File-locker Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 11 |
| First Seen: | March 1, 2017 |
| Last Seen: | January 20, 2023 |
| OS(es) Affected: | Windows |
The File-locker Ransomware is an encryption ransomware Trojan that is used to lock the victims' files with a strong encryption method. Once the File-locker Ransomware has made the victim's files inaccessible, the File-locker Ransomware will demand a fee to provide the decryption key, that is the only tool that can restore the affected files. The File-locker Ransomware is designed to target computer users in Korea, demanding a ransom payment of 50 thousand Won, which is equivalent to approximately 47 USD. Although the File-locker Ransomware's ransom demand is lower than most encryption ransomware Trojans that are active currently, PC security researchers advise PC users to refrain from paying the ransom associated with the File-locker Ransomware or contacting the people responsible for this attack.
Table of Contents
Protecting Your Computer from the File-locker Ransomware and Similar Threats
The best way to prevent the File-locker Ransomware attacks and similar infections is to be cautious when browsing the Web. Unsolicited file attachments, generally attached to spam email messages, are a prime way of distributing these threats and should be evaded at all costs. Fake file downloads also are a common source of these infections, and computer users should take steps to ensure that their computers are protected adequately, and software and other files are only downloaded from reputable sources. While anti-malware software and file backups are of vital importance in making sure that your computer does not fall prey to threats like the File-locker Ransomware, being cautious when browsing the Web remains the most effective way of keeping your computer safe from these threats.
How the File-locker Ransomware File-locker Ransomware Infection Works
After the File-locker Ransomware has encrypted the victim's files, it will display its ransom note in the form of a text file named 'Warning!!!!!!.txt.' The full text of this file is displayed in Korean and English, and reads as follows:
'한국어: 경고!!! 모든 문서, 사진, 데이테베이스 및 기타 중요한 파일이 암호화되었습니다!!
당신은 돈을 지불해야 합니다
비트코인 5만원을 fasfry2323@naver.com로 보내십시오 비트코인 지불코드: 1F1tAaz5x1HUXrCNLbtMDqcw6o5GNn4xqX 결제 사이트 hxxp://www.localbitcoins.com/
English: Warning!!! All your documents, photos, databases and other important personal files were encrypted!!
You have to pay for it.
Send fifty thousand won to fasfry2323@naver.com Bitcoin payment code: 1BoatSLRHtKNngkdXEeobR76b53LETtpyT Payment site hxxp://www.localbitcoins.com/'
The File-locker Ransomware uses a strong encryption algorithm in its attack, to make the victim's files completely inaccessible. The File-locker Ransomware will target the user-generated files. The File-locker Ransomware may encrypt the files that have the following file extensions:
.txt, .doc, .docx, .xls, .index, .pdf, .zip, .rar, .css, .lnk, .xlsx, .ppt, .pptx, .odt, .jpg, .bmp, .png, .csv, .sql, .mdb, .sln, .php, .asp, .aspx, .html, .xml, .psd, .bk, .bat, .mp3, .mp4, .wav, .wma, .avi, .divx, .mkv, .mpeg, .wmv, .mov, .ogg, .java, .csv, .kdc, .dxg, .xlsm, .pps, .cpp, .odt, .php, .odc, .log, .exe, .cr2, .mpeg, .jpeg, .xqx, .dotx, .pps, .class, .jar, .psd, .pot, .cmd, .rtf, .csv, .php, .docm, .xlsm, .js, .wsf, .vbs, .ini, .jpeg, .gif, .7z, .dotx, .kdc, .odm, .xll, .xlt, .ps, .mpeg, .pem, .msg, .xls, .wav, .odp, .nef, .pmd, .r3d, .dll, .reg, .hwp, .7z, .p12, .pfx, .cs, .ico, .torrent, .
The File-locker Ransomware will encrypt the affected files, changing their file extension by adding the string '.locked' to any affected files' names. Fortunately, computer users can restore their files with the password 'dnwls07193147.' This makes the File-locker Ransomware different from most ransomware Trojans, which use an attack from which computer users cannot recover. It is extremely necessary to have file backups in these cases. Fortunately, in the case of the File-locker Ransomware, computer users can easily restore access to the infected files thanks to the fact that the File-locker Ransomware uses a static password in its attack.
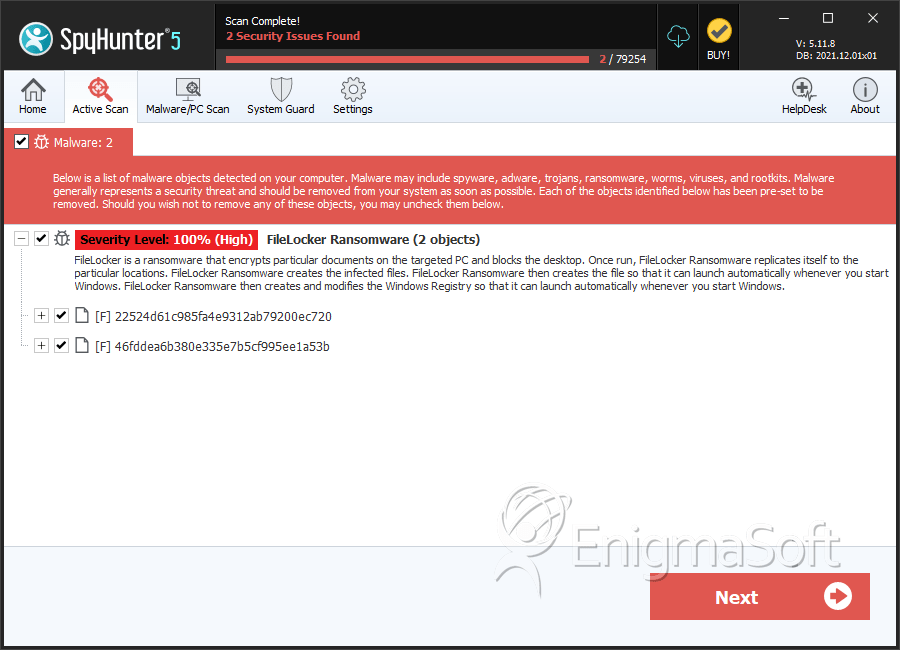
SpyHunter Detects & Remove File-locker Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 22524d61c985fa4e9312ab79200ec720 | 22524d61c985fa4e9312ab79200ec720 | 0 |
| 2. | 46fddea6b380e335e7b5cf995ee1a53b | 46fddea6b380e335e7b5cf995ee1a53b | 0 |

