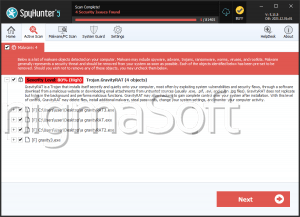
GravityRAT
GravityRAT is a Remote Access Trojan (RAT) distributed via documents laced with corrupted macros. The first version of GravityRAT had the ability to collect information from compromised systems such as MAC address, computer name, IP address, username, dates, mapped volumes in the system, as well as any files that have the following extensions: .docx, .doc, .pptx, .ppt, .xlsx, .xls, .pdf and .rtf.
The second version of the RAT expands on that by adding the ability to open ports in the victimized host by running the Netstat command, as well as listing any running processes, available services, exfiltrating .ppt and .pptx files, gathering files in any USB keys connected to the system. It also supports AES file encryption with the key 'lolomycin2017,' collecting even more information on the account, such as the account type, domain name, full name, SID, status and description. It also checks if the system is a virtual machine through several different techniques, potentially attempting to ascertain if the host is run on one.
What GravityRAT does is to use many virtual machine evasion techniques, such as checking the number of CPU cores, thus terminating itself if there is only one core, requesting hardware temperature details (which virtual machines usually don't provide), checking the username, if the MAC address matches the one used by most popular virtual machine vendors, as well as for the presence of software from a list of malware analysis and dissection tools used in anti-malware operations.