Cycbot
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
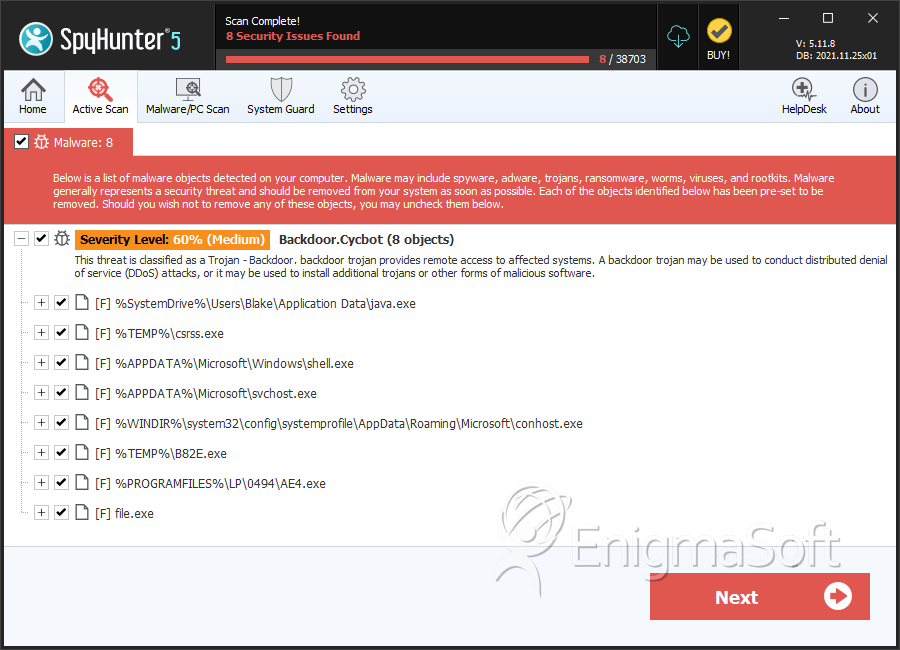
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 13,062 |
| First Seen: | October 1, 2010 |
| Last Seen: | July 7, 2022 |
| OS(es) Affected: | Windows |
First detected in early 2011, Cycbot is a dangerous backdoor Trojan used to install other malware, particularly fake security programs. ESG security researchers consider that Cycbot is a severe threat to your system's security and that Cycbot should be disabled right away with the aid of a competent anti-malware program. Although a Cycbot infection will not usually cause explicit symptoms, Cycbot will almost never attack alone, meaning that Cycbot will often be detected due to the effects of other malware installed due to the backdoor that Cycbot establishes into the victim's system.
Table of Contents
How the Cycbot Backdoor Trojan Works
Cycbot is designed to allow criminals to gain access to the infected computer. With Cycbot, a remote attacker can gain the ability to control the infected computer. Once Cycbot is installed on the victim's computer, this Trojan establishes an unauthorized connection with a remote server. Once the connection has been made, Cycbot receives orders, updates and configuration data from the people behind the Cycbot infection. Cycbot can receive updates, connect to specific websites or download and install malicious files. Due to its backdoor capabilities, criminals can integrate the infected computer into a botnet, a vast network of infected systems. With thousands of infected computers under their command, criminals can carry out DdoS attacks on specific targets (overloading a specific target with requests in order to shut it down) or use the infected computer systems for money laundering or spam email operations.
An Analysis of a Cycbot Attack
Cycbot is designed to make dangerous changes to the Windows Registry that allow Cycbot to run automatically as soon as the infected computer starts up. As soon as Cycbot is installed, Cycbot will be contained in executable files in the AppData folder in the system folder. Cycbot connects to one of a large list of web servers associated with this threat. Some examples of servers that have been linked to the Cycbot Trojan include the following:
blenderartists[dot]org
136136[dot]com
motherboardstest[dot]com
zonejm[dot]com
qudeteyuj[dot]cn
178.63.123.226
dolbyaudiodevice[dot]com
freeonlinedatingtips[dot]net
pcdocpro[dot]com
sharewareconnection[dot]com
xy95[dot]cn
protectyourpc-11[dot]com
historykillerpro[dot]com
zoneck[dot]com
Cycbot has been linked to keyloggers designed to steal sensitive data and fake security programs such as those belonging to the FakePAV or the FakeVimes families of malware. It is important to understand that a Cycbot infection will endanger other systems in contact with your computer. Because of this, removing Cycbot and malware installed by this backdoor Trojan should be an immediate priority.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| AVG | Win32/Cryptor |
| Ikarus | Backdoor.Win32.Gbot |
| AhnLab-V3 | Backdoor/Win32.Gbot |
| Sophos | Troj/CycBot-R |
| AntiVir | TR/Kazy.48327 |
| DrWeb | BackDoor.Gbot.1851 |
| BitDefender | Gen:Variant.Kazy.48327 |
| Kaspersky | Backdoor.Win32.Gbot.qvo |
| Avast | Win32:Cycbot-PM [Trj] |
| NOD32 | a variant of Win32/Kryptik.XGT |
| K7AntiVirus | Backdoor |
| McAfee | BackDoor-EXI.gen.aa |
| Ikarus | PWS.Win32 |
| DrWeb | BackDoor.Gbot.53 |
| Kaspersky | Trojan.Win32.Jorik.Gbot.cql |
SpyHunter Detects & Remove Cycbot
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | csrss.exe | f47aadf4ff478b19588157650bda890d | 577 |
| 2. | csrss.exe | dac0d9d8376ffa1d6cf62f5490407fb6 | 479 |
| 3. | csrss.exe | 1c188b925b3cfa89d89e41c2f1bba8a1 | 368 |
| 4. | csrss.exe | ed4160b1baa565213d64006437191e05 | 284 |
| 5. | csrss.exe | 2f880685106424359d20662497cdf65f | 248 |
| 6. | csrss.exe | d74ff12da848dcbd7b6d3696d9c7a4ec | 195 |
| 7. | csrss.exe | 7f39241b3444a3576708320afbf7a0fc | 180 |
| 8. | csrss.exe | 5e7958d860d40a4f60e9228a6a499844 | 168 |
| 9. | csrss.exe | d6f90ef3c7fbd500e3541100f4112294 | 157 |
| 10. | csrss.exe | b8d57d709ce681bce0b2f592a3ed18f5 | 150 |
| 11. | csrss.exe | 6701aace873cb3c3f8f23f0decb8640e | 150 |
| 12. | csrss.exe | ea634e7d683f995c833fc8eba4e69843 | 147 |
| 13. | csrss.exe | 0c95a41daa93394853f55153260f7972 | 131 |
| 14. | csrss.exe | 71be4948aa4472ef4e75ffaf99a55300 | 112 |
| 15. | java.exe | 1529e457137f7d1b0ffd9d7fb538ad37 | 108 |
| 16. | csrss.exe | 2e7f5cbef3f0e1443bb3dff26b989bf7 | 102 |
| 17. | csrss.exe | b2734c93280818f292d61084a89e8939 | 99 |
| 18. | csrss.exe | 1352ec65f1b06affdf9b0c6a6cb08701 | 97 |
| 19. | csrss.exe | dcd9adde88908cacbdbe025b507d9f41 | 95 |
| 20. | csrss.exe | b28d47077367c7dfe56ca519e5bebcfe | 90 |
| 21. | csrss.exe | ee6203d2157255de4ab8549595e503e7 | 85 |
| 22. | csrss.exe | b35be1565a07f3e1a2f95431bc50bf1c | 85 |
| 23. | conhost.exe | db884b05bebde8c010d917dd91e37e72 | 3 |
| 24. | AE4.exe | f4086ebc9edb0957dff0d4f836cfbab6 | 1 |
| 25. | file.exe | e1bb90ddf62072afea134bfc0f6fe7b1 | 1 |
| 26. | file.exe | df365fd69880bbb15cf1f87a049aa24c | 0 |
| 27. | File.exe | a3e06ec580bfc4757bf18feb2bcb1139 | 0 |
| 28. | file.exe | af1f2e45efcae2df0f53f10c68e8655b | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.