Cuba Ransomware
Cuba Ransomware Image
Among the most prevalent threats online are data-encrypting Trojans, also referred to as ransomware. Creating ransomware threats is rather easy as cyber crooks can simply use a ransomware building kit and quickly create a brand-new file-locking Trojan ready for distribution. One of the newest threats of this class is called Cuba Ransomware. Upon studying this new ransomware threat, malware researchers uncovered that this is a variant of the Buran Ransomware.
Propagation and Encryption
The majority of ransomware authors tend to use spam email campaigns as a means of propagating their malicious creations. Usually, an email of this kind would consist of a fraudulent message and a malicious attachment. The message aims to convince the target to execute the attached file, as this is how the threat would compromise their system. Other popular infection vectors are fake software updates and downloads, pirated copies of popular applications or media, torrent trackers, etc. The Cuba Ransomware would make sure to scan the files on the user’s system and begin locking them using an encryption algorithm. Files like images, documents, spreadsheets, videos, presentations, databases, archives, etc. will all be locked swiftly. Upon locking a targeted file, the Cuba Ransomware applies a new extension to its name – ‘.cuba.’ For example, if you had named an image ‘January-mist.mp4,’ the Cuba Ransomware will rename the file to ‘January-mist.mp4.cuba’ when it applies its encryption algorithm.
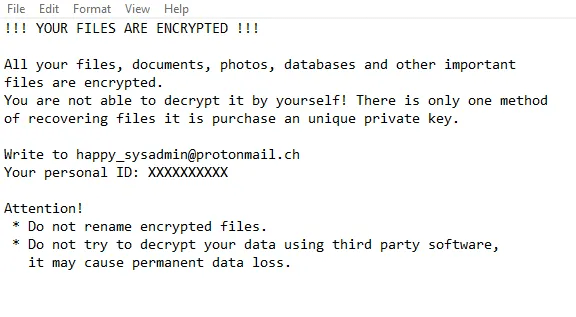
The Ransom Note
When the encryption process is completed, the Cuba Ransomware will proceed with the attack by dropping a ransom message on the victim’s desktop. The message in question is stored in a file called ‘!!! ALL YOUR FILES ARE ENCRYPTED !!!.txt.’ In the ransom note, the attackers state that unless the user pays up, they will not be able to recover their data. There is an email address provided for the victim – ‘happy_sysadmin@protonmail.com.’ This is how the authors of the Cuba Ransomware expect to be contacted for further information. There is no specific ransom fee mentioned, but it is likely that the attackers would require several hundred dollars in exchange for the decryption key you would need to unlock your files.
It is not advisable to attempt to contact the attackers or pay them the ransom fee they would demand. Most users who pay up never receive the decryption keys they need, so there is no point in rolling the dice. Instead, you should consider investing in a reputable antivirus solution that will clear your system of the Cuba Ransomware.

