EggShell
 The EggShell malware is a hacking tool that is capable of targeting both OSX systems and iOS devices. This threat appears to operate as a post-exploitation utility mainly. The EggShell malware has a long list of capabilities. Thanks to the wide variety of capabilities of the EggShell threat, the attackers will be able to collect not only information about their targets but also launch long-lasting reconnaissance campaigns. The campaigns that include the EggShell malware are known to be very threatening, as this feature-rich threat is able to allow the attackers to gain nearly full control over the infected device.
The EggShell malware is a hacking tool that is capable of targeting both OSX systems and iOS devices. This threat appears to operate as a post-exploitation utility mainly. The EggShell malware has a long list of capabilities. Thanks to the wide variety of capabilities of the EggShell threat, the attackers will be able to collect not only information about their targets but also launch long-lasting reconnaissance campaigns. The campaigns that include the EggShell malware are known to be very threatening, as this feature-rich threat is able to allow the attackers to gain nearly full control over the infected device.
Some of the capabilities of the EggShell threat include:
- Take screenshots of the victim’s desktop and active windows.
- Modify the iTunes service.
- Modify the iMessage service.
- Download, upload, delete, move, and copy files from the infected host.
- Monitor, alter and collect data from the user’s clipboard.
- Collect cookies and other information from Facebook.
- Use the microphone and camera of the compromised device to record audio and video, which is then transferred to the C&C (Control & Command) server of the attackers.
- Present the user with bogus prompts designed to phish their administrator credentials.
Malware researchers speculate that the EggShell threat is likely being propagated via macro-laced documents, which are attached to phishing emails. The corrupted documents in question are programmed to exploit known vulnerabilities in the Microsoft Office service.
Table of Contents
How Does EggShell Get on Computers?
Most casual Mac users are under the mistaken belief that the operating system is watertight and doesn’t get infected by viruses. The reality is that plenty of threats have found their way around standard Apple security features. As an example of this, EggShell allows even inexperienced programmers to attack Mac computers in a variety of ways. The backdoor trojan works as spyware, too, giving complete functionality to criminals.
The primary way that EggShell propagates is through the dubious cryptocurrency tracking app CoinTicker. The virus hides inside the installation program for CoinTicker, and it isn’t the only one that does. EvilOSX has also been seen hiding behind the CoinTicker application. It’s also possible that the virus spreads through more traditional means, such as malspam campaigns and illegal downloads.
What Does EggShell Do?
The first thing EggShell will do is establish persistence on the infected system. It does this by using a cron – the Unix version of a scheduled task. If a user enters their password information to verify the installation, then EggShell gains root access to the computer and gains the functionality of a rootkit.
Researchers warn that EggShell can do all kinds of things, including;
- Download and execute files from the internet and upload information to a C2 (Command and Control server)
- Collect information, including taking screenshots, controlling microphones, cameras, and other peripheral devices, and creating copies of anything copied to the clipboard
- Target Apple-specific products and services, such as iTunes and iMessage
- Steal login information from social networking services like Facebook
- Generate spoofed OS notification popups to steal more credentials from users
To execute commands, EggShell must first plant their corresponding malicious payloads into the targeted machine. However, those payloads do not come all at once – a master payload takes precedence in order to set up a secure connection between the host machine and EggShell’s server. Once established, the connection paves the way for a remote EggShell session. An active session allows for remote code execution, which could ultimately result in keystroke emulation (via the USB-injected Teensy payload), tab completion, unauthorized camera usage, and so on. EggShell can perform all these operations thanks to a particular security flaw present in the iOS 9.3.3 Webkit.
Multisession Capability
While EggShell can only establish a single session to a PC, it is fully capable of running parallel sessions to two or more targeted machines at the same time. For example, EggShell could simultaneously adjust screen brightness on one connected computer, take pictures through iSight on another, change the volume of a third, view system information on a fourth, etc. The table below contains a list of select commands EggShell can execute on a targeted device depending on its software platform.
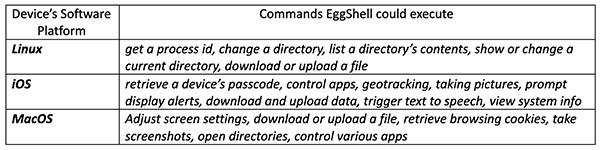
The operations laid out in the table above are but a taste of what the EggShell tool is capable of doing. For some reason, however, the app is not available in the official Apple App Store and its developers are currently using alternative distribution methods instead.
How to Avoid EggShell
Researchers note that EggShell isn’t more sophisticated than the average trojan, but it is still a threat to watch out for and avoid. This flexible trojan can perform all manner of spying operations. Threat actors could use the virus to hijack your account and spread Eggshell further, collect information to sell for profit on the dark web, and install other viruses and malware. Given that EggShell was created for Apple devices, the fact the virus even exists is a warning about the power of default security settings.
One way to tell if your computer is infected is that you will get a lot of popups asking for credentials. Outside of hiding within EvilEgg and CoinTicker, EggShell can spread in more traditional ways. Targets have been hit with exploitative content such as documents with macros that install the virus. These documents are disguised as resumes, invoices, and other important documents.
The easiest way to avoid infection is to not allow macros on documents from unknown sources. Also, be sure to keep any programs – especially security programs – updated to prevent software exploits. There’s nothing particularly new about how EggShell operates, but what it can do is more than enough to encourage anyone to practice better security habits.

