Consumer Input
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 6,203 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 59,068 |
| First Seen: | July 3, 2014 |
| Last Seen: | May 24, 2026 |
| OS(es) Affected: | Windows |
While there is definitely harmful malware out there on the Internet, some of it poses significantly less danger than other malware and is harder to judge. While they differ in their functions, the effects they have on you and your machine can be from mildly frustrating to highly annoying.
Table of Contents
What’s the Purpose of Consumer Input?
Consumer Input is a product developed by Compete Inc. with the purpose of collecting people's feedback about services and products they are interested. The incentive for using Consumer Input is the chance for users to earn the privilege to enter sweepstakes and win cash prizes or gift cards. Consumer Input is, of course, not the first to try to provide paid research surveys with the intent of collecting user opinion. The goal of these kinds of research surveys is to obtain social information on users, although some may try to do so by shady means or with the help of adware programs. Even though Consumer Input may be a legitimate program, malware researchers have classified it as a PUP (Potentially Unwanted Program).
The shape of Consumer Input comes as a browser plug-in for the most popular browsers (like Internet Explorer, Mozilla Firefox and Google Chrome) for Windows XP, Vista, 7 and Windows 8 operating systems. While installation may in some rare cases be without the user's consent, that is not most often the case. What a vast majority of the users on the Internet fail to notice when installing new programs on their machine is the skillfully camouflaged option to install additional software, which would already be checked off with a mark (in our case Consumer Input), in addition to the one you personally want (most often a freeware or shareware product). Proof of that you can even find in their own description of how to remove Consumer Input if you no longer desire to use it - "In cases where the Software is integrated into a partner's application (such as a toolbar), you can opt-out of the Compete research panel, either by removing the partner application, or by disabling the collection features of the application if the partner has provided such functionality".
Make a Decision If You Should Keep It
Consumer Input may also be categorized as adware, since what Consumer Input does is that it records your browsing patterns. What you need to know is that, even though the creators of Consumer Input have stated that the information gathered this way will not be sold or used to benefit third parties, it is still possible for that information to be leaked or compromised. Even Compete Inc. confess themselves, that if you have an installation that dates to before February 1, 2010, then your sensitive information (credit card numbers, financial account numbers, security codes and expiration dates, usernames, passwords and Social Security numbers) may have been exposed.
Consumer Input makes use of browser cookies so that websites, which you visit, can recognize you. Consumer Input may also use cookies to link data, collected through the help of the adware and without it, to your profile
Once you have installed Consumer Input on your machine, Consumer Input will display the typical behavior of the common adware – a barrage of image, pop-up, in-text and in search advertisements on the websites that you are visiting. What Consumer Input also does is that Consumer Input provides non-personal information, such as search and URL history to advertising affiliates in order to improve advertisement relevance.
It seems that the creators of Consumer Input are also offering a mobile application version of their software. The reviews on the page are from both kinds – positive and negative. Although, comments about compromised personal data are almost entirely lacking, the most common gripe is that people using the application never get to receive their rewards.
In its nature, adware is not designed to be hard to remove. You can get rid off of Consumer Input by following the instructions on the official Consumer Input website. The procedure is relatively uncomplicated, and the process seems like the legitimate one that is used for the removal of other regular software. Not been sure about the genuineness of the steps described on the official website, then you can insure yourself by using one of the numerous computer protection programs on the Internet.
Aliases
11 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| Ikarus | PUA.Compete |
| GData | Win32.Application.Agent.VGHEAB |
| McAfee-GW-Edition | Artemis!PUP |
| Sophos | Generic PUA OJ (PUA) |
| Avast | Win32:Malware-gen |
| McAfee | Artemis!A9C69837EC78 |
| McAfee | Artemis!42E77A08ED9B |
| AVG | Generic.381 |
| McAfee-GW-Edition | BehavesLike.Win32.BadFile.th |
| McAfee | Artemis!0F3433C84718 |
| Symantec | Infostealer.Consmiper |
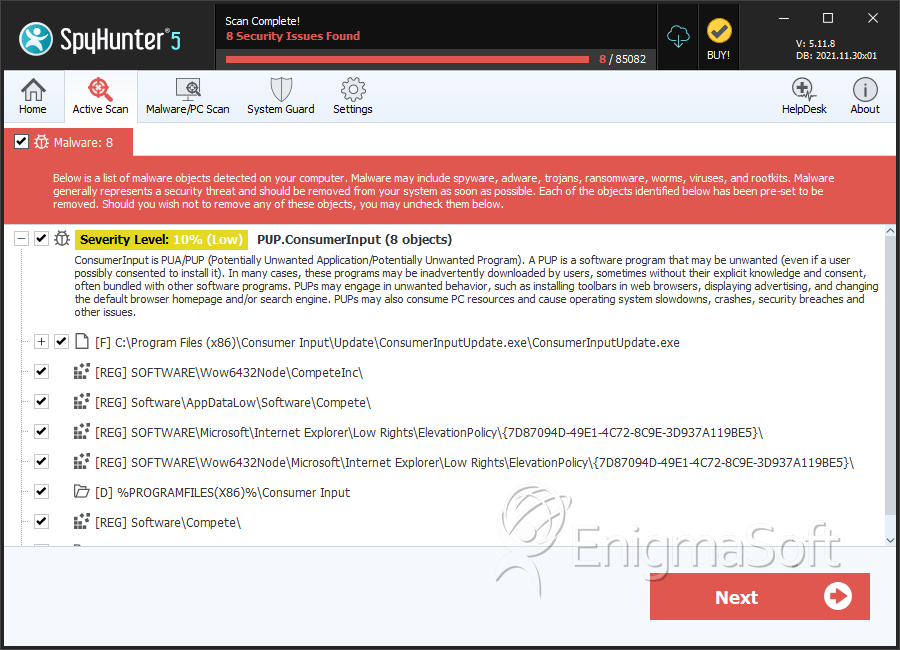
SpyHunter Detects & Remove Consumer Input
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | ConsumerInputUpdate.exe | 7b110c27e90217ff3bd49cef739a2e1d | 364 |
| 2. | dca-bho.dll | 6a967ae8da20832f3d3c959181deda83 | 104 |
| 3. | cinput.exe | bc308733568e737020e57b7b1f728cd2 | 67 |
| 4. | c10w.exe | c761c275bac28f9e02d638cf3d372864 | 25 |
| 5. | compete.exe | a9c69837ec78126315335e6814781730 | 3 |
Registry Details
Directories
Consumer Input may create the following directory or directories:
| %LOCALAPPDATA%\Consumer Input |
| %PROGRAMFILES%\Consumer Input |
| %PROGRAMFILES%\Setup Support for Consumer Input |
| %PROGRAMFILES%\Setup Support for Consumer Input DH |
| %PROGRAMFILES(X86)%\Consumer Input |
| %PROGRAMFILES(X86)%\Setup Support for Consumer Input |
| %PROGRAMFILES(X86)%\Setup Support for Consumer Input DH |
| %UserProfile%\Local Settings\Application Data\Consumer Input |
| %appdata%\Compete\Consumer Input |
Analysis Report
General information
| Family Name: | PUP.ConsumerInput |
|---|---|
| Signature status: | Self Signed |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
1035aeb5fa6f8c281ab85ae8012551d4
SHA1:
615996356bac12f01507b13c3e903ffc29e6ded4
SHA256:
AC6E3CA26C2808C9F7E571D4895CAF643443C145590C0B974CD15EA721FACA85
File Size:
62.34 KB, 62336 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File has exports table
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name | Compete, Inc. |
| File Description | This plugin is able to read data from registry. |
| File Version | 3.2.0.208 |
| Internal Name | ci-npapi.dll |
| Legal Copyright | (c) Compete, Inc. All rights reserved. |
| M I M E Type | application/x-consumer-input-npapi |
| Original Filename | ci-npapi.dll |
| Product Name | Consumer Input Chrome plugin |
| Product Version | 3.2.0.2925 |
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Compete Inc | VeriSign Class 3 Code Signing 2010 CA | Self Signed |
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 286 |
|---|---|
| Potentially Malicious Blocks: | 0 |
| Whitelisted Blocks: | 272 |
| Unknown Blocks: | 14 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
| Anti Debug |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\615996356bac12f01507b13c3e903ffc29e6ded4_0000062336.,LiQMAxHB
|