Exte Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | July 15, 2017 |
| OS(es) Affected: | Windows |
The Exte Ransomware is a ransomware Trojan that is a variant of the Azer Ransomware, a known ransomware Trojan that was released relatively recently. The Exte Ransomware and several other ransomware Trojans belong to the CryptMix family of ransomware Trojans, which are used to encrypt the victims' data and then demand a ransom payment. The Exte Ransomware's previous version was released in June 2017, with the latest version of the Exte Ransomware appearing in mid-July 2017. The Exte Ransomware was observed on online anti-virus programs, where con artists often submit their ransomware Trojans to find out whether they can evade detection by established anti-virus software.
Table of Contents
How the Exte Ransomware Carries out Its Attack
The Exte Ransomware is currently being distributed through the use of corrupted spam email attachments, taking the form of corrupted Microsoft Word files commonly, which includes a macro script that downloads and installs the Exte Ransomware onto the victim's computer. Once the Exte Ransomware has entered a computer, it will begin encrypting the victim's files, using a strong encryption algorithm. Some of the file types that the Exte Ransomware will target in its attack include:
.aif, .apk, .arj, .asp, .bat, .bin, .cab, .cda, .cer, .cfg, .cfm, .cpl, .css, .csv, .cur, .dat, .deb, .dmg, .dmp, .doc, .docx, .drv, .gif, .htm, .html, .icns, .iso, .jar, .jpeg, .jpg, .jsp, .log, .mid, .mp3, .mp4, .mpa, .odp, .ods, .odt, .ogg,.part, .pdf, .php, .pkg, .png, .ppt, .pptx, .psd, .rar, .rpm, .rss, .rtf, .sql, .svg, .tar.gz, .tex, .tif, .tiff, .toast, .txt, .vcd, .wav, .wks, .wma, .wpd, .wpl, .wps, .wsf, .xlr, .xls, .xlsx, .zip.
The Exte Ransomware will use a strong encryption algorithm to make the file inaccessible, just like most encryption ransomware Trojans that are active currently. After encrypting the victim's files, the Exte Ransomware changes their extensions by adding the file extension 'EXTE' and encrypting the file's name so that it is replaced with what appear to be random characters. Once the Exte Ransomware encrypts a file, it will no longer open normally, and computer users will need a decryption key to access the affected file. The people responsible for the attack hold this decryption key until the victim pays a large amount of money. The Exte Ransomware takes the victim's files hostage until the victim pays a ransom. The ransom note, which informs the victim of the attack and demands payment, is contained in a text file that will show up on the infected computer's desktop. This file is named '_HELP_INSTRUCTION.TXT' and contains a short message instructing the victim to contact the con artists via email to receive further instructions. The following is the full text of the Exte Ransomware ransom note:
'Hello!
Attention! All Your data was encrypted!
For specific informartion, please send us an email with Your ID number:
exte1@msgden.net
exte2@protonmail.com
exte3@reddithub.com
We will help You as soon as possible!
DECRYPT-ID-[RANDOM CHARACTERS]'
Dealing with a Exte Ransomware Infection
Although it is possible to contact the people responsible for the Exte Ransomware, PC security analysts strongly advise against it. After the victim makes contact, the con artists will demand a ransom payment of several hundred dollars (typically between $500 and $1500 USD) in BitCoins. Malware analysts do not recommend paying this ransom. Besides that it is extremely unlikely that the affected files will be restored to their former state, paying these ransoms enables con artists to continue carrying out these attacks and developing new ransomware Trojans. The best protection against threats like the Exte Ransomware is to have backup copies of your files, on a removable memory gadget or the cloud preferentially. If the possibility of restoring the affected files from a backup exists, then the people responsible for the Exte Ransomware lose any power they have over the victim that enables them to demand a ransom payment. It also is necessary to use a reliable, fully updated anti-malware application.
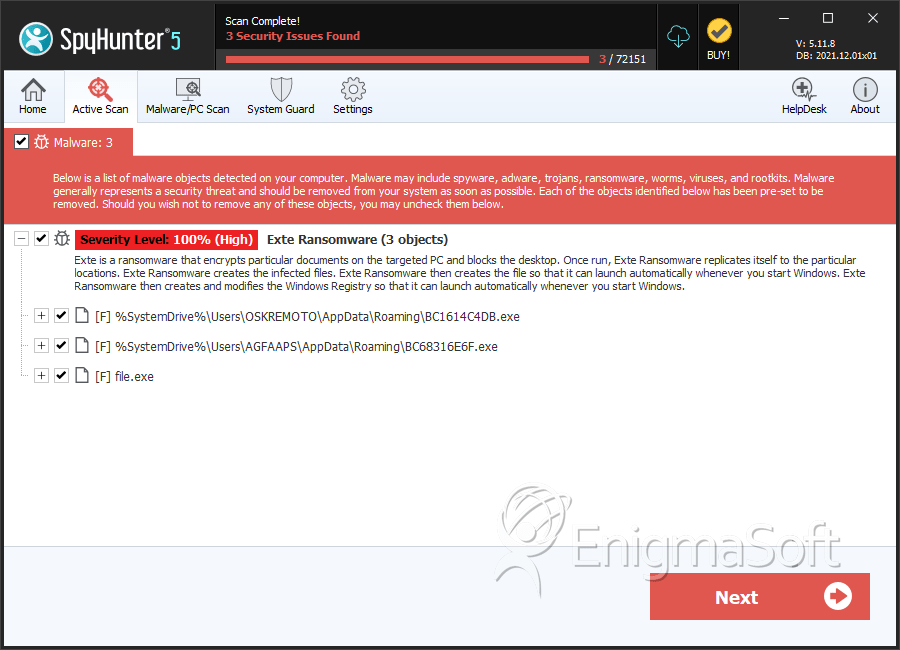
SpyHunter Detects & Remove Exte Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | BC1614C4DB.exe | a105b70a635f3aee7f6d020764c1ba92 | 1 |
| 2. | BC68316E6F.exe | 025274c91248e3a278d2b37173e2bd76 | 1 |
| 3. | file.exe | 1059676fbb9d811e88af96716cc1ffb5 | 0 |
| 4. | file.exe | 7d41a26f0d410d4303747c447ab76c3b | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.