CryptoSpider Ransomware
The CryptoSpider Ransomware is an encryption ransomware Trojan designed to force computer users to pay large ransoms in exchange for their files, which the CryptoSpider Ransomware takes hostage. The CryptoSpider Ransomware is one of the many variants of HiddenTear, an open source ransomware platform that has spawned countless ransomware variants since its first release in 2015. PC users that take precautions against the CryptoSpider Ransomware and similar threats can avoid numerous problems.
Table of Contents
Analyzing the CryptoSpider Ransomware and Other HiddenTear Variants
The CryptoSpider Ransomware customizes the original HiddenTear open source ransomware platform. This ransomware platform was released to the public in August of 2015 by a programmer named Utku Sen. Since its release, this ransomware Trojan, which was released for proof of concept and educational purposes originally, has allowed con artists to create countless ransomware variants based on its code. The CryptoSpider Ransomware attacks have been centered on the United States or the United Kingdom, and attacks have been observed all around the world. Unfortunately, ransomware Trojans based on HiddenTear carry out an effective attack and cause irreparable damage to victims' files and data.
How the CryptoSpider Ransomware Executes Its Attack
The most common way in which the CryptoSpider Ransomware may be delivered is by attaching it as a corrupted file to a spam email message.The CryptoSpider Ransomware may arrive on the victim's computer in the form of a Microsoft Word file, or another type of file capable of executing corrupted macros and scripts. Once the victims open the file and allow the corrupted macro to be executed, the CryptoSpider Ransomware will be installed on their computers and begin its attack.
Once the CryptoSpider Ransomware enters a computer, it will begin to scan the victim's hard drives, affecting the files on removable memory devices connected to the infected computer and network shared directories as well. The CryptoSpider Ransomware will use a strong encryption algorithm to encrypt the victims' files, identifying the files affected by the attack with the addition of the file extension '.cspider' to the end of each affected file's name. The CryptoSpider Ransomware will target the user-generated files, which may include media files such as photos, sound, music, videos, and movies, as well as files associated with software such as Microsoft Word and Adobe Acrobat. The CryptoSpider Ransomware is identical to the countless other ransomware variants that are active currently, especially to the numerous other variants of HiddenTear that exist today.
How the Ransom Note of the CryptoSpider Ransomware is Delivered
One aspect of the CryptoSpider Ransomware that is fairly unique is that the CryptoSpider Ransomware also displays a lock screen apart from encrypting the victim's files. The CryptoSpider Ransomware lock screen contains a picture of an orange cat over a black background as a header. The text below this image reads as follows:
HACKED BY ./Mr.Gh0s7_C47
./Mr.Gh0s7_C47
ARE YOU SAFE?
Unlike more threatening lock screens, the CryptoSpider Ransomware message can be bypassed by using a keyboard shortcut, although the victim's files will remain encrypted and inaccessible.
Preventing and Dealing with a CryptoSpider Ransomware Attack
Unfortunately, once the files have been encrypted by the CryptoSpider Ransomware attack, they no longer become recoverable without the decryption key, which may cost hundreds or thousands of dollars to obtain it from the people responsible for the CryptoSpider Ransomware attack. This is why it is so crucial to take precautions against these threats. Handling all spam email messages and unsolicited email attachments with caution is the best policy to prevent these attacks. Furthermore, having file backups is essential in ensuring that your data is protected. If you can recover your files from a backup, then the people responsible for the CryptoSpider Ransomware attack lose any power over you. A proper security program is an essential part of recovering from the CryptoSpider Ransomware attacks and preventing these infections, and, if combined with a reliable backup method, it can provide a solid protection.
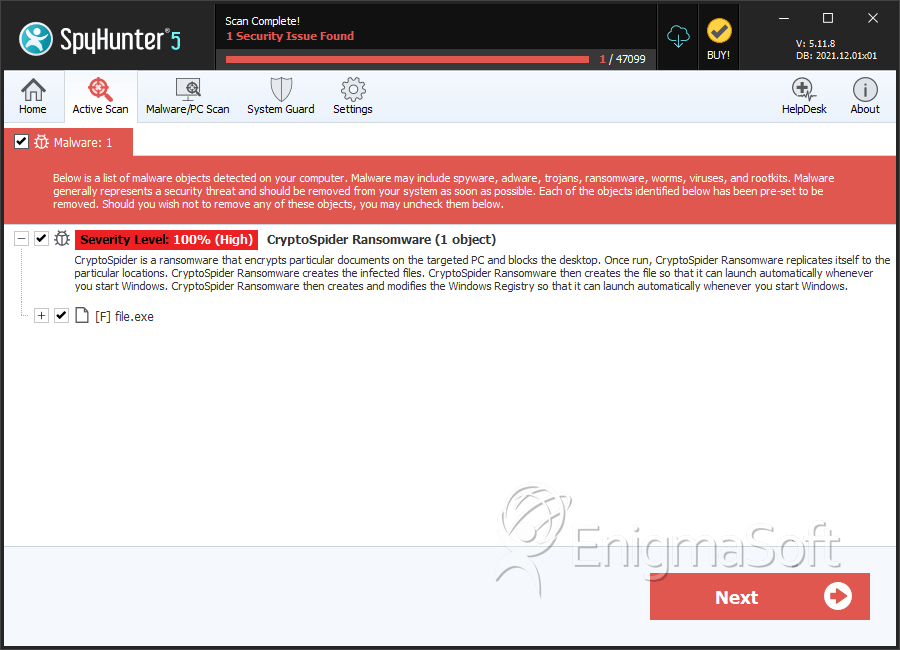
SpyHunter Detects & Remove CryptoSpider Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | b18c5af696e8847241e4c17230db36c9 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.