE THIS FILE, YOU MUST SEND AT THIS ADDRESS
FOR $ 2500 BTC FOR ALL NETWORK
[BTC WALLET] AFTER PAYMENT SENT EMAIL nullforwarding@qualityservice.com
FOR INSTALLATION FOR DECRIPT
NOT TO TURN OFF YOUR COMPUTER, UNLESS IT WILL BREAK'
The people responsible for the HC6 Ransomware attack shouldn't be contacted, and the HC6 Ransomware ransom shouldn't be paid. In the case of the HC6 Ransomware, computer users can use the freely available decryption program released by PC security researchers to restore their files after an HC6 Ransomware infection. However, in the case of most threats that are similar to the HC6 Ransomware, recovering the affected files may not be a possibility. Because of this, the best protection against the HC6 Ransomware and similar ransomware Trojans is to have a reliable, fully updated anti-malware application and backup copies of your files stored on the cloud or an external memory device.
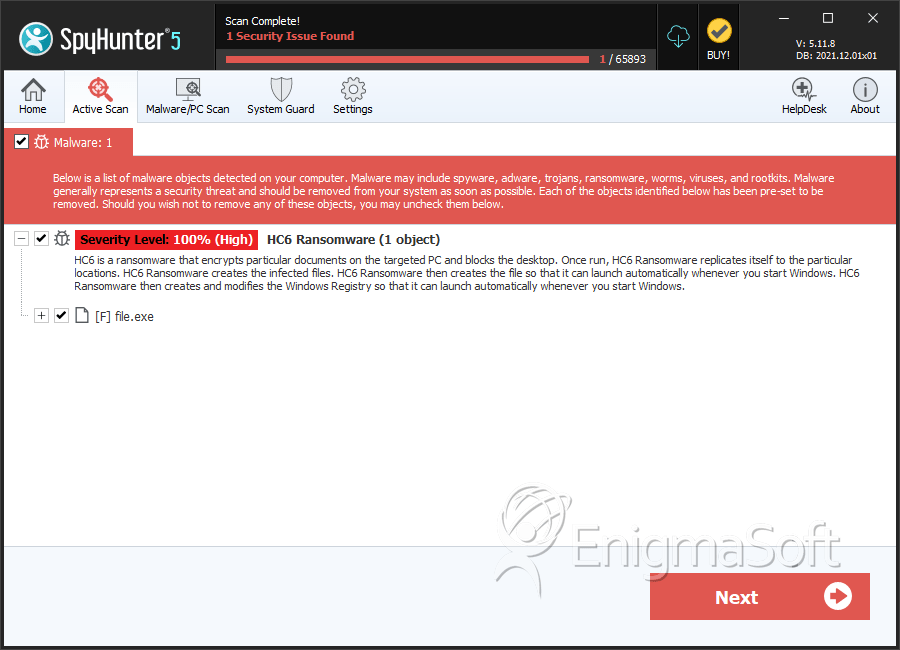
SpyHunter Detects & Remove HC6 Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | d7a8a80c8c30378a5f460989e0f50dc3 | 0 |

