Grum
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
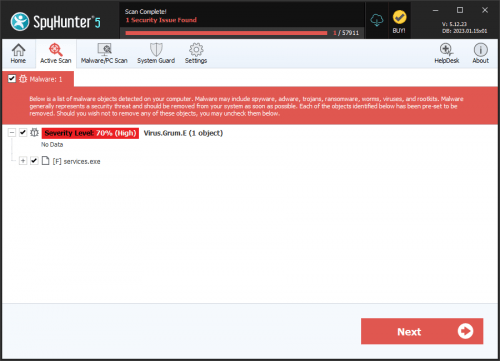
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 8,587 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 3,542 |
| First Seen: | July 23, 2012 |
| Last Seen: | September 13, 2023 |
| OS(es) Affected: | Windows |
The Grum botnet was a vast network of computer systems infected with Trojans designed to send out spam email and to allow criminals to control infected computers from a remote location. At one point, Grum may have been responsible for up to thirty-five percent of all of the world's spam email. Fortunately, law enforcement officials in The Netherlands, Panama and the Russian Federation, with the help of PC security researchers, have shut down Grum's command and control servers, which were located in those countries. Although Grum-related Trojans are still found in the wild and can cause various symptoms on infected computers, the fact that these command and control servers aren't active anymore is a significant blow to the operations of the criminals behind the Grum.
The Grum was set up so that Grum could send out massive amounts of email spam from hundreds of thousands of infected computers all around the world. Basically, the criminals behind the Grum used a variety of Trojans with the goal of infecting computer systems and forcing them to connect to the Grum. From there, these computer systems could be controlled remotely in order to send out spam email messages. By coordinating millions of computers at once, criminals could use the Grum to send out impressive amounts of email spam. The Grum in its earliest versions had been active since 2008 and quickly took the place of other botnets, such as Rustock, that were disabled thanks to law enforcement operations. Fortunately, thanks to the efforts of PC security analysts all around the world, the amount of spam email messages advertising cheap sexual enhancers and shady online businesses will be greatly reduced in the future.
Malware Associated with Grum
With the Grum disabled, Trojans associated with this botnet will remain on the victims' computer systems but will have no way of sending out spam email. This happens because they will not be able to communicate with their command and control servers, which have been shut down. While some symptoms from software conflicts and performance issues may present themselves, shutting down the Grum effectively neutralizes its associated malware. The Trojans associated with the Grum go by various names, including Trojan.Win32.Buzus.cqit, Tedroo, Win32/Injector.AJF, a href="/infostealerbankerc-removal/" title="Remove Infostealer.Banker.C">Infostealer.Banker.C, TROJ_BUZUS.BKM and many others, depending on the brand of anti-malware software used to detect them. The main purpose of these Trojans is to send out spam email by receiving email addresses from a command and control server and then using SMTP servers in order to send out email spam to these contacts.
URLs
Grum may call the following URLs:
| doxyspats.com |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.