CYR-Locker Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 4 |
| First Seen: | March 3, 2017 |
| Last Seen: | April 11, 2022 |
| OS(es) Affected: | Windows |
The CYR-Locker Ransomware is a ransomware Trojan that is used to force computer users to pay large amounts of money to recover their files, which become compromised during the attack. The CYR-Locker Ransomware encrypts its victims' files, as well as carries out various other operations on the victim's computer. The CYR-Locker Ransomware demands the payment of a large ransom in exchange for the decryption key required to decrypt the affected file. During the attack, the CYR-Locker Ransomware demands payment within 24 hours under the threat of deleting the victim's files permanently. The most common way in which the CYR-Locker Ransomware is distributed is through corrupted email attachments, which will use a variety of tactics to trick computer users into opening the attached file or clicking on an embedded link that leads to an attack website.
Table of Contents
How the CYR-Locker Ransomware Trojan Attack Works
Once the CYR-Locker Ransomware has been installed, it will install two corrupted executable files; one that is named with random numbers and the other named CYR-Locker.exe. Once the CYR-Locker Ransomware has begun its attack, it will work in the background to infect the victim's computer and encrypt the victim's file. Once the victim's files have been compromised, the CYR-Locker Ransomware will change the image on the victim's screen and display a ransom note. Apart from encrypting the victim's files, though, the CYR-Locker Ransomware also will change the Windows' settings, delete the Shadow Volume Copies of the victim's files, and other threatening operations. The CYR-Locker Ransomware will use a strong encryption method to encrypt the victim's files, targeting various files that may include text files, databases, PDF files, media files, documents created by various applications, images, and countless others. The files encrypted by the CYR-Locker Ransomware become unreadable. The CYR-Locker Ransomware changes the affected computer's Desktop wallpaper image into the CYR-Locker Ransomware's ransom note, which alerts the victim of the attack and demands the payment of a ransom. The full text of the ransom note is displayed below:
'Your personal files are encrypted by CYR-Locker.
Your documents, photos, databases and other important files have been encrypted with strongest encryption and unique key, generated for this computer.
Private decryption key is stored on a secret Ineternet server and nobody can decrypt your files until you pay and obtain the private key.
You only have 24 hours to submit the payment. If you do not send money within provided time, all your files will be permanently crypted and no one will be able to recover them. I need money amount from you just 10 millions send through Bitcoin into account: CYR-Locker.
WARNING! DO NOT TRY TO GET RID OF THE PROGRAM YOURSELF. ANY ACTION TAKEN WILL RESULT IN DECRYPTION KEY BEING DESTROYED. YOU WILL LOSE YOUR FILES FOREVER. ONLY WAY TO KEEP YOUR FILES IS TO FOLLOW THE INSTRUCTION.'
Dealing with the CYR-Locker Ransomware
PC security researchers strongly advise computer users to avoid paying the CYR-Locker Ransomware ransom, since this allows the con artists to continue creating these threats and carrying out more attacks. Unfortunately, the files that have been compromised during the CYR-Locker Ransomware attack become impossible to recover without access to the decryption key. The same encryption technology that is used to keep the computer users' data safe is used by these people to ensure that the affected files are not readable. Because of this, having file backups of all files is an essential aspect of dealing with the CYR-Locker Ransomware infections.
You should have backup copies of all files stored on an external memory device or the cloud. If computer users affected by the CYR-Locker Ransomware attack can recover their files by restoring them from a backup copy, then the people responsible for the CYR-Locker Ransomware attack lose any leverage they have over the victim that allows them to demand payment of a ransom. Apart from file backups, you should take precautions when dealing with unsolicited email messages and attachments, as well as have a reliable security application that is up-to-date.
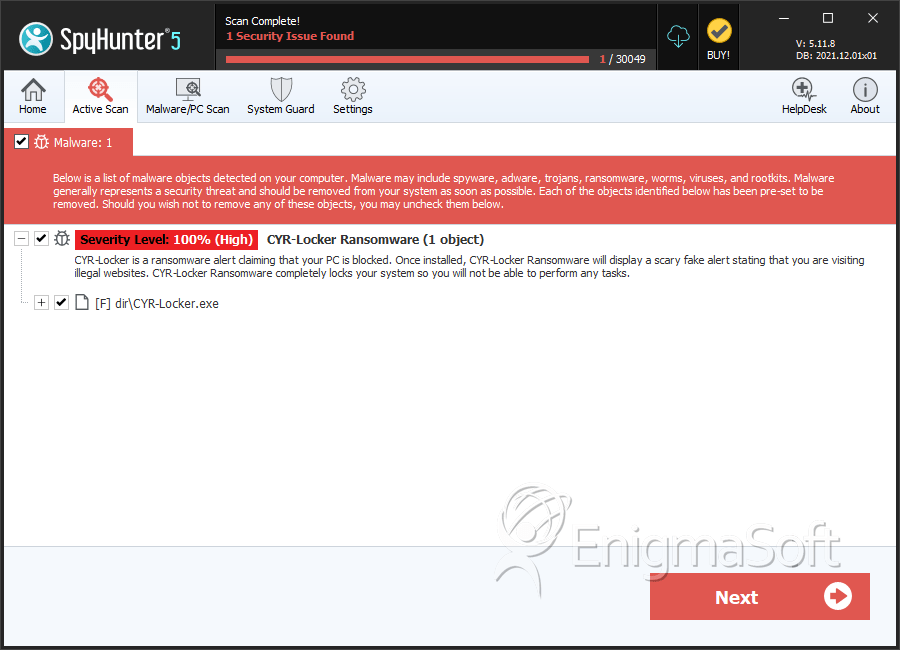
SpyHunter Detects & Remove CYR-Locker Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | CYR-Locker.exe | 295837a0503871bdccb8b78f5f54f5a0 | 2 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.