Exploit:JS/DonxRef.A
Exploit:JS/DonxRef.A is a JavaScript object that builds shellcode. Exploit:JS/DonxRef.A may be embedded within other document files, such as harmful HTML files. Exploit:JS/DonxRef.A proliferates via infected websites or infected HTML content inserted into a spam emailExploit:JS/DonxRef.A may strive to exploit a number of vulnerabilities in Java, Windows and Adobe Flash Player to launch other malware infections on the affected PC. Exploit:JS/DonxRef.A may detect a component of a particular exploit kit referred to as 'KaiXin' or 'Gong Da'. If the computer system contains a vulnerable version of these software products, Exploit:JS/DonxRef.A downloads and runs arbitrary files. Exploit:JS/DonxRef.A checks if the machine is vulnerable to the following:
CVE-2011-3544
CVE-2012-0507
CVE-2012-1723
CVE-2012-4681
CVE-2012-5076
CVE-2012-1535
Exploit:JS/DonxRef.A also exploits a vulnerability in Microsoft XML Core Services patched with the issue of Microsoft Security Bulletin MS12-043, (CVE-2012-1889).
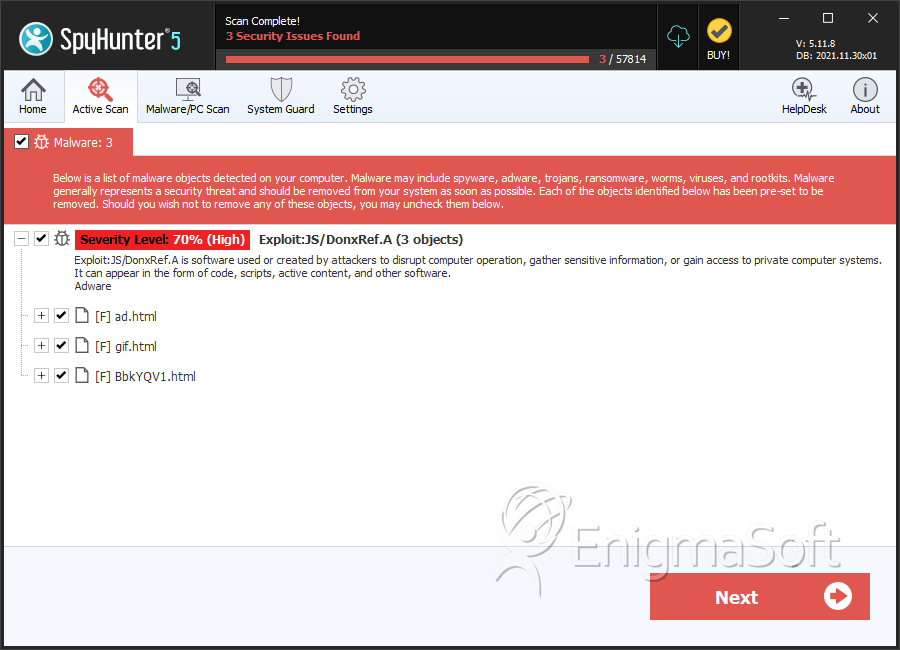
SpyHunter Detects & Remove Exploit:JS/DonxRef.A
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | ad.html | b7300c8ebe8d1d88a083ba9a65638ee2 | 0 |
| 2. | gif.html | 87e801461496495c9990107c4cc25ac7 | 0 |
| 3. | BbkYQV1.html | 829b479c52b68a68c4397fb37f563f2f | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.