Crypto_Support Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 3 |
| First Seen: | January 10, 2022 |
| Last Seen: | January 13, 2022 |
| OS(es) Affected: | Windows |
The Crypto_Support also encountered as the Crypto Support, is a disruptive malware threat that falls into the ransomware category. It is designed to encrypt the files of its victims, making them both inaccessible and unusable specifically. Affected users will no longer be able to open their documents, pictures, photos, databases, archives, etc. The goal of the attackers is to then extort the victim in exchange for helping to restore the encrypted data.
As part of its invasive actions, the Crypto_Support Ransomware also modifies the names of the targeted files by appending '.CRYPT' to them as a new file extension. The malware also will create two new files on the infected device. One is used to display a ransom note in a pop-up window, while the other named 'README.txt' carries an identical message in text form.
Ransom Note's Overview
According to the instructions delivered via the ransom note, victims have just 10 hours to comply with the demands of the attackers. After that, all encrypted files on the system will supposedly be deleted. To prevent it, users are expected to pay a ransom of 0.003 BTC (Bitcoin). At the currency price of the cryptocurrency, the amount of the ransom is around $140. After transferring the funds to the provided crypto-wallet address, victims, apparently, will receive a decoder software tool and the necessary decryption key from the cybercriminals. The only way to contact the attackers that is mentioned in the note is via a Telegram account.
The full text of the note is:
'Do not close this message !!!
Hi, don't worry. All of your files have been encrypted.
To return your files, you need to send 0.003 bitcoin
to the address 1NNLcGozxxNmFypZB4rgnmvuCju2pxfAQQ
if within 10 hours there is no payment, all your files will be deleted …You can pay through various crypto-exchanges (Binance, Coinbase and others),
crypto exchanges or from your personal bitcoin wallet.After payment you will receive a decoder and an unlock key and all your
files will be unlocked.Do not try to unlock it yourself, you will only waste time, and after
10 hours all files will be deleted. A strong encryption method is used
for encryption.Communication after payment
telegram: @crypto_support_id_43274.'
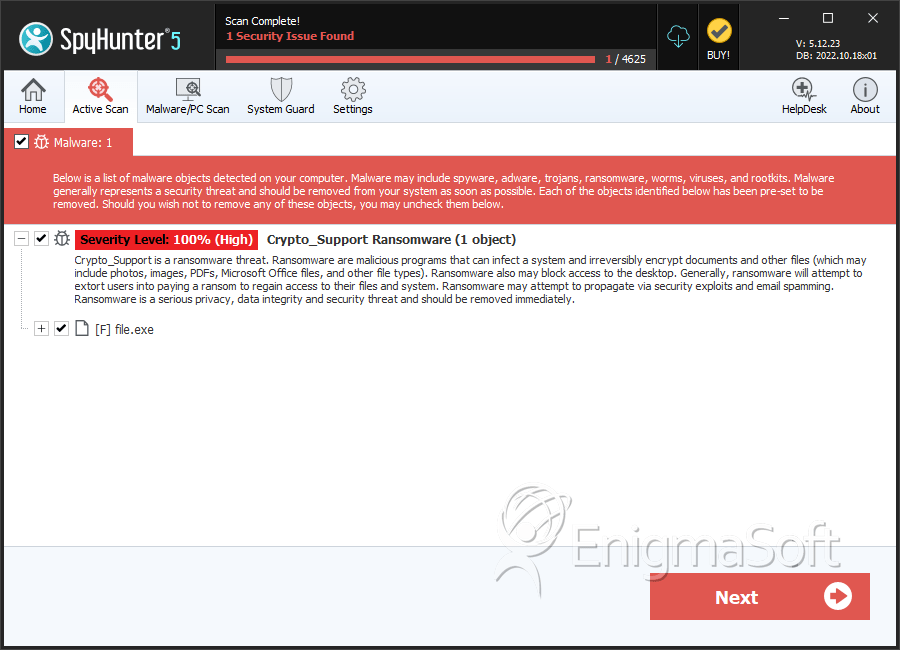
SpyHunter Detects & Remove Crypto_Support Ransomware