CometSystems
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
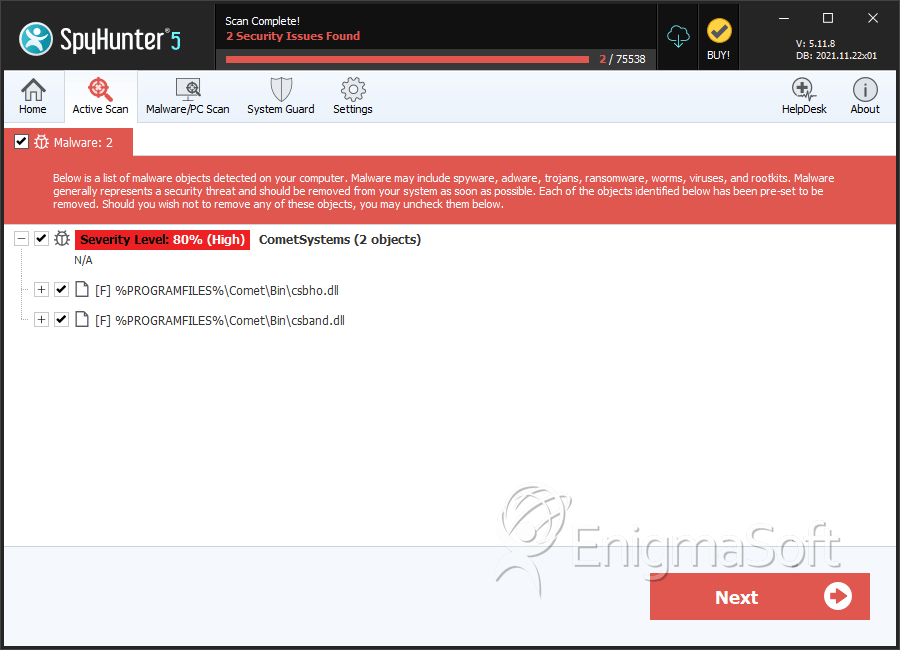
| Threat Level: | 80 % (High) |
| Infected Computers: | 4 |
| First Seen: | January 23, 2011 |
| OS(es) Affected: | Windows |
Comet Systems was a company that, until Comet Systems was bought in 2004, produced some programs that were supposed to modify or enhance the mouse pointer on Windows computers. In particular, Comet Systems was responsible for a program called Comet Cursor, which allowed users to change the mouse pointer to a wide variety of different styles of arrows, images, or animations. Over time, it became apparent that Comet Cursor (referred to within its program files in Windows as Comet Systems) behaved in ways that were typical of adware or spyware.
Table of Contents
What Made Comet Systems Popular and Widely-used
Comet Cursor was at the height of Comet Systems' popularity from the late 1990's to 2000 or 2001. Initially, Comet Cursor was just a free program that anyone can download, in order to change the mouse pointer on their computer to something cute or fun. Because Comet Cursor offered licensed content, like cursors based on popular characters (including Hello Kitty and Dilbert) and even images of celebrities, Comet Cursor became a very widely-used program. Comet Cursor also offered code that could be added to websites so that whenever someone visited the site, their cursor would change to something specific to the site while they viewed it. So, in addition to individuals downloading and using Comet Cursor on their own PC's, thousands of national and international businesses – and even political campaigns – added specialized cursors from Comet Systems to their websites.
However, the way that Comet Cursor worked within a web browser made Comet Cursor intrusive and suspicious. In order to change the cursor temporarily while someone viewed a particular website, Comet Cursor used an ActiveX program. So, if you were to visit one of the sites that used a special cursor, you would need to install the ActiveX program in order for the cursor change to work. Depending on the settings used within Internet Explorer for handling ActiveX Controls, Comet Cursor could be installed either with one click, or – in a disturbingly large number of cases – without any agreement or acknowledgement from the user at all.
More Serious Problems with Comet Cursor
So the problem with Comet Cursor was that they were doing a few things with Comet Cursor that they had not properly disclosed to users of the software; and with time, as Comet Cursor evolved and changed, that problem only grew. Initially, aside from the ActiveX problem, the issue was that Comet Cursor had no privacy policy for Comet Cursor, and did not notify its users that Comet Cursor was sending information about them back to Comet Cursor. In particular, Comet Cursor identified each computer it was downloaded onto with a unique number, and then whenever a Comet Cursor user changed which cursor design they were using, that information would be communicated to Comet Cursor. Furthermore, Comet Cursor was communicating with Comet Cursor and receiving program downloads and updates without the knowledge or consent of its users. Eventually, these updates allowed Comet Cursor to morph into something very different and much worse than it initially was, while remaining installed.
With time, Comet Cursor added a browser toolbar to Comet Cursor, as well as the capability to generate targeted pop-up advertisements and to create desktop shortcuts to advertisements. At the same time, Comet Cursor made advertising deals with some companies, offering to place advertisements within search results from the Comet toolbar, in exchange for getting paid a certain amount of money per click. Comet Cursor also began to be bundled along with every download of RealPlayer, which meant that a lot of unsuspecting PC users suddenly found that they had installed an adware toolbar.
Why Comet Cursor Died out, and Why it Should be Avoided
Uninstalling Comet Cursor was a nightmare, because of the huge number of changes it made to the PC Comet Cursor was installed on, including a shocking number of changes to the registry. The uninstall options for Comet Cursor were shoddy and incomplete, often leaving components of the adware behind even after Comet Cursor was supposed to be removed. To make things worse, many users started to report that Comet Cursor wasn't showing up in the Add/Remove programs list in the Control Panel, which meant that in some cases, there was no way to remove Comet Cursor without some kind of security software. Needless to say, things didn't go well for Comet Cursor, and they don't distribute Comet Cursor anymore. The Comet Cursor website no longer exists, and the domain registration has been allowed to expire.
It is entirely likely, given the former popularity of Comet Cursor's products, that Comet Cursor can still be downloaded from third-party sites. PC users should avoid downloading Comet Cursor, because Comet Cursor is extremely disruptive while it is installed, and Comet Cursor is very difficult to remove completely. Most security software prevents Comet Cursor from being installed, but if you do install Comet Cursor, be assured that you'll want a good anti-spyware program in order to remove Comet Cursor later.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| AVG | Adware Generic.DT |
| AntiVir | ADSPY/Comet.V.3 |
| BitDefender | Adware.Comet.Systems.N |
| Kaspersky | not-a-virus:AdWare.Win32.Comet.v |
| ClamAV | Adware.Comet-9 |
| CAT-QuickHeal | AdWare.Comet.v (Not a Virus) |
| Panda | Adware/Comet |
| Fortinet | Adware/CometCursor |
| Sunbelt | Comet Cursor |
| AVG | Adware Generic.CLV |
| Microsoft | CometSystems (threat-c) |
| Prevx1 | Malware |
| AntiVir | ADSPY/Comet.AK |
| eWido | Adware.Comet |
| BitDefender | Adware.Comet.9 |
SpyHunter Detects & Remove CometSystems
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | csbho.dll | 6593131457424a5eff23ac8d4b15eba9 | 2 |
| 2. | csband.dll | e4351e992c9b566b5a8e9ebaef568ce0 | 2 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.