Crypto.com Email Scam
In today's digital age, exercising caution when dealing with unexpected emails is crucial. Cybercriminals often disguise themselves as legitimate entities to deceive users into divulging sensitive information or following fraudulent links. One such prevalent threat is the Crypto.com email scam, a phishing campaign identified by cybersecurity researchers.
Table of Contents
An Overview of the Crypto.com Email Scam
The Crypto.com email scam involves fraudulent emails designed to appear as notifications from Crypto.com, a reputable cryptocurrency platform. These messages falsely claim to enhance the security of recipients' NFT (Non-Fungible Token) accounts by offering additional security features.
Deceptive Tactics Used in the Scheme
The phishing emails prompt unsuspecting recipients to take action by clicking on a button labeled 'Set Up Now.' This action supposedly leads to setting up 2-factor authentication and an anti-phishing code. However, the link actually redirects users to a fraudulent website designed to mimic Crypto.com's interface.
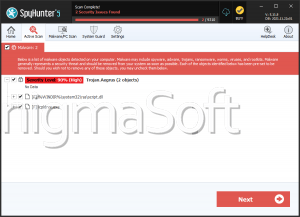
Risks and Consequences: The primary aim of the Crypto.com Email Scam is to deceive users into entering sensitive information, such as wallet details or recovery phrases. By doing so, fraudsters gain unauthorized access to victims' cryptocurrency wallets, enabling them to collect funds directly. The financial impact of such theft can be severe, as cryptocurrency transactions are typically irreversible and funds are challenging to recover once collected.
Recognizing and Avoiding Phishing Emails
Recognizing and avoiding phishing emails and tactics is crucial in today's digital landscape to protect personal information and financial security. Here are essential warning signs that can help users identify and steer clear of phishing attempts:
- Suspicious Sender Information: Phishing emails often come from addresses that mimic legitimate organizations but have slight variations or use domains that are not associated with the official company. Users should carefully scrutinize sender addresses for inconsistencies.
- Urgency or Threats: Phishing emails frequently try to induce a sense of urgency, urging recipients to take immediate action. They may threaten consequences if action isn't taken promptly. Legitimate organizations typically do not pressure customers in this manner via email.
- Unsolicited Attachments or Links: Emails containing unexpected links or attachments, especially from unexpected or suspicious sources, are common phishing tactics. These attachments may contain malware, and clicking on links can lead to fraudulent websites designed to steal login credentials or install malicious software.
- Poor Spelling and Grammar: Many phishing emails contain noticeable errors in spelling, grammar or syntax. Legitimate communications from reputable companies are usually well-written and professional. Users should be cautious of emails that exhibit these mistakes.
- Requests for Personal Information: Phishing emails often ask for particular personal information, such as passwords, Social Security numbers, credit card details or account credentials. Legitimate companies are unlikely to ask for such information via email. Users should verify any such requests through official channels before responding.
- Unusual Sender Behavior: Receiving emails from unfamiliar contacts or unexpected organizations, especially if they ask for personal information or prompt unusual actions, can indicate phishing attempts. Users should always verify the identity of the sender through known and trusted methods before taking any action.
- Mismatched URLs: Links in phishing emails may appear genuine at first glance but actually lead to spoofed or malicious websites. Users can hover over links to preview the URL destination before clicking. If you do not trust the URL or it does not match the claimed sender's official website, it should be avoided.
- Unusual or Unexpected Requests: Phishing emails may ask recipients to perform actions that seem unusual or unnecessary, such as confirming account details or making unsolicited payments. Users should independently verify such requests through official company websites or customer support channels.
In conclusion, phishing tactics like the Crypto.com email scam exploit trust and urgency to trick users into compromising their personal information and financial assets. By remaining vigilant and recognizing these warning signs, users can be better protected from falling victim to such fraudulent schemes. Always practice caution when dealing with unexpected emails and do not click on links or provide sensitive information unless absolutely certain of their authenticity.