GPAA Ransomware
The GPAA Ransomware is a ransomware Trojan that claims to be linked to the Global Poverty Aid Agency. Computer users are supposed to be convinced by the GPAA Ransomware to 'give' to this agency, with the goal of raising the large amount of 1000 BitCoin (nearly three million USD, approximately). Although the GPAA Ransomware claims that its main goal is to help people living in poverty, it is clear that the GPAA Ransomware is just carrying out a tactic and attempting to take advantage of inexperienced computer users. Like most other ransomware Trojans, the GPAA Ransomware may be delivered through the use of corrupted spam email attachments. Beyond the GPAA Ransomware's transparent superficial tactic, impersonating a humanitarian aid agency, there is virtually no difference between the GPAA Ransomware and the countless other encryption ransomware Trojans that are active currently.
Table of Contents
A Name with Various Possible Meanings but Only One Objective
The GPAA Ransomware is designed to encrypt user-generated files, searching the victim's computer for certain file types and then encrypting them with a strong encryption algorithm. The GPAA Ransomware will target the files located in all local drives, as well as on external memory devices connected to the victim's computer. The GPAA Ransomware will mark the encrypted files by adding the file extension '.cerber6' to the end the corrupted file's name. The GPAA Ransomware does not seem to belong to a larger threat family but that it was probably developed independently. In its attack, the GPAA Ransomware will target at least 180 different file types, including those files with the following extensions:
.123, .3dm, .3dmap, .3ds, .3dxml, .3g2, .3gp, .602, .7z, .accdb, .act, .aes, .ai, .arc, .asc, .asf, .asm, .asp, .assets, .avi, .backup, .bak, .bat, .bdf, .blendl, .bmp, .brd, .bz2, .c, .c4dl, .catalog, .catanalysis, .catdrawing, .catfct, .catmaterial, .catpart, .catprocess, .catproduct, .catresource, .catshape, .catswl, .catsystem, .cdd, .cgm, .class, .cmd, .config, .cpp, .crt, .cs, .csr, .csv, .dae, .db, .dbf, .dch, .deb, .der, .dif, .dip, .djvu, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .edb, .eml, .fbx, .fla, .flv, .frm, .gif, .gl, .gl2, .gpg, .gz, .h, .hpgl, .hwp, .ibd, .icem, .idf, .ig2, .igs, .ipt, .iso, .jar, .jasl, .java, .jpeg, .jpg, .js, .jsp, .key, .lay, .lay6, .ldf, .library, .m3u, .m4u, .mal, .max, .maxl, .mb, .mdb, .mdf, .mid, .mkv, .mml, .model, .mov, .mp3, .mp4, .mpeg, .mpg, .msg, .myd, .myi, .nef, .obj, .odb, .odg, .odp, .ods, .odt, .onetoc2, .ost, .otg, .otp, .ots, .ott, .p12, .paq, .pas, .pdf, .pem, .pfx, .php, .pl, .png, .pot, .potm, .potx, .ppam, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .ps, .ps1, .psd, .pst, .rar, .raw, .rb, .rtf, .sch, .session, .sh, .sldm, .sldx, .slk, .sln, .snt, .sql, .sqlite3, .sqlitedb, .stc, .std, .step, .sti, .stp, .stw.
After encrypting the victim's files, the GPAA Ransomware will deliver its ransom note, a message full of misspellings and grammar mistakes claiming that the victim must pay an extremely large ransom amount. The GPAA Ransomware ransom note is contained in a file named '! READ.htm,' which displays the following text on the victim's computer:
'Congradulations! Now you are a member of GPAA (Global Poverty Aid Agency).
We need bitcoins, our crowdfunding goal is to get 1000 BTCs. 1 BTC for 1 CHILD!
>> Click Here To Buy Bitcoins <<
Q: What happened?
A: Ooops, your inportant files are encrypted. lt weans you will not be able to access them anyeore until they are decrypted.
These files could NOT be decrypted if you do not have the KEY (RSA4096).
Q: How can I get the decrypt programme?
A: Your task is 10.91 btc.
Send the correct amount to the bitcoin address 19ZLfCEpxdskvWGLLhNUnM6dUG7yikhz2W
You can send more coins. When the goal is achieved, you will get the decrypt programme.
Q: Where to get the decrypt programme?
A: When the goal is achieved, we will send it to sc19ZLfCEpxdskvWGLLhNUnM6dUG7yikhz2W@outlook.com
(You may register it first with the specified password: Save1000Children!!! ).'
Dealing with the GPAA Ransomware
The best protection against ransomware Trojans like the GPAA Ransomware is to use a reliable security program and have file backups. If you can recover your files from a backup, those tactics can no longer extort you by taking your files hostage. Simply remove the GPAA Ransomware with your anti-virus program and restore the affected files by replacing them with the backup copies.
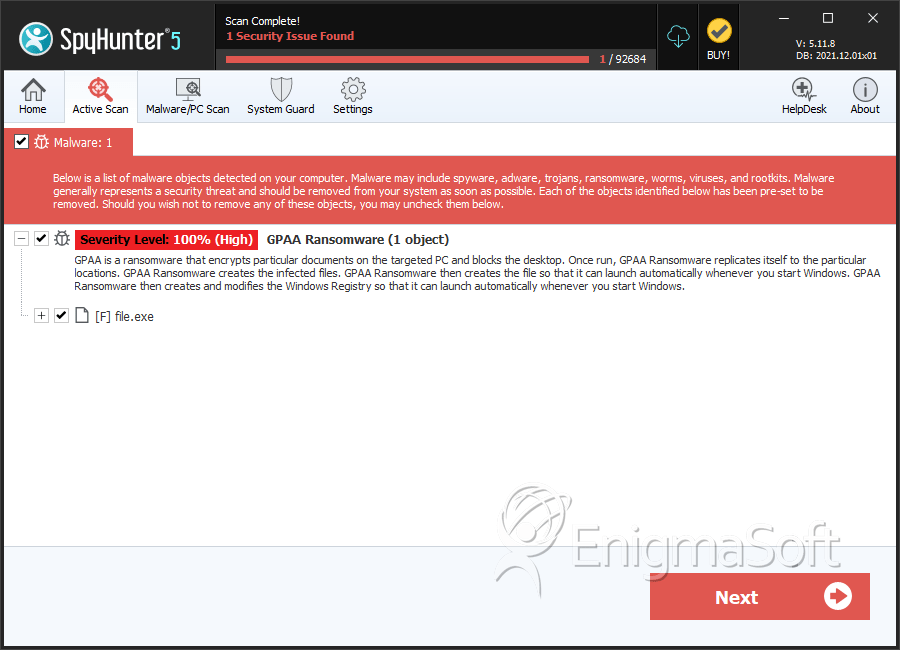
SpyHunter Detects & Remove GPAA Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | bf58714838edfcc135a64818d3667547 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.