Donald Trump Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | September 27, 2016 |
| Last Seen: | April 16, 2021 |
| OS(es) Affected: | Windows |
The Donald Trump Ransomware is a ransomware Trojan that tries to take advantage of the current public consciousness about the election to carry out a ransomware attack. However, in a way that fits considering this malware's theme, the Donald Trump Ransomware doesn't encrypt the victim's files, but instead 'builds a wall around them,' which makes them inaccessible in a superficial way. There is nothing new about the appearance of the Donald Trump Ransomware and other election-themed threats. The Donald Trump Ransomware is in its development version currently and, as the election rolls along, it's highly likely that this and other election-themed threats will be developed.
Table of Contents
Trending News and Threats Like the Donald Trump Ransomware
Threat creators tend to take advantage of trending news items to create threats and social engineering tactics that are likely to attract clicks. For example, during the recent Olympic Games, PC security analysts uncovered numerous threats themed around the Olympics and targeting computer users in Brazil. If computer users receive an email message containing information about a topic that is trending in the news, it's more likely that they will open a related attachment or click on an embedded link, especially if the email is written convincingly. This is the approach that threats like the Donald Trump Ransomware may take for distribution purposes.
The Ineffective Donald Trump Ransomware
The Donald Trump Ransomware is being developed currently and seems first to have been compiled in August of 2016. It is possible that the Donald Trump Ransomware will never be distributed to victims, however. The Donald Trump Ransomware does contain some content that suggests that it could encrypt the victims' files using the AES encryption. However, in its current form, the Donald Trump Ransomware does not encrypt the victims' files. The Donald Trump Ransomware searches for files in the targeted folder and uses 'base64' to encode the file names by adding the .ENCRYPTED extension to their ending. The Donald Trump Ransomware targets a specific list of file extensions, which include the following:
.zip, .mp3, .7z, .rar, .wma, .avi, .wmv, .csv, .tax, .sidn, .itl, .mdbackup, .menu, .icarus, .litemod, .sav, .lvl, .raw, .flv, .m3u, .xxx, .pak, .jpg, .png, .docx, .doc, .ppt, .odt, .csv, .jpeg, .psd, .rtf, .cfg, Minecraft, alts.json, .wolfram, .dat, .dat_mcr, .mca, .Ink, .pub, .pptx, .php, .html, .yml, .sk, .txt, .mp4, .vb, .swf, .ico, .xcf, bukkit.jar, .log, .sln, .ini, .dll, .xml, .tex, .assets, .resource, .java, .js, .css, .gif.
The Donald Trump Ransomware attack is not particularly serious since computer users can simply click on the 'Unlock' button to restore the files to their original file names.
Beware of Email Attachments During the Election Season
Any email attachments received during this election season should be handled carefully, especially if they contain any content referencing current news stories. Many computer users may be tempted to open these email attachments in an attempt to receive important news about electoral developments. However, threat creators know this is the case and will take advantage of the computer users' curiosity to infect their computers with threats like the Donald Trump Ransomware. Only accept online news from trusted sources, directly from their websites or news feeds. Unsolicited email attachments are not the most trustworthy source for news!
How the Donald Trump Ransomware may be Distributed
The Donald Trump Ransomware is being distributed in a spam email message that pretends to be a newsletter with news about the 2016 presidential elections. The email contains a corrupted attachment that redirects the victim to an attack website. When the victim visits this website, a corrupted executable file named 'CRPT-TRX.exe' is downloaded to the victim's computer. Once the file is on the victim's computer, it carries out the Donald Trump Ransomware attack. Fortunately for computer users, the Donald Trump Ransomware infection is not fully implemented and is harmless in its current state.
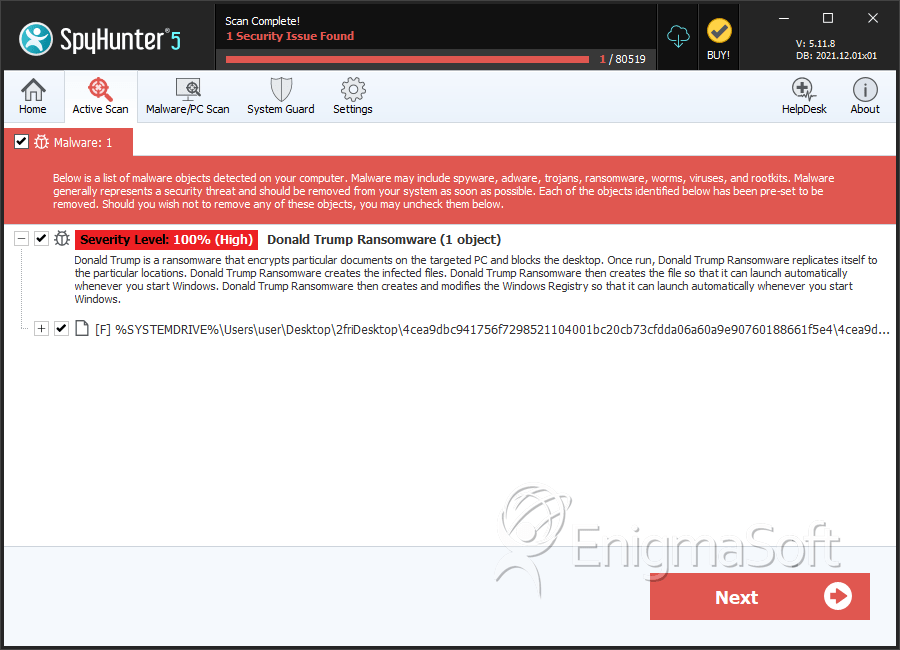
SpyHunter Detects & Remove Donald Trump Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 4cea9dbc941756f7298521104001bc20cb73cfdda06a60a9e90760188661f5e4 | e4d1951b179a1de9d22f83227f1026a6 | 1 |

