GoodSearch Toolbar
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 3,627 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 7,481 |
| First Seen: | September 27, 2010 |
| Last Seen: | January 10, 2026 |
| OS(es) Affected: | Windows |
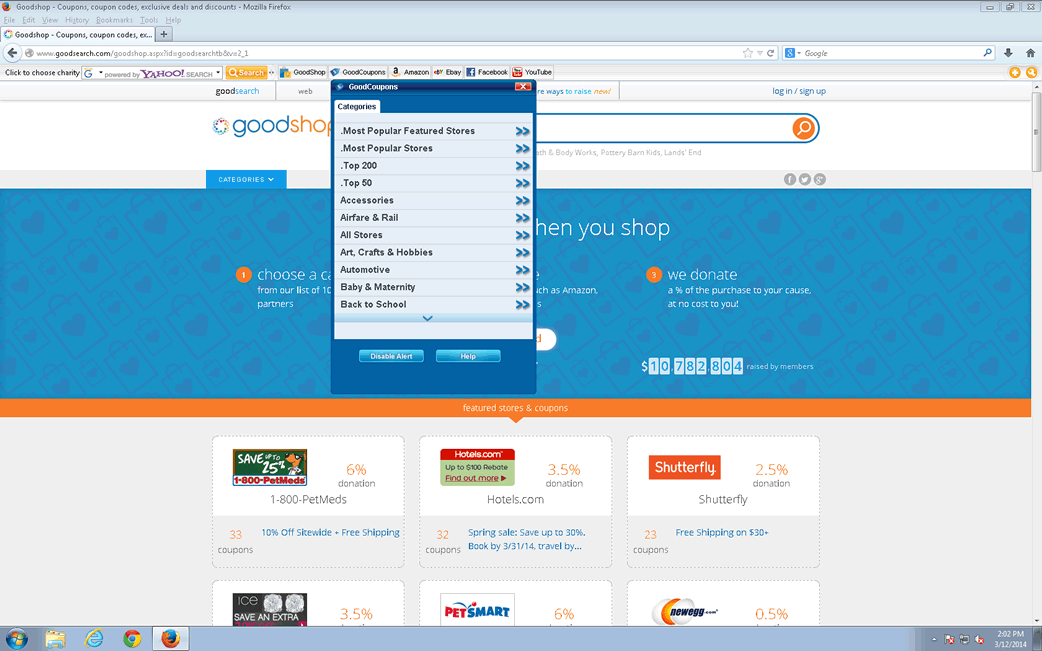
GoodSearch Toolbar Image
GoodSearch Toolbar is an unwanted browser extension/potentially unwanted program, which may circulate and access the PC through packed free software. GoodSearch Toolbar may also operate as a browser hijacker and continuously redirect PC users to questionable websites. GoodSearch Toolbar may press compute users visit other suspicious websites that are not connected with their search queries in any popular search engine. GoodSearch Toolbar can be downloaded manually; however, it may also enter the computer system through packaged free software that can be downloaded from unprotected download websites. After installation on the PC, GoodSearch Toolbar may change the default browser settings and take over all the Web browsers installed on the PC in an effort to show up on them as a toolbar. GoodSearch Toolbar may start interfering the computer user's Web sessions and reroute him to questionable websites that may be commercial. GoodSearch Toolbar may keep track of the PC user's browsing routine and display commercial pop-up advertisements and messages.
Table of Contents
Aliases
1 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| Panda | Suspicious file |
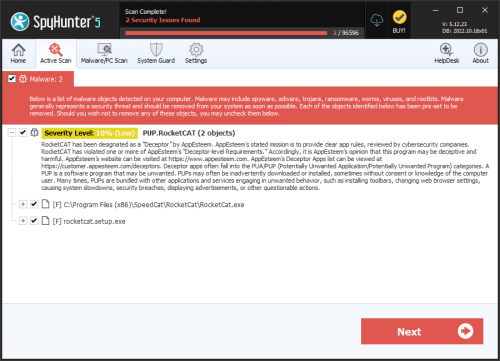
SpyHunter Detects & Remove GoodSearch Toolbar
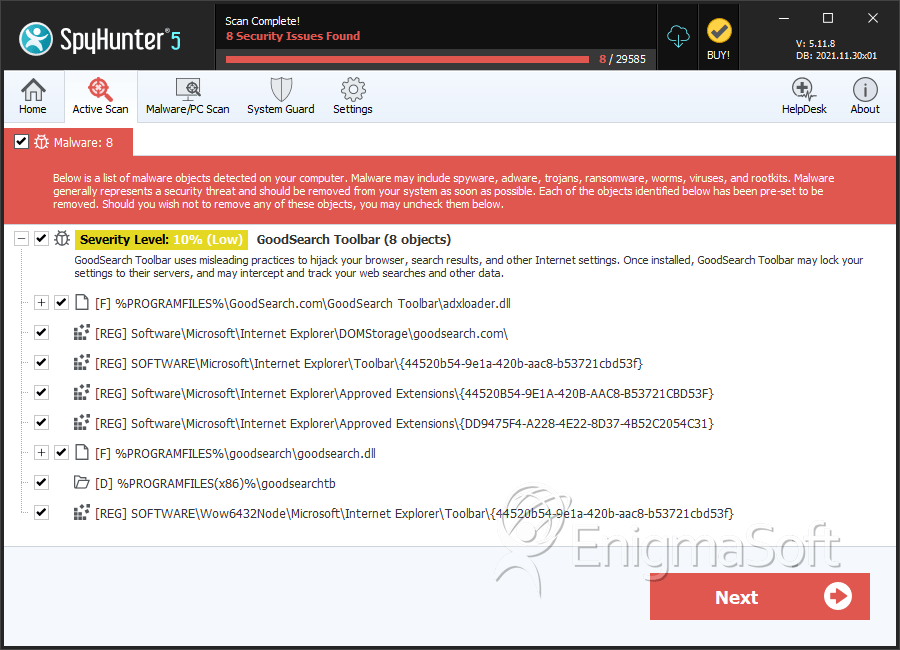
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | adxloader.dll | 10726c16d80d820509fd81d04762f53e | 1,196 |
| 2. | goodsearch.dll | 566ca922331cedb60d30bb9e73e418d6 | 14 |
Registry Details
Directories
GoodSearch Toolbar may create the following directory or directories:
| %PROGRAMFILES%\goodsearchtb |
| %PROGRAMFILES(x86)%\goodsearchtb |
URLs
GoodSearch Toolbar may call the following URLs:
| goodshop.com |