Conficker.C
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 50 % (Medium) |
| Infected Computers: | 1,180 |
| First Seen: | November 30, 2010 |
| Last Seen: | April 17, 2023 |
| OS(es) Affected: | Windows |
Conficker.C is a new variant of the Conficker worm and may be a greater threat than its predecessor. Conficker.C is expected to launch its attack on April 1st. The Conficker.C worm will disable the users' Windows Automatic Update, prevent the user access to the Windows Security Center, block DNS queries, delete all system restore points, as well as prevent the user access to security websites. The Conficker family of worms have been very dangerous and harmful to users' PC's. The new Conficker.C may prove to be even more damaging. It is essential at this point to keep all of your software updated in addition to verifying that your antivirus or antispyware applications are running with the latest definitions applied.
It is essential at this point to keep all of your software updated in addition to verifying that your antivirus or antispyware applications are running with the latest definitions applied.
Conficker.C is expected to contact various domains so it may obtain a set of instructions to carry out. Researchers have found the date of April 1st hard coded into Conficker.C as the date that these actions may take place. The domain generation algorithm has been slightly changed from previous versions of Conficker which makes Conficker.C much different. Below is a list of few of the domains that Conficker.C may contact on April 1st.
aaak.com.ai
aaax.com.hn
aaaxvt.co.ke
aabbb.com.uy
aabe.ac
aabfkx.com.co
aabk.lu
aacgebuee.ly
aach.dk
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Fortinet | W32/Conficker.FZ!worm.im |
| Ikarus | Trojan.Win32.Genome |
| AhnLab-V3 | Worm/Win32.Conficker |
| Sophos | W32/Confick-F |
| McAfee-GW-Edition | Heuristic.BehavesLike.Win32.Suspicious-PKR.G |
| AntiVir | Worm/Conficker.Z.17 |
| DrWeb | Trojan.Click1.38217 |
| F-Secure | Worm:W32/Downadup.BR |
| Kaspersky | Trojan.Win32.Genome.moke |
| Fortinet | W32/Kido.IH!worm |
| AhnLab-V3 | Win32/Kido.worm.166503.B |
| AntiVir | Worm/Conficker.Z.58 |
| DrWeb | Trojan.Click2.12841 |
| Kaspersky | Trojan.Win32.Genome.hkck |
| McAfee | Artemis!A312C8B1ADB4 |
SpyHunter Detects & Remove Conficker.C
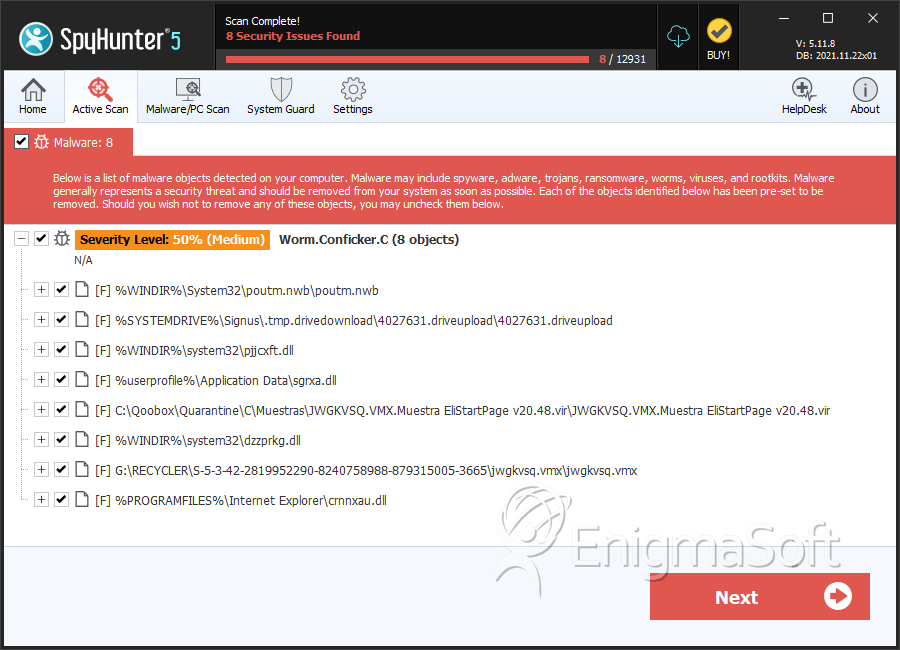
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | poutm.nwb | 04199a5b981fd5a3d846d3f9d4c1d574 | 484 |
| 2. | 4027631.driveupload | 93d305c9094278e3e6da70e40b543c28 | 24 |
| 3. | JWGKVSQ.VMX.Muestra EliStartPage v20.48.vir | 393e2e61ff08a8f7439e3d2cfcb8056f | 13 |
| 4. | jwgkvsq.vmx.vir | 9c09418c738e265a27e6c599f43d86ab | 12 |
| 5. | jwgkvsq.vmx | 67241ac88d798ccd90a6f49f481ac26c | 12 |
| 6. | pjjcxft.dll | ae7709bd2b77d2f40aa8f37c1126d8b1 | 12 |
| 7. | jwgkvsq.vmx | d987a9af709bfd188071aa3f5e027aac | 6 |
| 8. | jwgkvsq.vmx | d2eabe15257a453416efa18992d1edbd | 5 |
| 9. | crnnxau.dll | 76cfe416f735588146aaa3b4f8d0907a | 5 |
| 10. | lmmtvk.dll | 84ef65fbf6e58fc735e867031bbb8d02 | 4 |
| 11. | lccyr.dll | 95ad430abca3da496600f764c120683c | 4 |
| 12. | khgixdc.dll | b081022fc581decf4c8640dbc74a9198 | 3 |
| 13. | lvxan.dll | 59fe65fad4849c95ed538475c1f707cf | 3 |
| 14. | hzcakuc.dll.78034401.mwt | 9645f61e0913a58a29ecfcce940136fe | 2 |
| 15. | jyuzfa.dll | fb7ba7e14bafdc97724ffb66d39c2246 | 2 |
| 16. | njyqxzt.dll | 023bc7137676d46c114483b11853131e | 2 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.