FTCODE Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 14,782 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 961 |
| First Seen: | October 8, 2019 |
| Last Seen: | September 8, 2023 |
| OS(es) Affected: | Windows |
FTCODE Ransomware Image
Another ransomware threat has reared its ugly head recently. Its name is FTCODE Ransomware, and it does not appear to belong to any of the popular ransomware families. It is not known if free and publicly available decryption tools for the FTCODE Ransomware are available.
Table of Contents
Propagation and Encryption
It has not been determined what the infection vectors, which are involved in the propagation of this threat are. Cybercriminals dealing with data-locking Trojans tend to use several classic propagation methods - emails containing macro-laced attachments, fraudulent application updates, and fake pirated versions of popular software. Often, ransomware threats tend to target a wide variety of files to guarantee that enough damage will be done and the user may consider paying up the ransom. Usually, files like images, documents, videos, audio files, etc. will be the primary targets of threats like the FTCODE Ransomware.
The FTCODE Ransomware will run a scan to locate these files and then trigger its encryption process. After encrypting a file, the FTCODE Ransomware applies a new extension at the end of its filename - ‘.FTCODE.’ For example, if you had a photo that was called ‘paper-pale.jpeg’ originally after the encryption process is completed, the file will be renamed to ‘paper-pale.jpeg.FTCODE.’ To ensure that the user is less likely to retrieve any of the corrupted files for free, the FTCODE Ransomware also will wipe out the Shadow Volume Copies from the compromised host. Furthermore, the FTCODE Ransomware also will tamper with the System Restore module and disable it so that getting any of the data back will be nearly impossible.
This Week in Malware Episode 4: FTCODE Ransomware
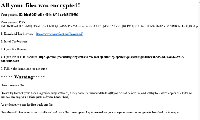
The Ransom Note
Then, the FTCODE Ransomware will drop a ransom note that goes by the name ‘READ_ME_NOW.htm.’ In the note, the attackers instruct the victim on how to download and install a TOR browser because their payment processing is carried out on a TOR-based payment portal. The authors of the FTCODE Ransomware state that within the first three days of the attack, the ransom fee will be $500. However, if the victim fails to pay up within this deadline, the ransom fee will begin increasing periodically:
- Between three and five days - $2,500.
- Between five and ten days - $5,000.
- Between ten and thirty days - $25,000.
Finally, the attackers claim that in case the fee is not processed within thirty days of the attack taking place the decryption key will be wiped out permanently, which means that there will be no way for the victim to retrieve any of the encrypted data.
Do not trust cyber crooks. Their threats, as well as their promises, are often just smoke and mirrors. It is far safer to remove the FTCODE Ransomware from your system using a reputable anti-virus application. Then, if you wish, you can try to retrieve some of the lost files using a third-party data-recovery tool.
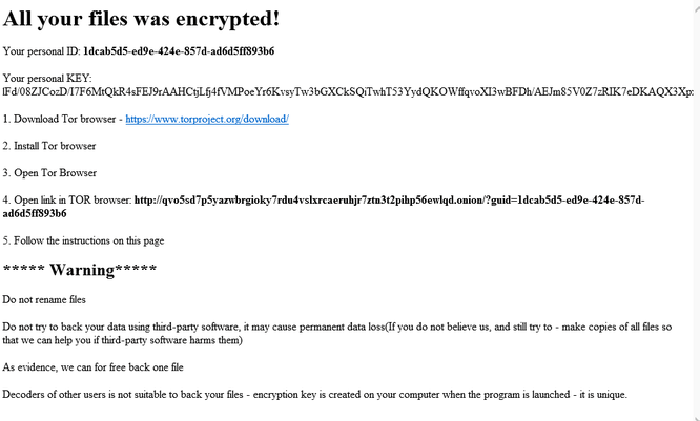
SpyHunter Detects & Remove FTCODE Ransomware
FTCODE Ransomware Screenshots
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.vbs | cdd6ee0b57678678a3dc48574ffb9f14 | 1 |
| 2. | file.doc | a5af9f4b875be92a79085bb03c46fe5c | 0 |