Backdoor.Cycbot.A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 16,271 |
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 2,661 |
| First Seen: | November 30, 2010 |
| Last Seen: | June 23, 2023 |
| OS(es) Affected: | Windows |
Backdoor:Win32/Cycbot.A is a backdoor Trojan that allows attackers to obtain remote unauthorized access and control of a corrupted PC. Once a computer is infected, Backdoor:Win32/Cycbot.A connects to a specific remote server to receive further intructions from attackers that can instruct Backdoor:Win32/Cycbot.A to proliferate to other cPCs by scanning for network shares with weak passwords, exploiting Windows vulnerabilities, or possibly propagating through backdoor ports opened by other families of malicious programs. Backdoor:Win32/Cycbot.A may also allow attackers to execute other backdoor functions, such as initiating denial of service (DoS) attacks and restoring system information from corrupted machines. Backdoor:Win32/Cycbot.A can also log keystrokes or steal personal information. It is strongly advised to remove Backdoor:Win32/Cycbot.A as soon as possible.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Panda | Trj/KillFiles.BF |
| AVG | SHeur3.BBZH |
| Fortinet | W32/Swisyn.ALXY!tr |
| Ikarus | Backdoor.Win32.Goolbot |
| AhnLab-V3 | Win-Trojan/Downloader.77312.V |
| Antiy-AVL | Trojan/Win32.Swisyn.gen |
| eTrust-Vet | Win32/Swisyn.CB |
| AntiVir | TR/Swisyn.alxy.2 |
| DrWeb | Trojan.DownLoader1.23379 |
| BitDefender | Trojan.Generic.4806317 |
| Kaspersky | Trojan.Win32.Swisyn.alxy |
| Symantec | Backdoor.Cycbot |
| F-Prot | W32/Trojan3.CAQ |
| McAfee | Generic.dx!ulb |
| AVG | Cryptic.BKE |
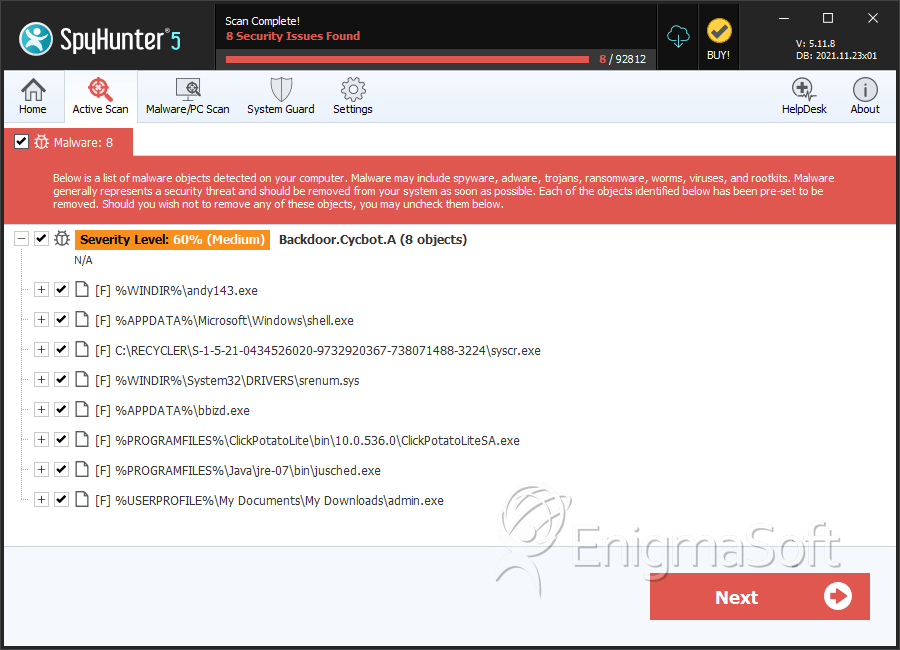
SpyHunter Detects & Remove Backdoor.Cycbot.A
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | andy143.exe | 00acbad51d1c87712fef2a59bbd9f749 | 55 |
| 2. | shell.exe | fbd7aed3145a59a7ce352b9439fd4857 | 49 |
| 3. | srenum.sys | 83c7e2a7add3a7de3e9ef9cc457f7546 | 30 |
| 4. | ClickPotatoLiteSA.exe | 10e871835aeff742826cf6748c3640b1 | 21 |
| 5. | jusched.exe | f83c617b55a53db1fc9bd68c9c732192 | 13 |
| 6. | admin.exe | 01561b954bcf7a8d70e633591b988281 | 13 |
| 7. | movie[1].exe | ae6b3daea687270874389f971ebd18b2 | 12 |
| 8. | updates.exe | 58c5604ac47dd9e67a807bab521e490b | 10 |
| 9. | chkntfs.exe | 6ea03b0a1296b6a02c7272b31a011d8e | 7 |
| 10. | msvmiode.exe | 4aa952ad15927f9847c379e5459ead51 | 7 |
| 11. | api-ms-win-core-misc-l1-1-032.dll | 137f8e711c3869a1c065db1f599705b3 | 6 |
| 12. | updates.exe | 414d64e82901049368e05b74312143e6 | 6 |
| 13. | ajyWlxBiFK.exe | 0f9c3aa84453b91cdec2c9152e10be3b | 6 |
| 14. | o41uVnF8.exe | ff3a19654f34476e18c6309dd0e7350b | 4 |
| 15. | sysi.cpl | 4e8b68f22e1f0a0f3201465e5764e8d0 | 3 |
| 16. | windowswindows2.7.2600.2180.exe | 60db36352c5cd2c0bd18062f996db3c7 | 3 |
| 17. | bbizd.exe | 88dc8cd3aa31adb39587ea09692f07df | 3 |
| 18. | fbx.exe | 97c2dd327917f8df38d005b2b968a3db | 2 |
| 19. | flipopia.exe | f81e26306f6244f964038e08e51e809f | 1 |
| 20. | quicktimeresourcesquicktime.exe | 810f4c861c7bc9728e14fad39f18ad5d | 1 |
| 21. | IEBrowserEvents.dll | 3a2de3fe969bd90072b0ebc626a09ec2 | 1 |
| 22. | lkbfmln.exe | b180feded7e9ee1aad000f64ff92f6b3 | 1 |
| 23. | RHCPL.exe | f1149ee97164d239304fabac6234b8ba | 1 |
| 24. | RegEasyCleaner.exe | 3cc0c78b78234e37484e4a167720a086 | 1 |
| 25. | regprov.dll | c183b8821e561334ee0d9088f78d060e | 1 |
| 26. | printedit.dll | 9cb14fff0365220d4ae00f18495e80d5 | 1 |
| 27. |
C:\Documents and Settings\ |
||
| 28. |
C:\Documents and Settings\ |
||
| 29. |
C:\Documents and Settings\ |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.