Great Discover
The Great Discover is far worse than the typical adware. It too delivers unwanted advertisements to the affected systems that could greatly diminish the user's browsing experience. However, on top of that annoying functionality, it also possesses the capabilities of a crypto-mining threat. The Great Discover will initiate its processes in the background and start to siphon off the system's hardware resources. It could impact the GPU, CPU and RAM. All hijacked resources will be used to generate coins for a specific cryptocurrency, depending on the preferences of its operators. The threat actor could set it to mine for Bitcoin, Ethereum, Monero, Litecoin, etc.
On systems with a sufficiently powerful GPU and CPU and enough RAM, Great Discover's activities might remain unnoticed. The threat also could be adjusted to initiate only when the computer is not under heavy load, thus helping it maintain its cover for longer periods. However, on older devices, users might notice that various applications are acting strange, lagging, becoming unstable or even crashing. The OS itself could become much slower and experiencing frequent freezes.
The most likely vector used by Great Discover to infiltrate the user's computer is via dubious software installers. When users search for a cracked version of a legitimate software product such as a newly released video game, they are often led to questionable download sites. Instead of the desired products, the installers obtained from such untrustworthy sources deliver various adware, browser hijackers, PUPs (Potentially Unwanted Programs), or, as in this case, crypto-mining threats.
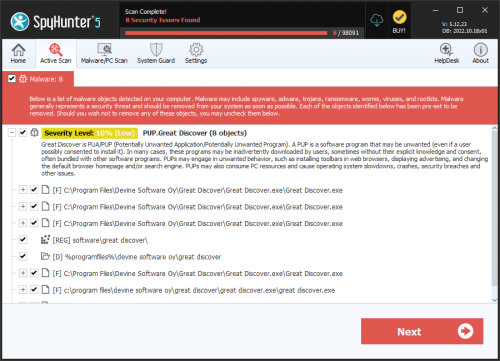
It is recommended to remove Great Discover as soon as you notice its presence. The preferable method is to perform a thorough scan with a reputable anti-malware solution and then remove the detected items. Users also can try to delete Great Discover manually but if you do not get all of its files, there is a chance that the threat will reestablish itself on the system.