DeadSec-Crypto Ransomware
The DeadSec-Crypto Ransomware is an encryption ransomware Trojan that was first observed on May 18, 2017. The DeadSec-Crypto Ransomware is being used in attacks against Portuguese speakers. The DeadSec-Crypto Ransomware is typically being delivered using corrupted spam email attachments that use various social engineering tactics to lure computer users into opening the attachment. The attached files will use corrupted macros to exploit vulnerabilities in the victim's computer and download and install the DeadSec-Crypto Ransomware (the DeadSec-Crypto Ransomware will be installed to a temporary directory in the AppData folder of Windows). The DeadSec-Crypto Ransomware will run in the background after being installed, scanning the infected computer's hard drives and encrypting its contents using a strong encryption algorithm. The DeadSec-Crypto Ransomware is running as 'WindowsApplication1.exe' on the infected computers. The DeadSec-Crypto Ransomware receives its name because it displays a ransom note in the form of a program window titled 'DeadSec-Crypto Ransomware v2.1' on the infected computer.
Table of Contents
How the DeadSec-Crypto Ransomware can Extort Computer Users
The DeadSec-Crypto Ransomware uses a combination of the RSA and AES encryptions to make the victims' data inaccessible. The DeadSec-Crypto Ransomware seems to be an independent threat project rather than belonging to a larger family of ransomware (however, it does contain various elements that may have been lifted or copied from other ransomware Trojans active today). The DeadSec-Crypto Ransomware will scan the victim's drives for user-generated files, such as video and audio files, text, databases, and files generated with software such as Microsoft Office or Adobe Photoshop. Using its encryption algorithm, the DeadSec-Crypto Ransomware will encrypt these files, making them unusable, and add the file extension '.locked' to the end of each affected files' name. Unfortunately, once a file has been encrypted by the DeadSec-Crypto Ransomware attack, it becomes unrecoverable without the decryption key. After encrypting the victim's files, the DeadSec-Crypto Ransomware will display a ransom note in the form of a program window. Below is the full text of the DeadSec-Crypto Ransomware ransom note, translated from the original in Portuguese:
'Why did I receive this?
You are a victim of a ransomware and all your data was encrypted by DeadSec all files are with .locked extension and with the SHA256SUM hash virtually impossible to recover. We have all your data including passwords, documents and files among other personal things like Cards and etc.
What to do?
You will need to donate an amount of 0.05 Bitcoins that in Reals = $ 100.00 to the address below, to donate the amount you need to buy Bitcoins with real money at: https://blockchain.info/wallet/#/signup After sending the bitcoins to the address, we will confirm the transaction and send a key to your email and you will have your files and passwords.
You have the deadline: 1 Week thecrackerOday@gmail.com
Key: [TEXT BOX] Address: 1Mx4Zgz5nYmFPPSUS6TbF2SfVP4xfcghBu
If you do not send the amount in 1 Week, we will leak all your data'
Dealing with a DeadSec-Crypto Ransomware Infection
PC security researchers strongly advise computer users to refrain from paying the DeadSec-Crypto Ransomware ransom. It is well documented that these people may ignore the victims' payments, demand more money, or simply reinfect the victim's computer after the payment has been made. Instead, it is important to have file backups to restore any data that has been lost in one of these attacks. Backup copies when sotred on an external memory device or the cloud allows computer users to recover their data in the event of one of these attacks and make the attack ineffective completely. Apart from file backups, it is also important to have a reliable security program that is fully up-to-date to remove the DeadSec-Crypto Ransomware infection itself and, in many cases, intercept it before it carries out its attack. Since the DeadSec-Crypto Ransomware is mostly distributed using corrupted email attachments, learning to handle this content safely is a big part of protecting your computer from these attacks.
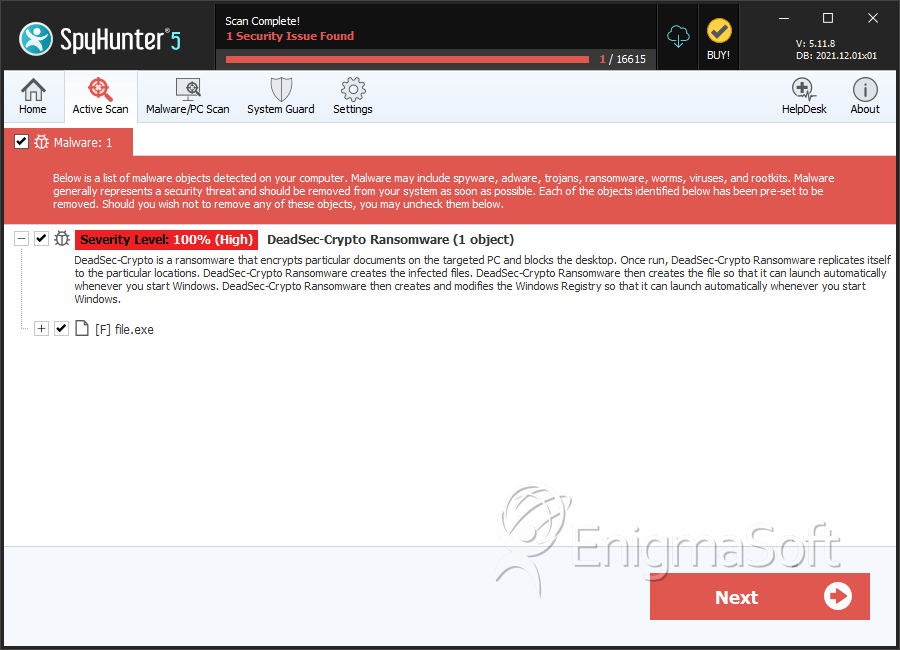
SpyHunter Detects & Remove DeadSec-Crypto Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 87a6a44dd175546d6cb7f840ce6a22ae | 0 |

