Get2
There is a hacking group that has been developing over the past several years greatly. It is called TAT505, and researchers believe that this group is behind the notorious Locky Ransomware campaigns and the Dridex banking Trojan. The TAT505 group appears to target companies in the finance industry, mainly. The hacking group is known to launch attacks all around the globe – the United States, Canada, Singapore, Greece, Sweden, Georgia and others. When malware researchers studied the latest TAT505 campaigns, they came across two previously unknown malware families – the SDBBot RAT and the Get2 Trojan downloader.
Collects Data and Delivers a Secondary Payload
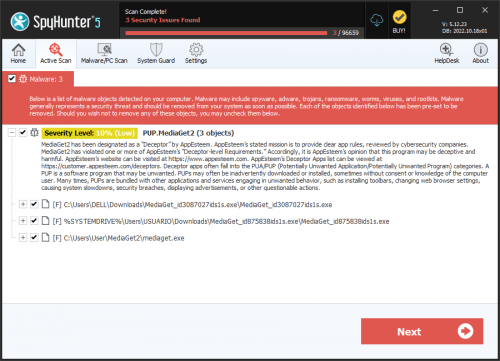
Much like most Trojan downloaders, once the Get2 Trojan infiltrates a host, it will start collecting information regarding the hardware of the host and the software present. All the gathered data will then be forwarded to the operators’ server. This information helps the attackers determine how to continue the operation in the most efficient manner. When the authors of the Get2 Trojan make up their minds, the threat will receive a secondary payload, which will be planted on the compromised system swiftly. Malware researchers have determined three separate second-stage payloads, which are deployed with the help of the Get2 Trojan downloader:
- On the 9th of September, the TAT505 group launched campaigns targeting financial institutions located in the UAE, Greece, Lithuania, Singapore and others.
- On the 20th of September, the hacking group went after victims operating in the finance industry in the United States and Canada.
- On the 7th of October, the attackers concentrated all their efforts on targets in the United States only.
The infection triguer used by the attackers was macro-laced email attachments. The target would receive a compromised Microsoft Excel document attached to an email. In the campaign that took place on the 7th of October, the TAT505 group opted to host the threatening attachment files on external servers. The URL links in the email were shortened promptly. If the attackers manage to convince their target to open the corrupted attached file, the Get2 Trojan downloader will be given the green light to begin the attack. The Get2 Trojan will then wait to receive the second-stage payload, which is meant to be installed on the compromised computer. The Get2 Trojan downloader is known to deploy four different secondary payloads – the de hackers, the FlawedGrace RAT, the '.snatch file Extension' Ransomware and the FlawedAmmyy RAT.
It is clear to see that the Get2 Trojan downloader is among the favorite hacking tools of the TAT505 group; thus we will likely continue to hear about this threat in the future. Businesses need to start taking cybersecurity more seriously, as there are an ever-increasing number of threats lurking on the Internet.