Crystal Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
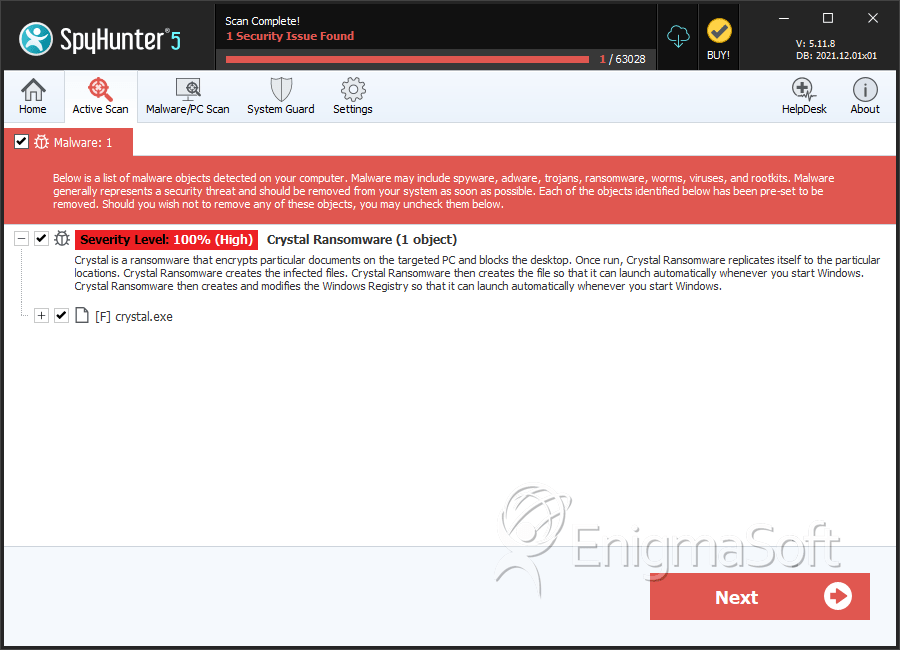
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 1 |
| First Seen: | August 3, 2017 |
| Last Seen: | April 18, 2018 |
| OS(es) Affected: | Windows |
The Crystal Ransomware is an encryption ransomware Trojan that targets English speakers computer users and seems to have most of its attacks targeted towards computer users in Europe and United States. The Crystal Ransomware is being distributed using a large-scale spam email campaign that tricks computer users into downloading and installing the Crystal Ransomware onto their computers. These spam email messages may be disguised as messages from legitimate companies and websites, tricking computer users into downloading a corrupted Microsoft Word file. This file has macro scripts that download and install the Crystal Ransomware on the victim's computer. The Crystal Ransomware is written using the Microsoft .NET framework and is capable of infecting most versions of Windows, going back to Windows XP and Windows Vista (if the .NET framework isn't installed, it will be installed by default in the Windows 7, 8 and 10).
Table of Contents
What is the Tactic Used by the Crystal Ransomware to Extort PC Users
During its attack, the Crystal Ransomware will use a combination of the AES and RSA encryptions to make the victim's data inaccessible. To restore the affected files, it is necessary to use the decryption key the con artists hold in their possession and will only release it when the victim pays a large ransom. The Crystal Ransomware will mark the files encrypted by the attack with the file extension '.CRYSTAL,' which is added to the end of each affected file. Once the Crystal Ransomware encrypts a file, it is no longer will be recoverable without the decryption key. The Crystal Ransomware also will add 32 bytes to the affected files' header, apart from encrypting the victim's files and appending the file extension mentioned above, making the affected files slightly larger.
In its attack, the Crystal Ransomware will target various file types on the infected computer, including the following:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, ,doc, .epub, .docx .fb2, .flv, .gif, .gz, .iso .ibooks,.jpeg, .jpg, .key, .mdb .md2, .mdf, .mht, .mobi .mhtm, .mkv, .mov, .mp3, .mp4, .mpg .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr2.
The Crystal Ransomware will avoid the files that are required by Windows to function since they will be necessary for the victim to be able to use the infected computer to pay the demanded ransom and view the ransom note that the Crystal Ransomware displays. The Crystal Ransomware will display a message on the victim's computer, which demands a ransom payment to be provided with the decryption key they will need to recover the infected files after encrypting the victim's files.
Dealing with a Crystal Ransomware Infection
If your files have been encrypted by the Crystal Ransomware attack, you should take preventive steps. This is required because the files encrypted by the Crystal Ransomware cannot be recovered using the current technology. Computer users can restore their files by copying them over from a file backup, after removing the Crystal Ransomware infection itself with the help of a reliable security program. The combination of anti-malware software, file backups, and the implementation of good practices for handling spam emails can help to protect most computer users from infections like the Crystal Ransomware.
It is also strongly advised to avoid paying the Crystal Ransomware ransom, or the ransoms demanded by similar attacks. There are several reasons for this. The people responsible for the Crystal Ransomware attack may ignore the ransom payment, and instead, demand more money or ignore the victim altogether. Paying these ransoms also allow these people to target you for further attacks and continue developing and financing these infections.
SpyHunter Detects & Remove Crystal Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 34b93f1989b272866f023c34a2243978565fcfd23869cacc58ce592c1c545d8e | 0f27d1180d28e1bcaf4d66f6b51c087c | 0 |

Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.