ForceLock Ransomware
Protecting devices from malware threats are crucial to safeguarding personal and organizational data. Ransomware, a particularly threatening form of malware, is designed to encrypt files and extort victims for a ransom for their decryption, leading to significant data loss and operational disruptions.
Table of Contents
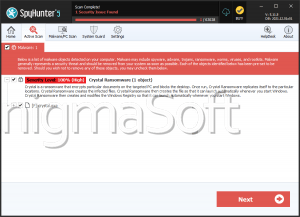
Understanding the ForceLock Ransomware
ForceLock is a type of ransomware belonging to the Globe Imposter family. Once a computer is infected, ForceLock encrypts files and appends the '.forcelock' extension to filenames. For instance, '1.doc' becomes '1.doc.forcelock' and '2.jpg' is renamed to '2.jpg.forcelock'. The ransomware also generates a ransom note named 'how_to_back_files.html' to inform victims about the attack.
Post-Infection Actions
The ransom note claims that the victim's network has been breached and all important files have been encrypted using RSA and AES cryptographic algorithms. It warns that attempting to restore or modify the files with third-party tools will corrupt them, emphasizing that only the cybercriminals behind ForceLock can decrypt the files. The note further mentions that sensitive data has been collected and will be publicly released or sold if the ransom is not paid.
The Content of the Ransom Note
The ransom note includes a contact email (cryptomans77@outlook.com) and urges victims to contact the attackers within 72 hours in order to avoid a higher decryption cost. To prove their capability, the attackers offer to decrypt 2-3 non-essential files for free. The note serves as a means to pressure the victim into paying the ransom by highlighting the dire consequences of non-compliance, including the potential public release or sale of sensitive data.
Implications of Paying the Ransom
Despite the pressure, paying the ransom is definitely not recommended as it does not guarantee the recovery of the affected files. Cybercriminals often fail to provide the promised decryption tools even after receiving the ransom. Additionally, paying the ransom supports illegal activities and perpetuates the cycle of cybercrime.
Technical Aspects of the ForceLock Ransomware
The ForceLockRansomware uses a combination of RSA and AES cryptographic algorithms to encrypt files, making decryption virtually impossible without the attackers' tools. This strong encryption method ensures that recovering the files without the decryption keys is exceedingly difficult.
Threats and Extortion
ForceLock employs a double-extortion tactic, threatening to release or sell any sensitive data if the ransom is not paid. This tactic adds additional pressure on victims, who may be concerned about the exposure of confidential information.
Preventive Measures Against Ransomware
To protect against ransomware infections like ForceLock, users should implement the following security measures:
- Regular Backups: Maintain regular backups of sensitive or important data and ensure they are stored offline or in a secure, isolated environment. This practice may largely mitigate the impact of a ransomware attack by enabling data recovery without paying the ransom.
- Up-to-date Software: Keep all installed software, including the operating system and any applications, up to date with the latest security patches. This reduces vulnerabilities that ransomware can exploit.
- Anti-malware Solutions: Use reputable anti-malware software to detect, block, and remove ransomware before it can cause damage.
- Email and Web Filtering: Implement email filtering to block unsafe attachments and links. Use Web filtering to prevent any access attempts from known fraudulent websites.
- User Training and Awareness: Educate users about the perilousness of ransomware and how to recognize phishing emails and other common attack vectors.
- Network Segmentation: Segment the network to reduce the spread of ransomware if an infection occurs.
- Least Privilege Principle: Apply the theory of least privilege to reduce users' access to only the data and systems necessary for their roles.
Protecting devices from ransomware threats like ForceLock is essential to maintaining data security and operational continuity. By seting up robust security measures,keeping informed about new threats, anadopting a culture of cybersecurity knowledgement, users can significantly reduce the risk of falling victim to ransomware attacks. Regular backups, up-to-date software, and comprehensive security practices are key to defending against these harmful threats.
The full text of the note containing the ransom demand dropped on devices infected by the ForceLock Ransomware is:
'YOUR PERSONAL ID:
/!\ YOUR COMPANY NETWORK HAS BEEN PENETRATED /!\
All your important files have been encrypted!Your files are safe! Only modified. (RSA+AES)
ANY ATTEMPT TO RESTORE YOUR FILES WITH THIRD-PARTY SOFTWARE
WILL PERMANENTLY CORRUPT IT.
DO NOT MODIFY ENCRYPTED FILES.
DO NOT RENAME ENCRYPTED FILES.No software available on internet can help you. We are the only ones able to
solve your problem.We gathered highly confidential/personal data. These data are currently stored on
a private server. This server will be immediately destroyed after your payment.
If you decide to not pay, we will release your data to public or re-seller.
So you can expect your data to be publicly available in the near future..We only seek money and our goal is not to damage your reputation or prevent
your business from running.You will can send us 2-3 non-important files and we will decrypt it for free
to prove we are able to give your files back.Contact us for price and get decryption software.
email:
cryptomans77@outlook.com
cryptomans77@outlook.comTo contact us, create a new free email account on the site: protonmail.com
IF YOU DON'T CONTACT US WITHIN 72 HOURS, PRICE WILL BE HIGHER.'