CStealer
The CStealer threat is yet another strain of malware that aims at collecting information about its targets. The CStealer malware is designed to target systems running Windows exclusively. Infostealers like the CStealer threat tend to gather data from the host and then transfer it to the remote server of its operators.
Exfiltration Technique
Normally, the authors of threats of this class tend to use FTP or HTTP connection to siphon the gathered data. Another method that is gaining popularity is employing a Telegram bot to exfiltrate the information. However, in the case of the CStealer malware, the attackers have opted to use a rather interesting technique. The collected information is transferred to a MongoDB database set up by the threat’s authors. However, there are some issues with this method certainly. The attackers have hardcoded the administrator login credentials in the threat itself. This means that anyone who dissects the CStealer malware will be able to get their hands on the login credentials for the database that stores all the collected information.
Collects Login Credentials from Google Chrome Only
Usually, infostealers target a wide variety of data. However, the CStealer threat only gathers login credentials from the Google Chrome Web browser. This makes this threat very limited in its capabilities. Threats of this kind tend to collect data regarding instant messaging sessions, email clients, numerous Web browsers, FTP logins, etc. Malware researchers speculate that the CStealer threat may be an unfinished project, and it is likely that its authors may add more modules to this tool in the future.
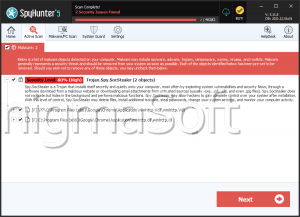
It is not yet known what the propagation methods employed in the distribution of the CStealer malware are. It is likely that the attackers are taking advantage of multiple infection vectors such as spam emails, bogus application updates, pirated content, etc. If you want to keep your system and your data protected from pests like the CStealer threat, you should consider downloading and installing a reputable anti-malware solution.