Epor Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 161 |
| First Seen: | January 19, 2011 |
| Last Seen: | March 31, 2023 |
| OS(es) Affected: | Windows |
Epor Ransomware Image
The Epor Ransomware is another crypto locker threat classified by infosec researchers as belonging to the infamous and quite prolific STOP/DJVU family of malware threats. Although new variants of this family are detected almost daily, that doesn't diminish their capacity for destruction in the slighted. The Epor Ransomware is not an exception.
If the threat manages to infiltrate a computer successfully, it will deploy its encryption process rapidly, resulting in nearly all files being locked with a powerful cryptographic algorithm. Victims will be prevented from accessing or using any of their personal or business files effectively, including documents, pictures, databases, spreadsheets, PDFs, video, audio, etc. Each file that has been enciphered by the Epor Ransomware will have '.epor' appended to its original filename as a new extension. The cybercriminals behind this threat deliver their instructions in the form of text files named '_readme.txt.' A copy of the note-carrying file will be placed in every folder containing encrypted data.
Victims of the Epor Ransomware are told that to receive the decryptor tool and key necessary for the restoration of their data, they will have to send the hefty sum of $980 to the criminals. The price can be reduced by as much as 50% to $490 if the affected users establish contact with the hackers in the first 72 hours following the Epor Ransomware infection. To do so, users are supposed to send an email message to either the main email address at 'helpmanager@mail.ch' or the reserve one at 'restoremanager@airmail.cc.' A single file can be attached to the message to be decrypted for free.
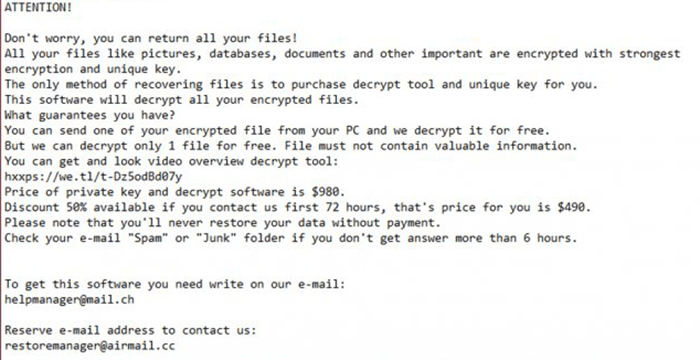
The full text of the Epor Ransomware's note is:
'ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-Dz5odBd07y
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your email "Spam" or "Junk" folder if you don't get answer more than 6 hours.
To get this software you need write on our email:
helpmanager@mail.ch
Reserve email address to contact us:
restoremanager@airmail.cc
Your personal ID:'

