HackTool:Win32/Oylecann.A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 2,525 |
| First Seen: | December 28, 2012 |
| Last Seen: | May 31, 2026 |
| OS(es) Affected: | Windows |
The HackTool:Win32/Oylecann.A cyber threat can grant attackers a remote access to infected PCs. The HackTool:Win32/Oylecann.A malware is connected to the Fynloski backdoor trojan, and they are both used as tools to infiltrate systems. The HackTool:Win32/Oylecann.A trojan is deployed enclosed in archive files that are attached to spam emails with subject lines relating to financial operations. The HackTool:Win32/Oylecann.A malware is used by hackers to compromise the security of computers and modify and extract data. Additionally, HackTool:Win32/Oylecann.A can be used to perform DDoS attacks by flooding networks with TCP, UDP and HTTP packets. It can be concluded that HackTool:Win32/Oylecann.A can be used by hackers to perform a number of malicious activities and hijack your system resources. The HackTool:Win32/Oylecann.A malware can be countered by using a trusted anti-malware shield that can provide you with advanced cyber defenses.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| AVG | Win32/Heur |
| Ikarus | Virus.Win32.Heur |
| Sophos | Mal/Scribble-D |
| eSafe | Win32.NewPoly |
| McAfee | Artemis!3AC5AE179C32 |
| Fortinet | Adware/Fam.NB |
| AntiVir | APPL/Solimba.Gen |
| Sophos | Solimba Installer |
| Symantec | Trojan.ADH.2 |
| Fortinet | W32/Kryptik.ARKD |
| AntiVir | TR/Meredrop.A.1227 |
| Avast | Win32:Rootkit-gen [Rtk] |
| McAfee | Artemis!DFA4D1E735CD |
| McAfee-GW-Edition | Heuristic.LooksLike.Win32.SuspiciousPE.J |
| Comodo | Heur.Corrupt.PE |
SpyHunter Detects & Remove HackTool:Win32/Oylecann.A
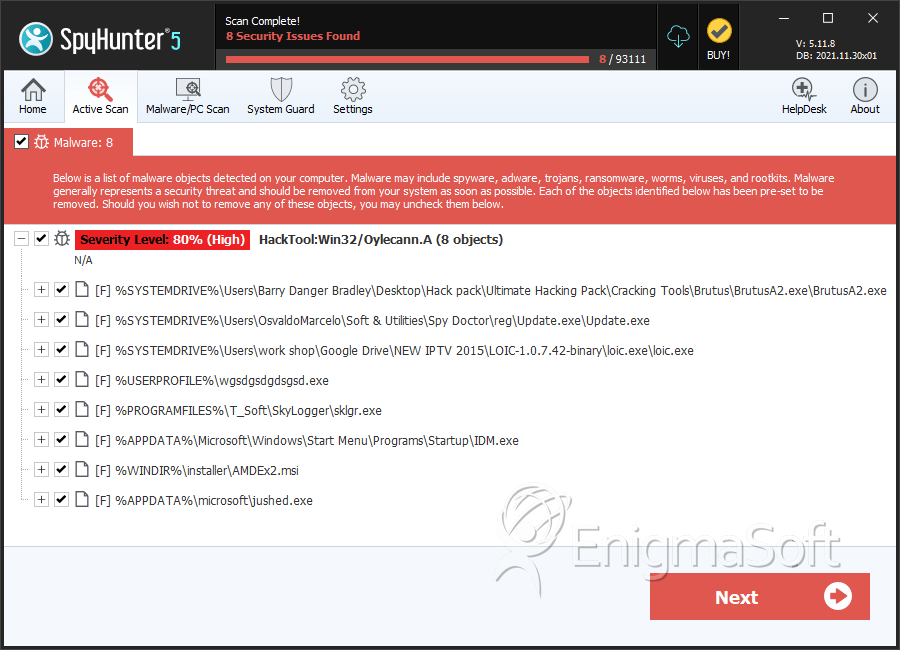
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | BrutusA2.exe | d6066d187be09b56d917ad3aa63e4874 | 687 |
| 2. | Update.exe | 3ac5ae179c32df28c24c709cbc1dda85 | 427 |
| 3. | loic.exe | b596e7cacbad1e814b0cd053086c4900 | 190 |
| 4. | wgsdgsdgdsgsd.exe | dfa4d1e735cdfbfe0c9325b5d8b97859 | 13 |
| 5. | sklgr.exe | 0b82e239b7eddc6d018ca190de2c4e77 | 6 |
| 6. | IDM.exe | 46f02a41b53bc5a875b72326070a925b | 6 |
| 7. | AMDEx2.msi | 705dd89587131c80d0351c8adbcadf98 | 3 |
| 8. | jushed.exe | 3f3af17ce4f42d0bd2e0ec8d080487e9 | 1 |
