Comrade Circle Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 4 |
| First Seen: | October 10, 2016 |
| Last Seen: | April 11, 2022 |
| OS(es) Affected: | Windows |
The Comrade Circle Ransomware is an encryption Trojan that uses a fake 'Windows Update' screen to hide its activity. The Comrade Circle Ransomware behaves similarly to the Fantom Ransomware and is spread the same way - spam emails loaded with a Trojan dropper in the form of a macro-enabled Microsoft Word file. Computer users may be urged to enable macro for the corrupted document by being shown a scrambled text and a banner that says 'Please, enable macro to read the text below.' The Comrade Circle Ransomware relies on the user's interaction to launch, and users should avoid spam email from unknown senders.
The 'Configuring Critical Windows Updates' Screen Leads to the Comrade Circle Ransomware
As stated above, the Comrade Circle Ransomware uses a fake 'Windows Update' screen to hide the encryption procedure. When the Comrade Circle Ransomware is initiated the user is shown a 'Configuring critical Windows Updates' message on the screen. The 'Configuring critical Windows Updates' notification by the Comrade Circle Ransomware disappears when the encryption process is complete. The Comrade Circle Ransomware is known to lock data in the default user's library, local drives and network shares that are not password protected. Researchers note that the Comrade Circle Ransomware can encode standard data containers used to store text, images, video, presentations, audio and databases. The Comrade Circle Ransomware may lock files in the following formats:
.3GP, .7Z, .APK, .AVI, .BMP, .CDR, .CER, .CHM, CONF, .CSS, .CSV, .DAT, .DB, .DBF, .DJVU, .DBX, .DOCM, ,DOC, .EPUB, .DOCX .FB2, .FLV, .GIF, .GZ, .ISO .IBOOKS,.JPEG, .JPG, .KEY, .MDB .MD2, .MDF, .MHT, .MOBI .MHTM, .MKV, .MOV, .MP3, .MP4, .MPG .MPEG, .PICT, .PDF, .PPS, .PKG, .PNG, .PPT .PPTX, .PPSX, .PSD, .RAR, .RTF, .SCR, .SWF, .SAV, .TIFF, .TIF, .TBL, .TORRENT, .TXT, .VSD,.WMV, .XLS, .XLSX, .XPS, .XML, .CKP, ZIP, .JAVA, .PY, .ASM, .C, .CPP, .CS, .JS, .PHP, .DACPAC, .RBW, .RB, .MRG, .DCX, .DB3, .SQL, .SQLITE3, .SQLITE, .SQLITEDB, .PSD, .PSP, .PDB, .DXF, .DWG, .DRW, .CASB, .CCP, .CAL, .CMX, .CR2.
What does Stalin and the Comrade Circle Ransomware Have in Common
The Comrade Circle Ransomware is named after the picture it uses as a custom wallpaper. The image is a representation of a long gone political leader under—Joseph Vissarionovich Stalin depicted as a saint from the Eastern Orthodox Church. Analysts suspect that the picture of Stalin may be used to put the Comrade Circle Ransomware in the same category as other Ransomware aimed at Russian-speaking users like the RAA Ransomware and the Kozy.Jozy Ransomware. Computer users that suffered an attack by the Comrade Circle Ransomware will find the '.comrade' suffix appended to modified files. For example, 'up_the_ladder.png' will be converted to 'up_the_ladder.png.comrade' and its content will be unavailable. The ransom note is delivered via 'RESTORE-FILES![random characters].txt' placed on the desktop. The message within 'RESTORE-FILES![random characters].txt' reads as follow:
'YOU FILES ARE ENCRYPTED by Comrade Circle!
You personal ID [string of random characters]
YOU HAVE 3 OPTIONS!
Option 1 = purchase decrytpion software. (if you need files your files back and have money)
1. Send donation of 2.04970001 btc to wallet [a string of random characters]
2. Send an email to recoverfiles@mail2tor.com with you personal id, and you will recieve the decryption software
3. Decrypt you files.
If you dont get answer in 4 hours, or email is blocked by evil anti virus companies:
Register here: http://bitmsg.me, Once you have done that, Write to adress BM-2cTivRoWe5eXdZAt8PqxTJ6tqaQwoaNt6tcontact with you email and personal ID'
The Comrade Circle Ransomware Offers Choices if You Want a Decryptor for Free
Option 2 and 3 suggest the victim send as much money as possible to the con artists and include an invitation to join them. The makers of the Comrade Circle Ransomware claim to deliver 50% of their profit to people under the poverty bar. We suspect that their intentions are less than altruistic. Researchers note that the makers of the Comrade Circle Ransomware may be trying to create a network of affiliates. The crooks behind the Comrade Circle Ransomware offer a percentage of their profits to potential partners and help in the development of new variants and distribution methods. It is not a good idea to deliver payment and participate in the distribution of cyber threats.
Malware researchers might be able to crack the Comrade Circle Ransomware; therefore, you should backup the encrypted data and keep an eye on the Internet for a free decryptor. Meanwhile, you can use offline backups, copies on the cloud (for example Google Drive and Dropbox) and archives on removable HDD and SDD to recover your data structure. Keep in mind that you will need to clean your machine with a reputable anti-malware suite that can eliminate the Comrade Circle Ransomware.
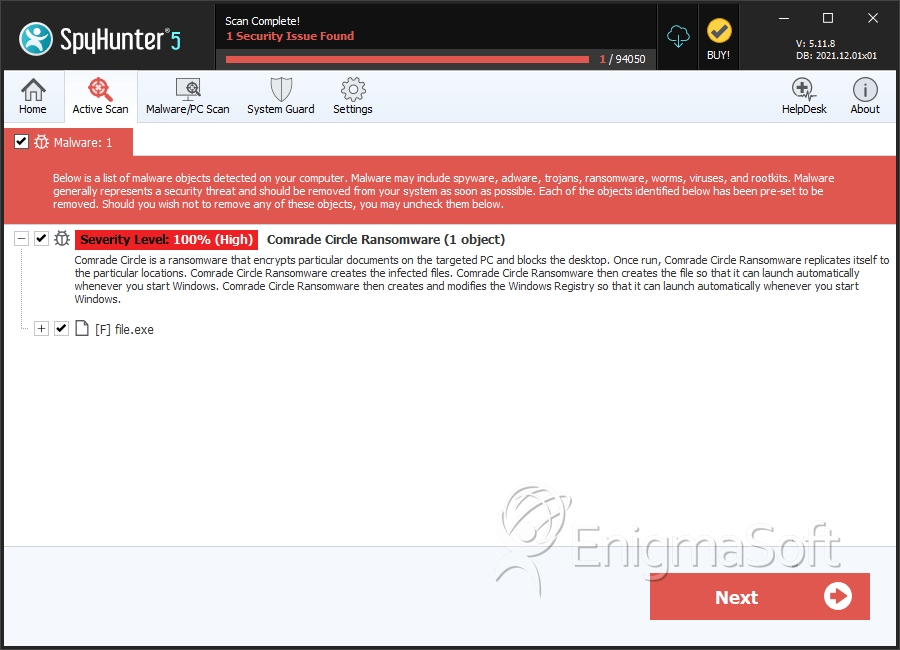
SpyHunter Detects & Remove Comrade Circle Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 09963f553929ef4cced4c44e8ec4e9c2 | 2 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.