Good Ransomware
Good Ransomware Image
The Good Ransomware is among the newest spotted ransomware threats lurking on the Web. Like most data-locking Trojans, the Good Ransomware will sneak into your system, encrypt your data, and then request a ransom fee to unlock the affected files supposedly.
There are a number of ransomware spinoffs, versions of the same codebase with minor modifications, that all fall under the common name ".good ransomware." What they have in common is that they all append the .good extension to encrypted files. In this way, a file named "front_porch.jpg" will turn into "front_porch.jpg.good" once it has been encrypted. It seems a number of bad actors are using the .good ransomware, as there are a number of different ransom notes and contact e-mails used in different campaigns and attacks. This is not surprising at all, in an age when ransomware is sold as a service and any number of threat actors can obtain the same basic attack kit, then customize it slightly to fit their needs. For example, some versions of the .good ransomware list specific ransom demand sums in Bitcoin, while others simply include a contact e-mail.
The most common attack vector of the .good ransomware is the usual - spam e-mails that contain malicious attachments, posing as some ordinary document - a tax return form, an invoice, or some other innocent-looking file.
The .good ransomware is also known to use ransom notes named "HOW_TO_RECOEVR_FILES.txt" and "RETURN FILES.txt". The contact e-mails used in those two ransom notes are respectively "dsupport@airmail.cc" and "onecrypt@aol.com". What all versions have in common is the threat that the ransom demand will increase the longer the victim waits - a common scare tactic that many bad actors use to intimidate their victims and scare them into immediately paying the ransom.
Table of Contents
Propagation and Encryption
The authors of the Good Ransomware may be using emails to spread their creation. These emails usually contain an attached document that appears to be important such as CVs, tax return documentation, a potential job offer, etc. This is a common social engineering trick to mislead the user into opening the attachment. However, once they attempt to open the attached file, a macro-script that was hidden in, it will be triggered. Then, the executable file of the Good Ransomware will be initialized. Next, the Good Ransomware will scan the infected machine and locate the files, which it was programmed to go after. After this is completed, the Good Ransomware will execute its encryption process and lock all the targeted files. The files locked by the Good Ransomware will have a '.good' extension added at the end of their filenames. For example, a file called 'no-traps.jpeg' will be renamed to 'no-traps.jpeg.good' once the Good Ransomware encrypts it.
The Ransom Note
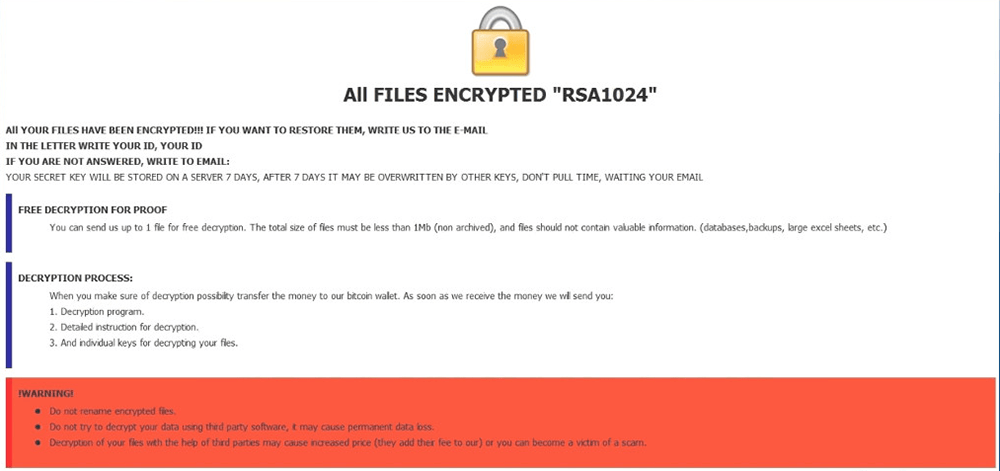
The next phase of the attack is the dropping of the ransom note. The Good Ransomware's ransom note is called 'Restore-My-Files.txt,' and in it, the authors of the Good Ransomware have provided 'goodmen@countermail.com' and 'datareesstore@tutanota.com.' They also state that the longer the user waits to contact them, the higher the ransom fee will be. The cyber crooks behind the Good Ransomware also warn the users against attempting to decrypt their data using third-party services. This is a useful advice as such services are usually a hoax.
One version of the .good ransomware drops a ransom note named "Restore-My-Files.txt", which contains the following text:
All your files are encrypted.
To return to normal, please contact us by this e-mail: goodmen@countermail.com
Be sure to duplicate your message on the e-mail: datareesstore@tutanota.com
Interesting facts :
1. Over time, the cost increases, do not waste your time.
2. Only we can help you, for sure, no one else.
3. BE CAREFUL !!! If you still try to find other solutions to the problem, make a backup copy of the files you want to experiment on, and play with them. Otherwise, they can be permanently damaged.
4. Any services that offer you help or just take money from you and disappear, or they will be intermediaries between us, with inflated value. Since the antidote is only among the creators of the virus
Set topic of your message to [string]
Currently, there is no tool that can decrypt files encrypted with the .good ransomware. Of course, that does not mean that paying the ransom will result in the recovery of your files. The cybercriminals on the other end may or may not help you get your files back, so home users who do not keep vitally important data on their machines might want to stay away from extortionate payments. The best bet against ransomware finding its way on your system in the first place would be to use a modern, up-to-date PC security suite that has anti-ransomware capabilities.
However, the fact that you should not trust third-parties that claim to be able to decrypt your files in return for payment does not mean you should pay the attackers either. Cybercriminals are not known for their honesty, and they will likely never deliver on their end of the deal. Instead, use a reputable anti-virus software suite and use it to remove the Good Ransomware from your PC safely.


