EXTEN Ransomware
Ransomware remains one of the most damaging cyber threats out there. It can halt business operations, steal sensitive data, and lock individuals out of their personal files. Attackers continually develop new strains and more advanced methods, therefore protecting against these threats requires awareness, preparation, and disciplined security practices.
Table of Contents
Inside the EXTEN Ransomware Attack
EXTEN is a recently uncovered ransomware variant that encrypts data and demands payment for its release. During analysis, researchers observed that all compromised files were marked with the '.EXTEN' extension and had become unusable. A ransom note, stored as 'readme.txt', was also dropped in affected folders.
The note informed victims that the malware locked their files and they could only be recovered by paying the attackers 5 BTC—a sum exceeding half a million USD at current rates. Victims have a five-day deadline to comply. Beyond file encryption, the attackers threatened to leak exfiltrated data if the ransom was not paid, adding an extra layer of extortion.
Why Paying the Ransom is Risky
While the ransom note claims that payment is the only path to recovery, victims have no guarantee they will ever receive decryption keys. In many cases, ransomware operators simply pocket the payment and disappear. Even if files are restored, the stolen data may still be exposed on dark web marketplaces. Paying the ransom not only funds criminal activity but also increases the likelihood of future targeting.
Removing EXTEN from the system is necessary to halt further encryption, but this will not restore locked data. Recovery is only possible through secure, pre-existing backups. Without them, most victims face permanent data loss.
Distribution Tactics Used by EXTEN
Like other ransomware families, EXTEN relies on standard but effective distribution methods. The most frequent distribution method is malicious emails with infected attachments or links. These files often look like invoices, delivery notices, or other routine documents, tricking victims into opening them.
Other infection routes include compromised websites delivering drive-by downloads, pirated software, fake system updates, and malware bundled into files shared on peer-to-peer networks. Trojans acting as loaders or backdoors can also introduce ransomware into systems, and in some cases, ransomware can spread within local networks or via removable media.
Building Strong Defenses Against Ransomware
Preventing an EXTEN ransomware attack requires a proactive, multi-layered approach to cybersecurity. Backups are the cornerstone of recovery—users should maintain multiple copies of important files stored in different locations. At least one backup must remain offline or on a service isolated from the primary network to avoid being encrypted along with the system.
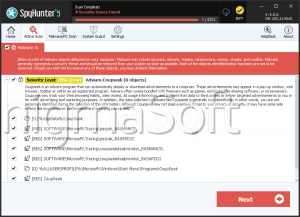
Reliable antivirus and endpoint protection software provide an additional layer of defense by identifying and blocking threats in real time. However, technology alone is not enough—user awareness is equally critical. Suspicious emails should be treated cautiously, and attachments or links from unknown senders must not be opened.
Downloading software only from official and verified sources and keeping operating systems and applications patched prevent attackers from exploiting known vulnerabilities.
Organizations can further enhance their resilience by segmenting networks, enforcing the principle of least privilege, and requiring multi-factor authentication for sensitive accounts. Regular cybersecurity training for employees helps reduce the risk of human error, which is often the weakest link in security.
Final Thoughts
EXTEN ransomware pairs file encryption with threats of data leaks for a powerful double-extortion strategy. Paying ransoms rarely solves the problem. The best defense lies in preparation: secure backups, strong security software, and cautious digital habits.